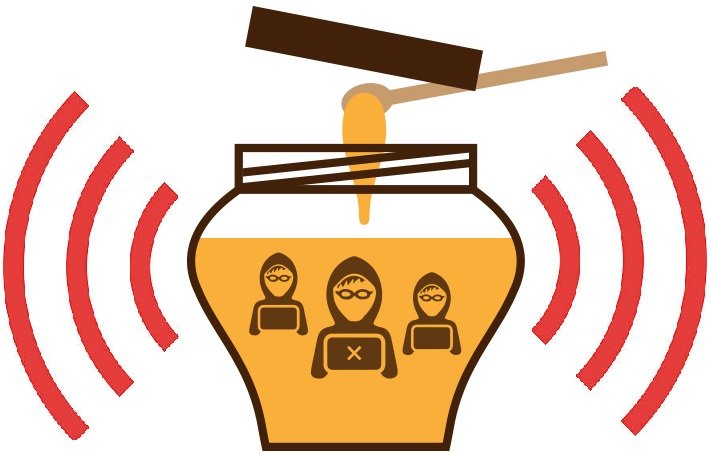
WireSpy allows users to quickly create honeypots to perform MITMA. The monitoring and recording function is implemented in order to "capture" the files from traffic data of the activities of the victims.
Also, many other tools can be used in conjunction with Wirespy to carry out more advanced attacks.
Two types of attacks are currently supported:
Evil twin: Force victims to automatically log in to the honeypot by forging a "trusted" hotspot (clone an existing access point and force users to log in easily and securely to the fake honeypot).
Honeypot: Set up a rogue hotspot and wait for customers to connect.
Specifications
- Capture the victims' traffic.
- MAC address spoofing.
- Set up honeypot and evil twin attacks.
- Display the list of access points.
- Wireless adapter card dongle power boost.
Available Commands
[pastacode manual=”Attacks%3A%0D%0Aeviltwin%20%3E%20launch%20an%20evil%20twin%20attack%0D%0Ahoneypot%20%3E%20launch%20a%20rogue%20access%20point%20attack%0D%0A%0D%0ACommands%3A%0D%0Aclear%20%3E%20clear%20the%20terminal%0D%0Ahelp%20%3E%20list%20available%20commands%0D%0Aquit%7Cexit%20%3E%20exit%20the%20program%0D%0Aapscan%20%3E%20show%20all%20wireless%20access%20points%20nearby%0D%0Aleases%20%3E%20display%20DHCP%20leases%0D%0Apowerup%20%3E%20power%20wireless%20interface%20up%20(may%20cause%20issues)%0D%0Astart%20capture%20%3E%20start%20packet%20capture%20(tcpdump)%0D%0Astop%20capture%20%3E%20stop%20packet%20capture%20(tcpdump)%0D%0Astatus%20%3E%20show%20modules%20status” provider=”manual” lang=”php”/]Use
- Export it script:
$ chmod + x wirespy.sh
- Run the script as administrators:
$ sudo ./wirespy.sh
- Type
helpto display the available options.
You can download it program from here.





