Researchers from company security FireEye revealed a new bug in iOS που επιτρέπει σε μια κακόβουλη εφαρμογή να παρακολουθεί και να συνδεθεί χρησιμοποιώντας τα δεδομένα αφής ενός χρήστη ενώ λειτουργεί στο παρασκήνιο. Το νέο exploit φέρεται να στοχεύει ένα ελάττωμα στις δυνατότητες multitasking του iOS “για να έχει πρόσβαση στα δεδομένα των χρηστών, και πραγματοποιεί την Mission them to a remote server.
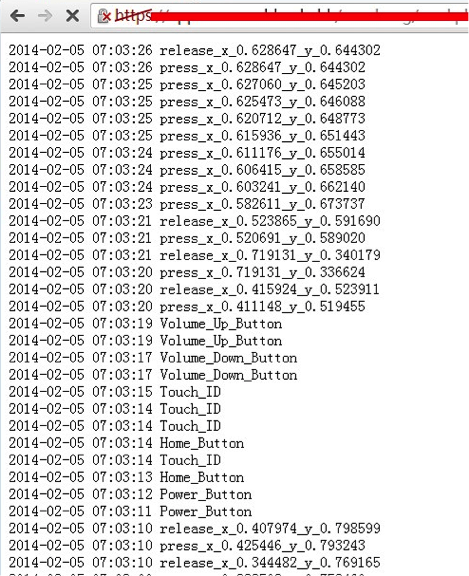
Για να αποδείξουν την ευπάθεια, οι ερευνητές δημιούργησαν ένα POC (proof-of-concept) των δράσεων της κακόβουλης εφαρμογής και ανέπτυξαν προσεγγίσεις για την αποτελεσματική procedure to "bypass" Apple's App Store. Once the app is installed on an iOS device, it starts recording what happens on the keyboard, data volume usage, home and power buttons, touches on the screen as well as all activities from Touch ID. All this is recorded and stored!
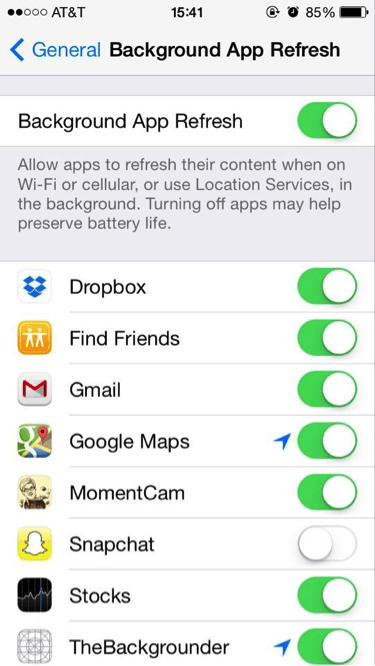
The researchers also noted that the malicious application disables the iOS "Background App Refresh" setting so that you do not disable the malicious app from data logging.
FireEye reports:
Note that our demo exploits the latest 7.0.4 version of the iOS system on a non-jailbroken iPhone 5s device successfully. We have found that the same sensitivity is available in iOS 7.0.5, 7.0.6, and 6.1.x versions. Based on the findings, potential attackers can use either phishing attacks or mislead the victim and install a malicious application or exploit another remote sensitivity of some apps, and then conduct background tracking.
The team added that they are actively working with Apple to fix the problem. The news comes less than a week after Apple released the iOS 7.0.6 update to identify an SSL vulnerability that allowed hackers to obtain or modify Safari and other apps data in allegedly secure sessions.