DNS settings on some router models by D-Link can be modified without permission via the administration menu, from the web.
For this change and attack, virtually no authentication is required, and can be used to redirect users to malicious online sites, dangerous scripts, or even phishing pages.
The report that has been created was published by Todor Donev, a member of the Bulgarian security research team Ethical Hacker, whose goal is to establish a community of professionals who bring innovation to the field of computer security.
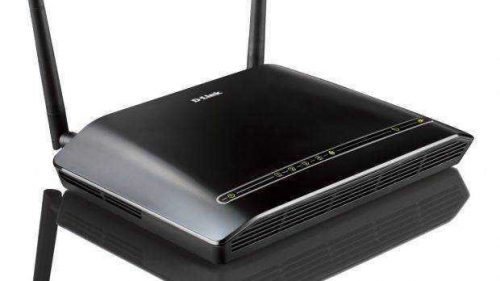
His research focused mainly on the D-Link DSL-2740R, but according to the report released on Tuesday, other routers from the same manufacturer are affected by this vulnerability. But the researcher did not list the affected devices.
It is unclear whether Donev contacted D-Link about the matter, as there is no word on an official release from the company's side about the problem. According to the official by clicking here of the company, the DSL-2740R has been discontinued, meaning it is no longer for sale.
However, although the production of the model has stopped, it can still receive support, since the models being released and used are still covered by the manufacturer's warranty.
Technology DNS, is responsible for the translation of domain to IP addresses of server hosting the websites. If the device is set to connect to one server DNS managed by scammers, the content that the user sees will of course not be the normal one.





