ThreatBox is a standard and controlled attack platform based on functional Linux.
It started as a collection of scripts, established itself as a virtual machine, existed as codes for building a Linux ISO, and has now turned into a series of playbooks.
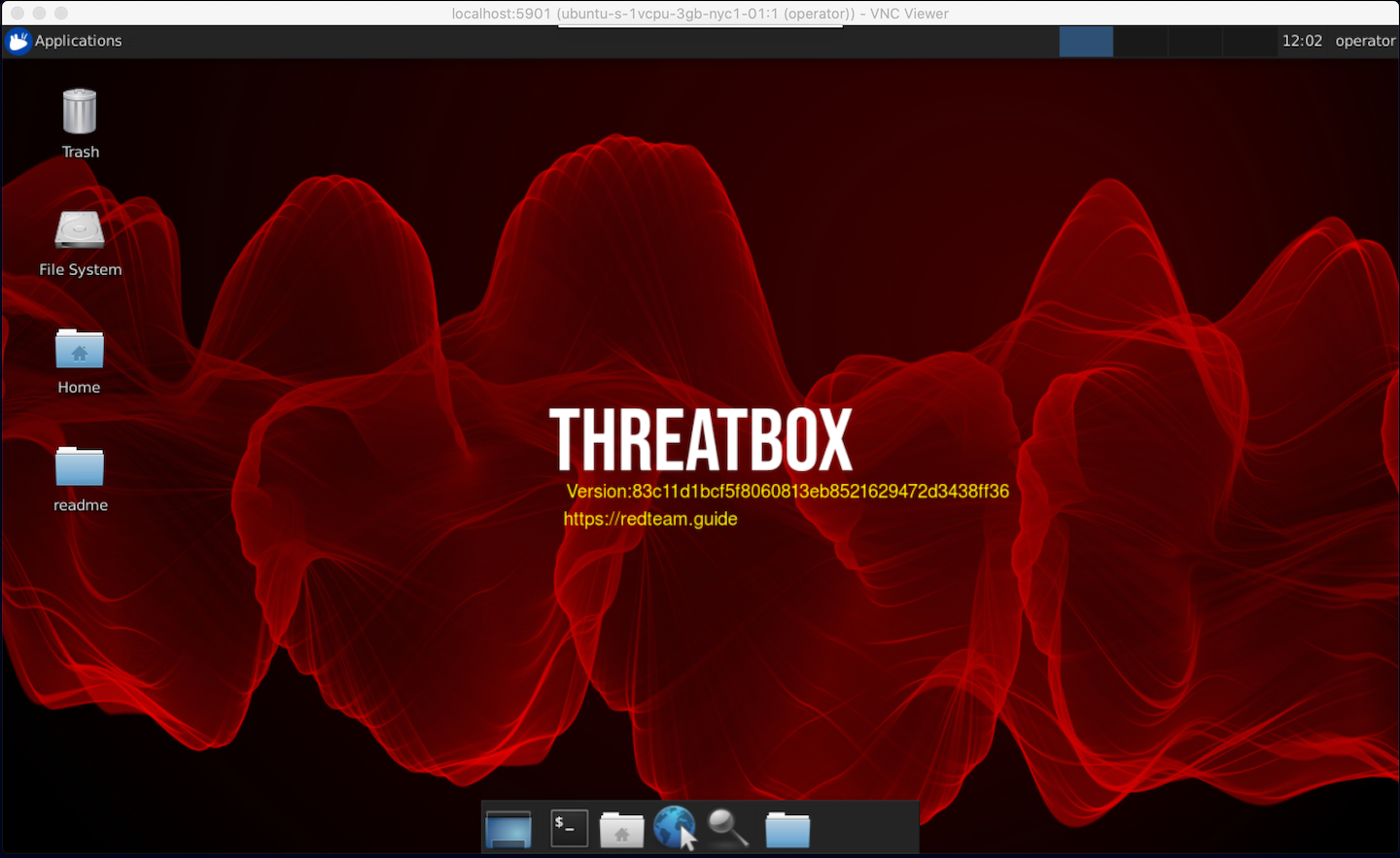
The project is designed to be used as a start-up process for creating, managing and using a standard attack platform for penetration testing.
Details on the concept of a Standard Attack platform can be found in the Red Team book Development and Operations – A practical guide, written by Joe Vest and James Tubberville.
Specifications
- Basic tools ansible roles
- Adjustments designed to facilitate security screening
- Variable list for adding or removing git repositories, operating system packages, or python drives. (ancbox.yml)
- Automatic SSH port switching. Deployment starts on port 22, but reconfigures it system destination to the desired SSH port using the ansible_port variable in the yml
- Download and collect many .net tools (eg SeatBelt.exe from Ghostpack https://github.com/GhostPack/Seatbelt)
- Most pythonprojects were installed using pipenv. Use the pipenv shell in the directory to access. See address https://realpython.com/pipenv-guide/ for instructions for use of pipenv
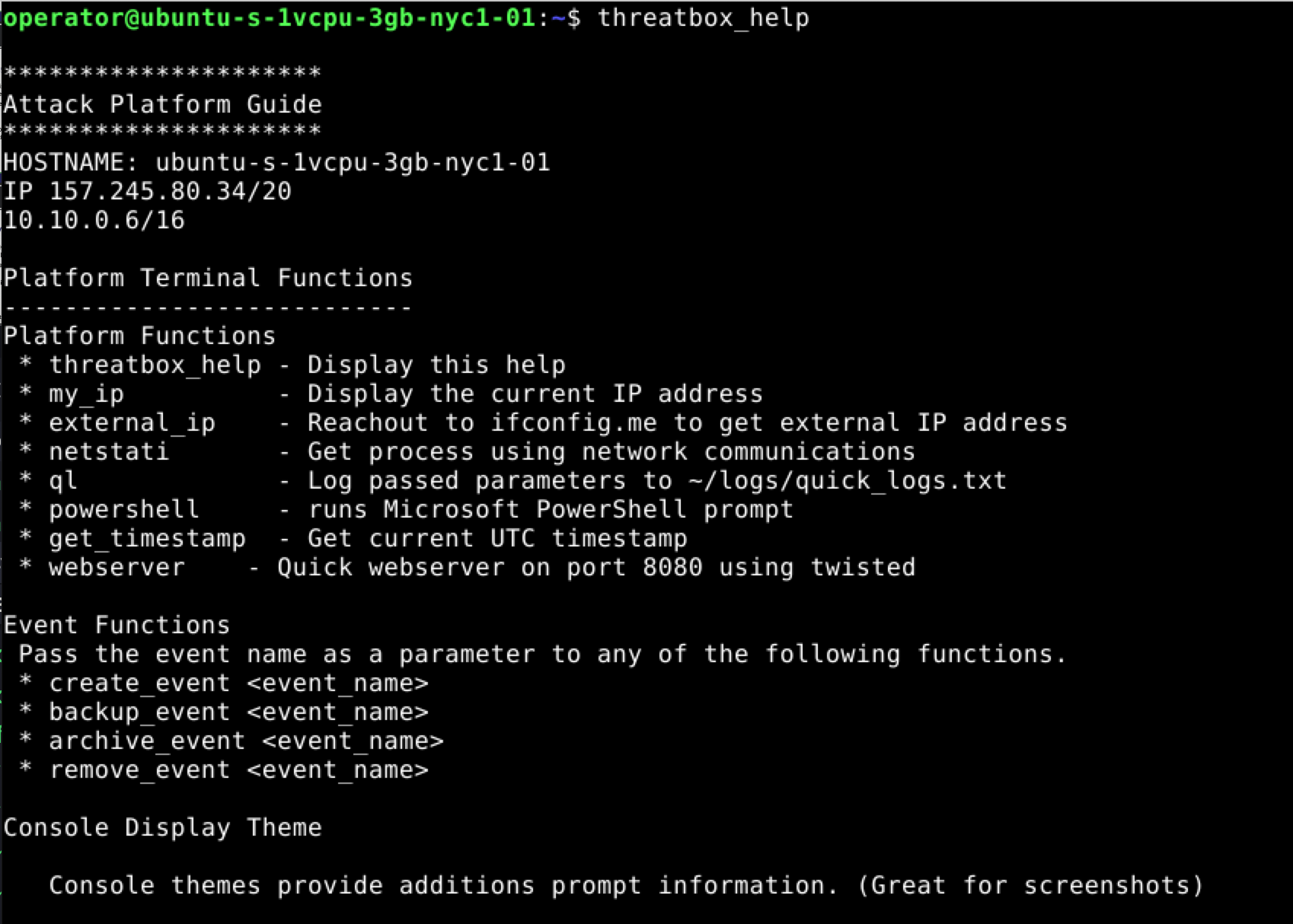
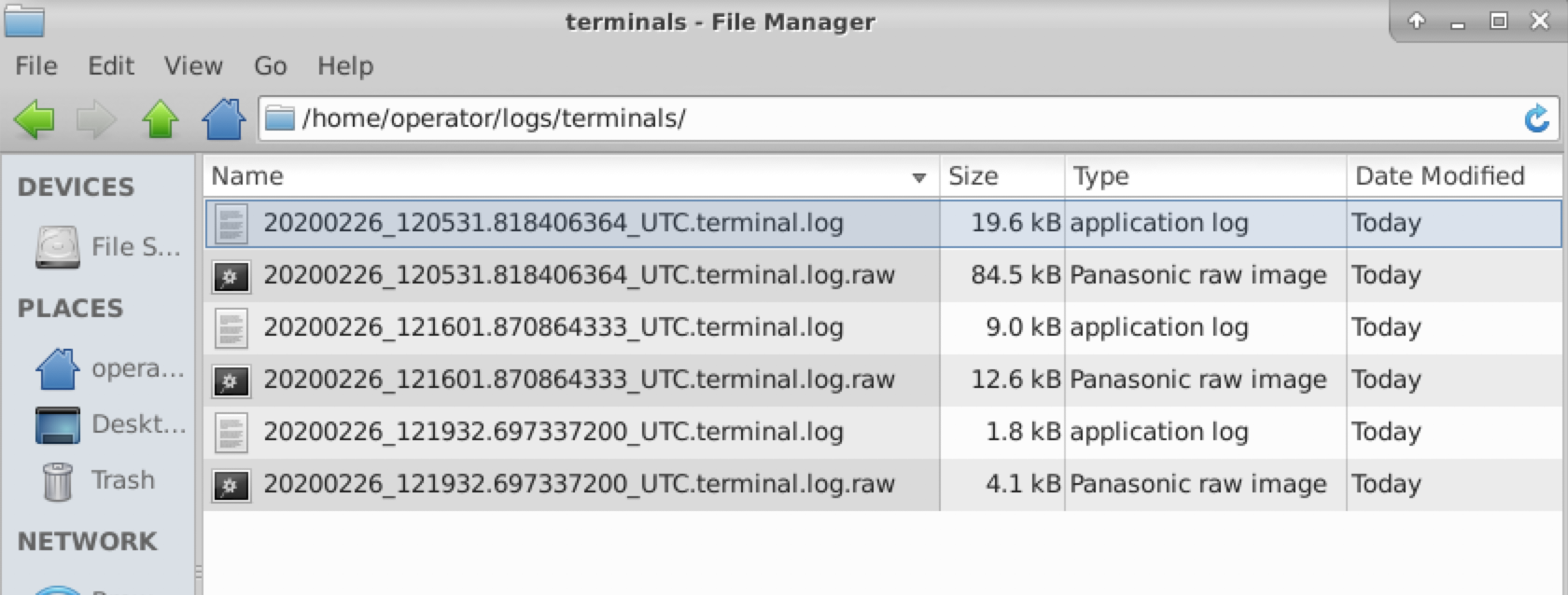
Application snapshots
![]()
Information on installing and using the program, you will find here.





