Intelspy Perform automated network authentication scans to collect network information.

IntelSpy is one tool εντοπισμού πληροφοριών πολλαπλών νημάτων που εκτελεί αυτοματοποιημένη σάρωση υπηρεσιών δικτύου. Πραγματοποιεί σάρωση ανίχνευσης ενεργών κεντρικών computers, σάρωση θύρας, σάρωση υπηρεσιών, σαρώσεις περιεχομένου ιστού, brute-force, λεπτομερείς αναζητήσεις εκμεταλλεύσεων εκτός connectionand others.
The program will also start further scans for each service detected using a large number of different tools.
Specifications
- It scans many targets in the form of IP addresses, IP bandwidth (CIDR note) and solvable host names.
- It scans the targets at the same time.
- Detects servers in IP range network (CIDR).
- Customizable port scan profiles and service enumeration commands.
- Creates a directory structure for collecting results.
- Records commands executed.
- Creates Shel with commands that will be executed manually.
- Exports important information in txt and markdown format.
- Stores data in a database data SQLite.
- Creates an HTML report.
Requirements
- Python 3
- colorama
- toml (https://github.com/toml-lang/toml)
- seclists
- curl
- enum4linux
- gobuster
- nbtscan
- no one
- Nmap
- onesixtyone
- oscanner
- smbclient
- smbmap
- smtp-user-enum
- Snmpwalk
- sslscan
- svwar
- tnscmd10g
- whatweb
- wkhtmltoimage
- pandoc
- Hydra
- jellyfish
- wpscan
- ldapsearch
- patter
pip3 install -r requirements.txt sudo apt install seclists
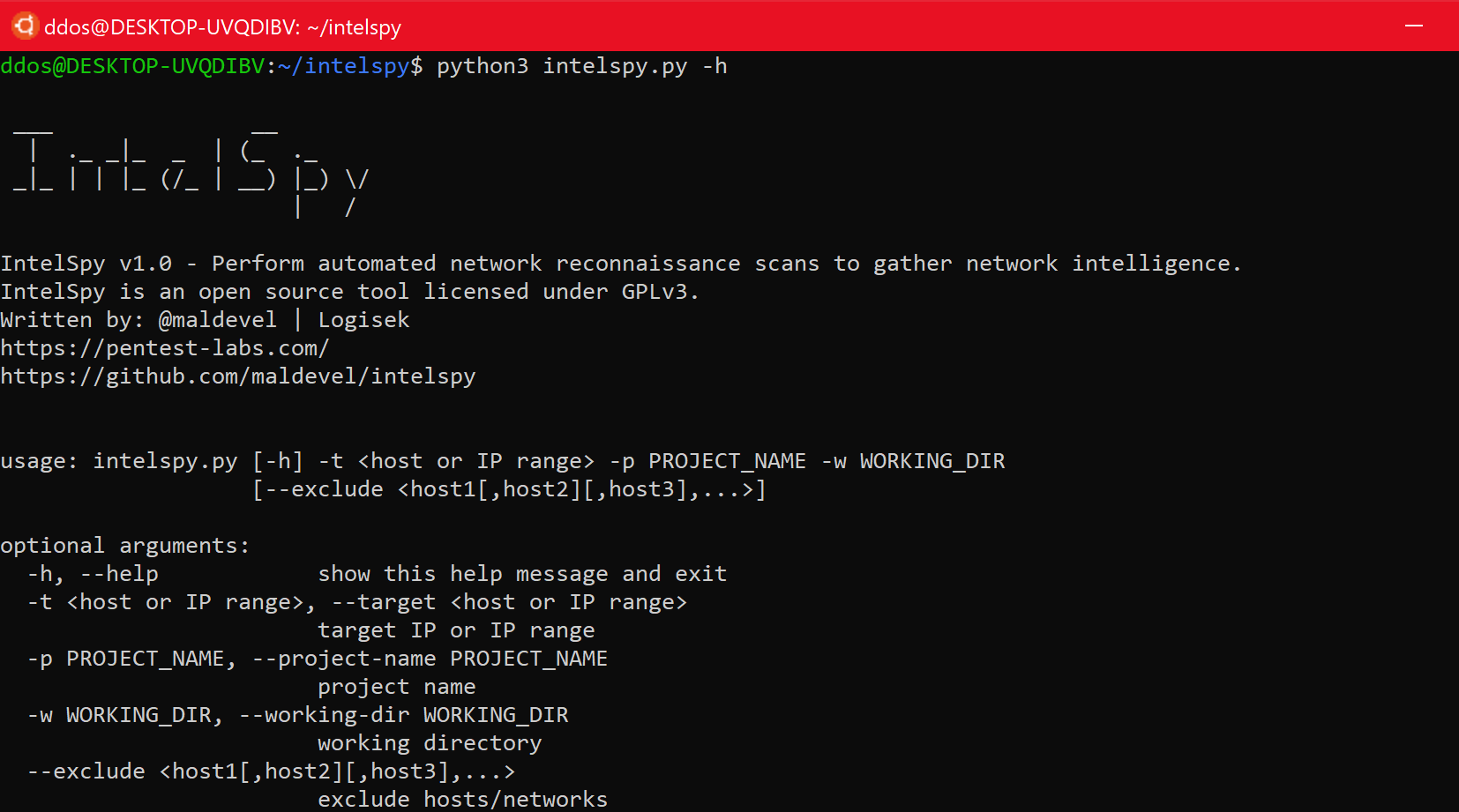
Use
___ __ | ._ _|_ _ | (_ ._ _|_ | | |_ (/_ | __) |_) \/ | / IntelSpy v1.0 - Perform automated network reconnaissance scans to gather network intelligence. IntelSpy is an open source tool licensed under GPLv3. Written by: @maldevel | @LOGISEK_LTD https://logisek.com | https://pentest-labs.com https://github.com/maldevel/intelspy usage: intelspy.py [-h] [-ts TARGET_FILE] -p PROJECT_NAME -w WORKING_DIR [--exclude] [-s SPEED] [-ct ] [-cs ] [--profile PROFILE_NAME] [--livehost-profile LIVEHOST_PROFILE_NAME] [--heartbeat HEARTBEAT] [-v] [targets [targets ...]] positional arguments: targets IP addresses (eg 10.0.0.1), CIDR notation ( eg 10.0.0.1/24), or resolvable hostnames (eg example.com) to scan. optional arguments: -h, --help show this help message and exit -ts TARGET_FILE, --targets TARGET_FILE Read targets from file. -p PROJECT_NAME, --project-name PROJECT_NAME project name -w WORKING_DIR, --working-dir WORKING_DIR working directory --exclude exclude hosts/networks -s SPEED, --speed SPEED 0-5, set timing template (higher is faster) (default: 4) -ct , --concurrent-targets The maximum number of target hosts to scan concurrently. Default: 5 -cs , --concurrent-scans The maximum number of scans to perform per target host. Default: 10 --profile PROFILE_NAME The port scanning profile to use (defined in port-scan-profiles.toml). Default: default --livehost-profile LIVEHOST_PROFILE_NAME The live host scanning profile to use (defined in live-host-scan-profiles.toml). Default: default --heartbeat HEARTBEAT Specifies the heartbeat interval (in seconds) for task status messages. Default: 60 -v, --verbose Enable verbose output. Repeat for more verbosity (-v, -vv, -vvv).
Examples of use
Scan a single target
sudo python3 intelspy.py -p MyProjectName -w / home / user / pt / projects / 192.168.10.15 sudo python3 intelspy.py -p MyProjectName -w / home / user / pt / projects / 192.168.10.15 -v sudo python3 intelspy. py -p MyProjectName -w / home / user / pt / projects / 192.168.10.15 -vv sudo python3 intelspy.py -p MyProjectName -w / home / user / pt / projects / 192.168.10.15 -vvv
Scanning a computer
sudo python3 intelspy.py -p MyProjectName -w / home / user / pt / projects / example.com
Scanning network bandwidth (CIDR)
sudo python3 intelspy.py -p MyProjectName -w / home / user / pt / projects / 192.168.10.0/24
Multi-objective scanning (comma separated)
sudo python3 intelspy.py -p MyProjectName -w / home / user / pt / projects / 192.168.10.15 192.168.10.0/24 example.com
Scan targets from a file
sudo python3 intelspy.py -p MyProjectName -w / home / user / pt / projects / -ts /home/user/targets.txt
Application snapshots
You can download the program from here.





