How do you detect a phone call? According to TV shows and movies, you just have to keep someone talking long enough for a detective to locate him.
While this overused rope can add some tension when paired with a timer that slowly marks, it doesn't really fit.

Before computers, there were switchboards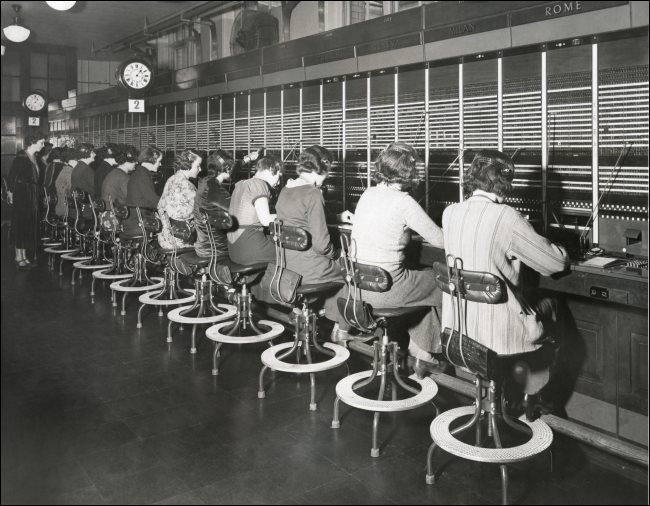
Before the global telephone system was computerized, calls were routed through a network of physical switches by an army of human operators. Traditionally, these operators were almost exclusively women (although the first were teenagers who were known for their rude language and unprofessional behavior).
When a call came in, the operator routed it to its destination, of course connecting it to a separate port on a plugboard. Later, however, automation gradually began to exert its influence.
In the late 19th century, the Almon Strowger company invented the world's first electromechanical step switch. Patented in 1891, this device allowed users to call others directly. While it took several decades for this invention to achieve commercial success, it eventually transformed a once-human task into one performed by the cool precision of a machine. This set the tone for the next century.
Over time, the technology used to automatically make calls has gradually become more sophisticated. Eventually, as the phones moved from the office and the payphone at home, it could handle larger quantities. People could make calls over longer distances. But the basic principles remained the same.
In these previous eras, the monitoring κλήσεων ήταν μια εμπλεκόμενη διαδικασία. Χωρίς μεταδεδομένα που δημιουργούνται από υπολογιστή, η ευθύνη ήταν στην τηλεφωνική εταιρεία. Έπρεπε να παρακολουθήσει τη διαδρομή περιέλιξης μιας σύνδεσης σε διακόπτες και ανταλλαγές για να ανακαλύψει την προέλευσή της. Στη συνέχεια, η τηλεφωνική εταιρεία το παρέδωσε στην επιβολή του νόμου.
This was a time consuming process, requiring a negotiator or a police officer to keep the call active as long as possible. If the suspect closed, the game was lost for good. They had to either try again or find another way to catch the criminal.
This is probably where Hollywood gets its inspiration. Of course, they get a little poetic leave. Call tracking inevitably took more than a minute or two to complete. But technical accuracy is often sacrificed on the altar of agony.
Call logs are now stored digitally

Eventually, computerization took place in the telecommunications sector. Gradually, he took on tasks, such as routing calls, previously performed by human or mechanical operators. This trend was momentary. On the consumer side, it has enabled new facilities such as caller ID and call waiting.
In terms of law enforcement, it simplified investigations. Calls no longer had to be detected manually on switches. Nor did law enforcement have to monitor calls in real time - they could just see the metadata generated by the calls.
The word metadata means "data about data". In telecommunications, metadata includes things like where a call came from and its destination, as well as the type of telephone (mobile, landline or payphone) used.
Because these files are essentially small chunks of text that can easily be stored in a database data, phone companies can keep them for a long time. This allows investigators to obtain information about a call months – or even years – after it was made.
The exact duration varies considerably between telephone companies and each has its own standards. There are also differences depending on the type of telephone and the telephone program used.
In 2011, documents leaked by the FBI revealed that some telephone companies kept records of postpaid subscriptions significantly more than those made from prepaid or burner phones, which are often used by criminals.
Because call records are now stored digitally, investigators can also obtain them access to files with a level of immediacy previously not possible. Once all the legal documents are created, it's just a matter of looking up a file in a database.
Law enforcement does not have to wait
It is easier than ever for law enforcement to detect regular phone calls. You can thank the computer system for this.
Of course, there are other ways in which criminals can communicate and avoid the thin blue line, such as with VPNs and encrypted voice applications. These cases will not be resolved so easily - even if you wait a few minutes to locate the call.



"Poetic license" my friend. "Permission".
Thank you George