From in December of 2022, Check Point Research (CPR) has expressed concerns about the consequences of ChatGPT at cyber security. Now, CPR is warning that there is an increase in the trade of stolen ChatGPT Premium accounts, which allow cybercriminals to bypass OpenAI's geofencing restrictions and gain unrestricted access to ChatGPT.
The market of ATOs (account takeovers), of stolen accounts on different online services, is one of the most thriving markets in the hacking underground and dark web. Traditionally, the market she aimed in stolen financial services accounts (banks, online payment systems, etc.), social media, online dating sites, emails and more.

As of March 2023, CPR is seeing an increase in chat and trade of stolen ChatGPT accounts, with a focus on Premium accounts:
- Leaking and free posting of credentials to ChatGPT accounts
- Stolen ChatGPT premium account transactions
- Bruteforcing and Checkers tools for ChatGPT – which allow cybercriminals to break into ChatGPT accounts by running through huge lists of email addresses and passwords, trying to guess the correct combination to access existing accounts.
-
ChatGPT Accounts as a Service – a special service offering to open premium ChatGPT accounts, possibly using stolen payment cards.
Why is the market for stolen ChatGPT accounts growing and what are the main concerns?
As we wrote previously histology, the ChatGPT imposes geographic restrictions on access to platform of certain countries (including Russia, China and Iran). Recently we stressed that using the ChatGPT API; it allows cybercriminals to bypass different restrictions as well the use of your ChatGPT premium account.
All this leads to a growing demand for stolen ChatGPT accounts, especially paid premium accounts. In the dark websites, where there is demand – there are smart ones cybercriminals ready to take advantage of the business opportunity.
Meanwhile, in recent weeks there have been discussions about ChatGPT's privacy issues, with Italy to forbid it and Germany to consider a similar possibility. We highlight one more potential privacy risk of this platform. ChatGPT accounts store the account holder's recent queries. So when cybercriminals steal existing accounts, they gain access to the original owner's queries. This may include personal information, details about company products and processes and more.
Trade stolen accounts of Chat GPT
Cybercriminals often take advantage of the fact that users recycle the same password across multiple platforms. Using this knowledge, they load sets of email and password combinations into a special software (also known as account control) and perform an attack against a specific online platform to find the sets of credentials that match the login to the platform.
A final account takeover occurs when a malicious actor takes control of an account without the account owner's authorization.
Over the past month, CPR has noticed an increase in discussions on underground forums related to the leaking or sale of compromised ChatGPT premium accounts:
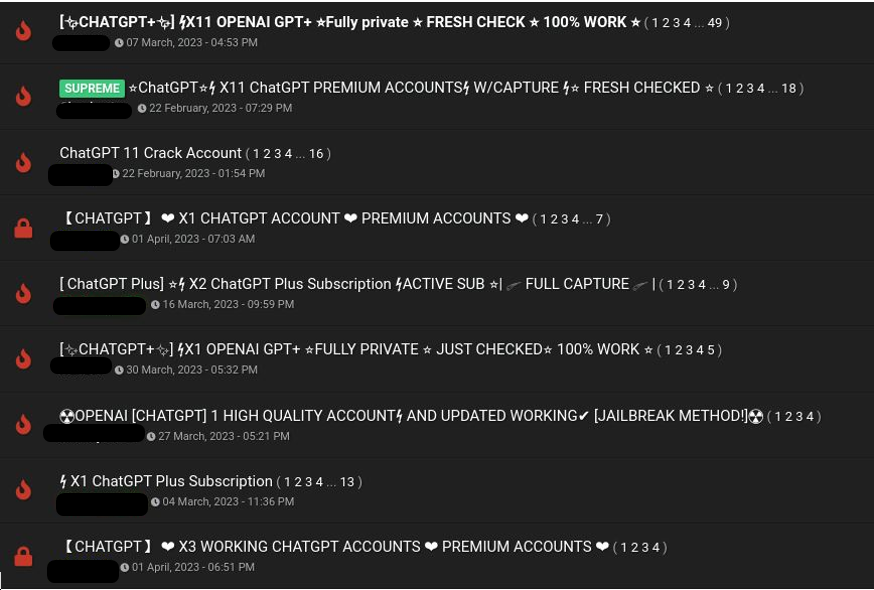
Image 1 - Threads in underground forums around stolen ChatGPT accounts
The stolen accounts are mostly sold, but some of the cybercriminals also share stolen ChatGPT premium accounts for free, to advertise their own services or tools to steal the accounts. In the example below, one cybercrime shared four stolen premium ChatGPT accounts. The way they were shared and their structure led CPR to conclude they were stolen using a ChatGPT account controller.
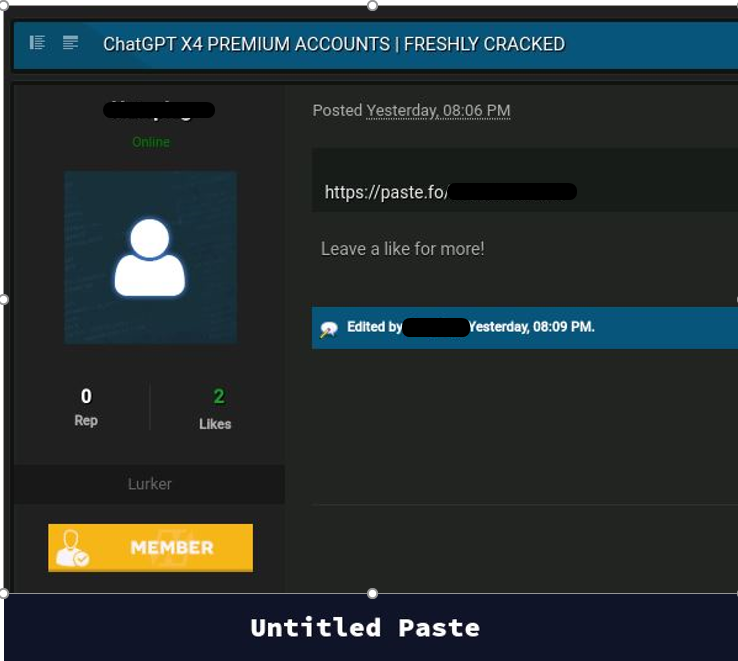
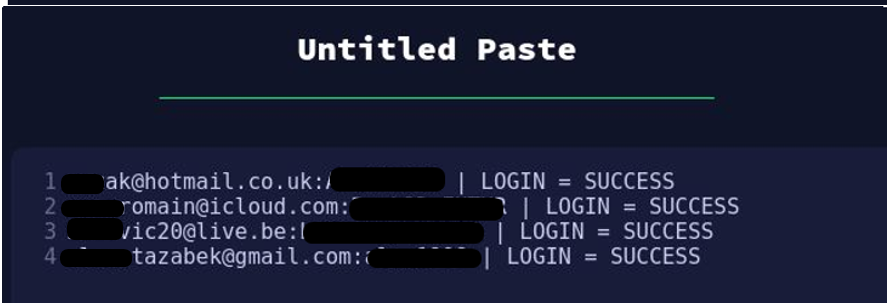
Image 2 – Cybercriminal sharing four premium ChatGPT accounts for free
Tools to Hack ChatGPT Accounts – Account Control and Configuration Files for Bruteforcing Tools
SilverBullet is one websites test suite that allows users to run requests to a targeted web application. It offers many tools to work with the results. This software can be used for collection and data analysis, automated pen testing, unit testing through selenium and more. This tool is also often used by cybercriminals to conduct credential stuffing and account control attacks against different websites and thus steal accounts for online platforms.
As SilverBullet is a configurable suite, to perform an audit or brute force attack against a specific website requires a “configuration” file that customizes this process for a specific website and allows cybercriminals to steal account of this website in an automated manner.
In this particular case, CPR identified cybercriminals offering a configuration file for SilverBullet that allows a set of credentials for OpenAI's platform to be checked in an automated manner. This allows them to steal accounts at scale. The process is fully automated and can start from 50 to 200 checks per minute (CPM). It also supports a proxy application that in many cases allows it to bypass different protections on websites from such attacks.
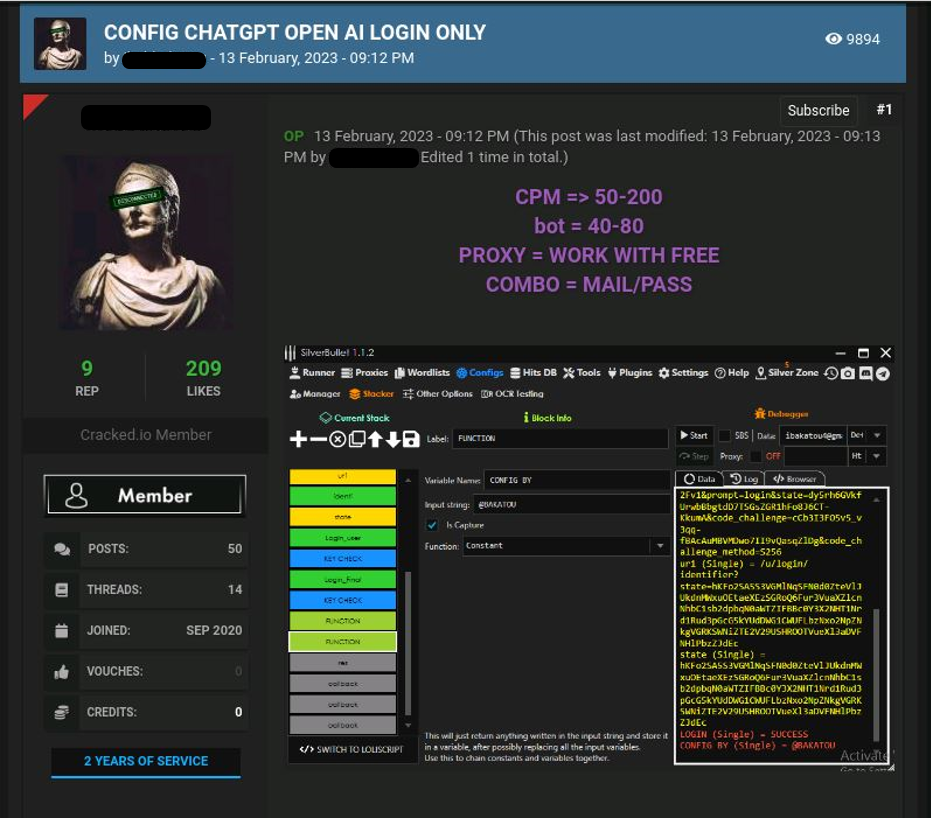
Image 3 – Cybercriminal offering openAI configuration file for SilverBullet
Another cybercriminal who only focuses on abusing and scamming ChatGPT products even named himself “gpt4”. Sta threads of, offers for sale not only ChatGPT accounts but also a configuration for another automated tool that checks the validity of a credential.
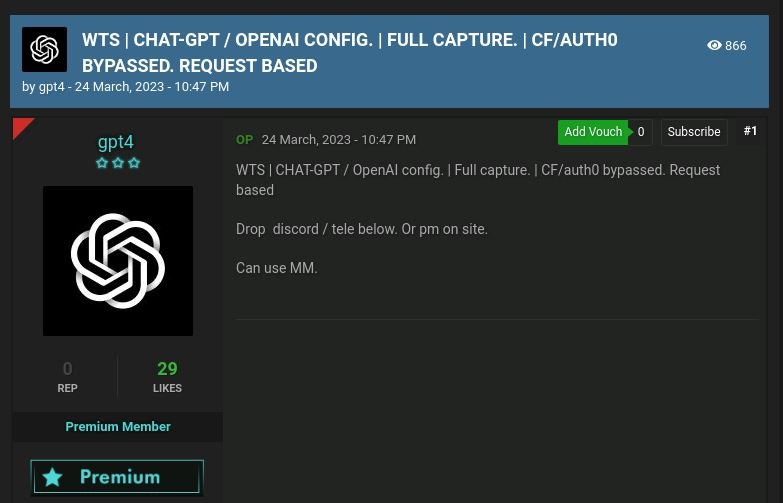
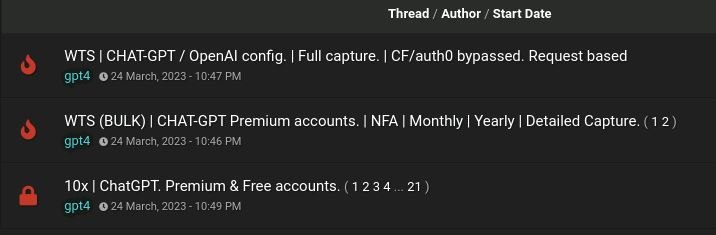
Image 4 – Cybercriminal named “gpt4” offers different services related to abuse around the platform
ChatGPT Plus lifetime upgrade service
On March 20, an English-speaking cybercriminal started advertising an account service Chat GPT More Lifetime, with 100% satisfaction guaranteed.
A lifetime upgrade to the regular ChatGPT Plus account (opened via email provided by the buyer) costs $59.99 (while OpenAI's initial legal pricing for this service is $20 per month). However, to keep costs down, this underground service also offers the option to share access to your ChatGPT account with another cybercriminal for $24.99, for life.
Some underground users have already left positive feedback for this service and vouched for it.
As in other illegal situations, when the threat actor provides certain services for pricing that is significantly lower than the original legitimate (for another example, see blog our on underground travel ticket services), we assess that payment for the upgrade is made using previously violationspaid payment cards.
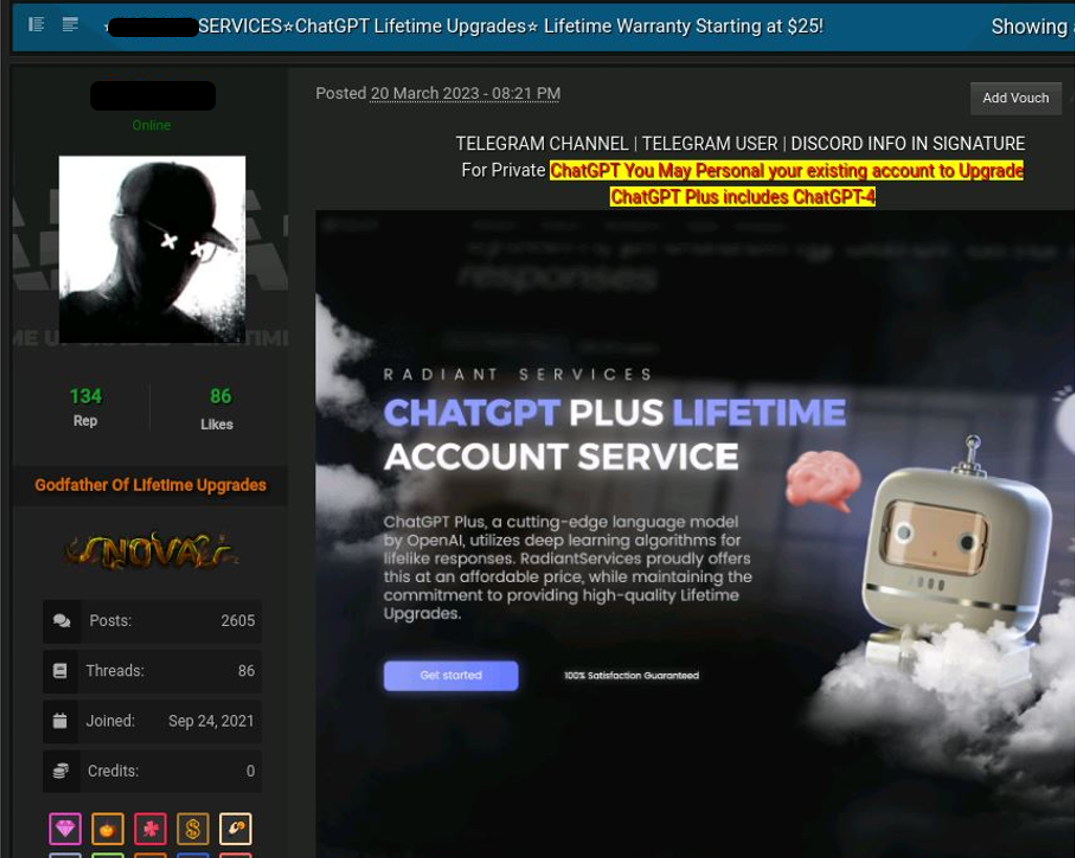

Image 5 – ChatGPT Plus lifetime account underground service





