Η ESET presents the Enterprise Potao Express, an extended one analysis of the cyber espionage group behind the malware family Win32 /Potao. 
In her report ESET with the same name all the technical details are described and the deployment mechanisms and the most notable attack campaigns are described since the first appearance of the malware 2011, up to date.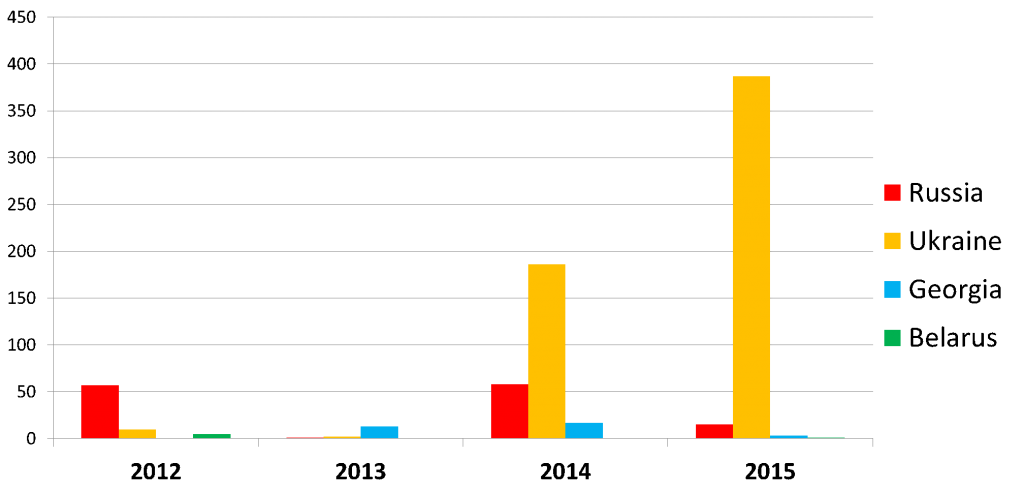
The Win32 /Potao is an example of malware spyware. It was mainly detected in Ukraine and some other CIS countries, including Russia, Georgia and Belarus. The family Potao is a typical one Trojan cyberguard that steals passwords and sensitive data, sending them to the remote server who has launched the attack. 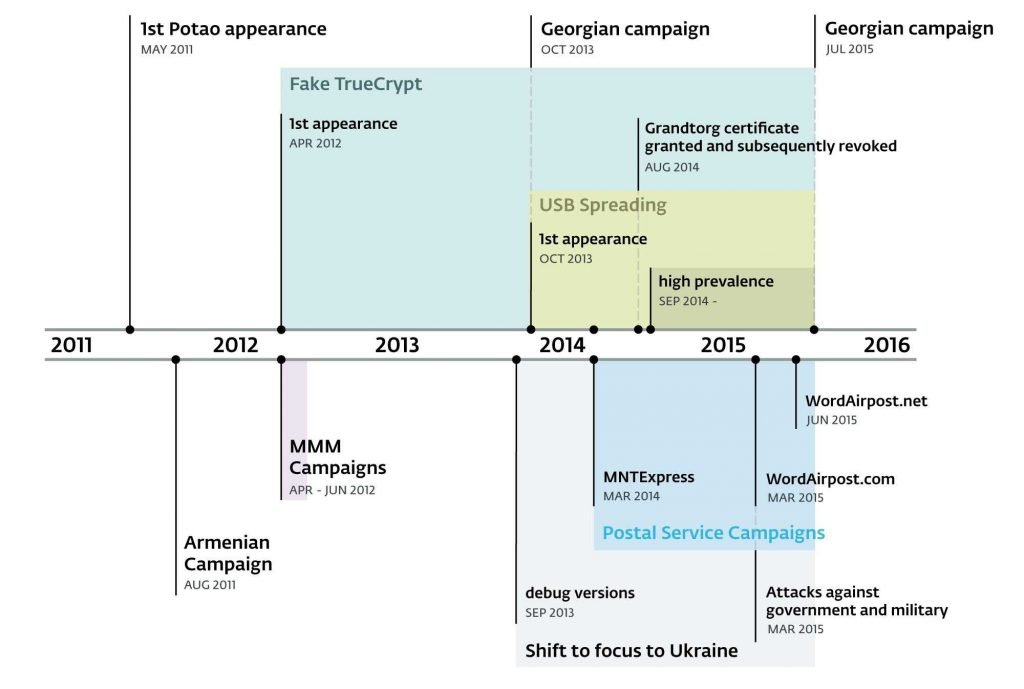
Similar to BlackEnergy, the Potao was used to spy on the Ukrainian government, military entities and a Ukrainian news agency. It was also used to spy on members MMM, a popular economic pyramid in Russia and Ukraine.
In addition to the variety of attack campaigns, there is another interesting point about it Win32 /Potao.
"Our investigation into Potao revealed a very interesting connection to a Russian version of the popular encryption software open code TrueCrypt, which no longer works, "he says Robert Lipovsky, Senior Malware Researcher in ESET.
Continuing the search, her researchers ESET found another link between its modified version TrueCrypt into a Trojan and the site truecryptrussia.ru, which, in addition to a carrier of infected encryption software, was found to be acting as well command and control (C&C) server for backdoor cuts.
More information on link: «Operation Potao Express: Analysis of a cyber-espionage toolkit» on WeLiveSecurity.com.





