Η Google επιβράβευσε ένα ερευνητή ασφάλεια με 5.000 δολάριο για την ανακάλυψη και την υποβολή μιας ευπάθειας cross-site scripting στην κονσόλα managementof Google Apps which could give an attacker full control over a Google account.
Many businesses associate their domains with Google services, allowing them access to Gmail, and working with Google Apps.
The technician security of Blizzard Entertainment, Brett Buerhaus discovered an XSS form that could be used when logging into the management console.
The log-in process requires the user's credentials, displaying at least two Google accounts. In the Google account switching form after the choice of one of the accounts, runs a JavaScript to redirect the browser to the correct page.
“The URL used in this JavaScript is provided to the user to continue the request parameter. The parameter that continues the request is a fairly common variable request in the Google login stream. But this is the only page I could find that did not validate the URL. The feature allows Cross-site Scripting attacks to be used using "javascript:" as part of the URL and will be executed when the browser redirects, "says Buerhaus. in one publication.
Exploitation of this vulnerability could allow an attacker to creationς νέων χρηστών με οποιοδήποτε επίπεδο δικαιωμάτων, συμπεριλαμβανομένου και του σούπερ διαχειριστή, την αλλαγή των ρυθμίσεων ασφαλείας για τους χρήστες ή τα domains, την αλλαγή των ρυθμίσεων του domain, για να προωθεί τα εισερχόμενα μηνύματα ηλεκτρονικού ταχυδρομείου σε διαφορετικό domain.
Additionally, the attacker could take control of different e-mail accounts with the password reset method. It could disable the two-factor authentication feature, completely weakening security in the targeted account.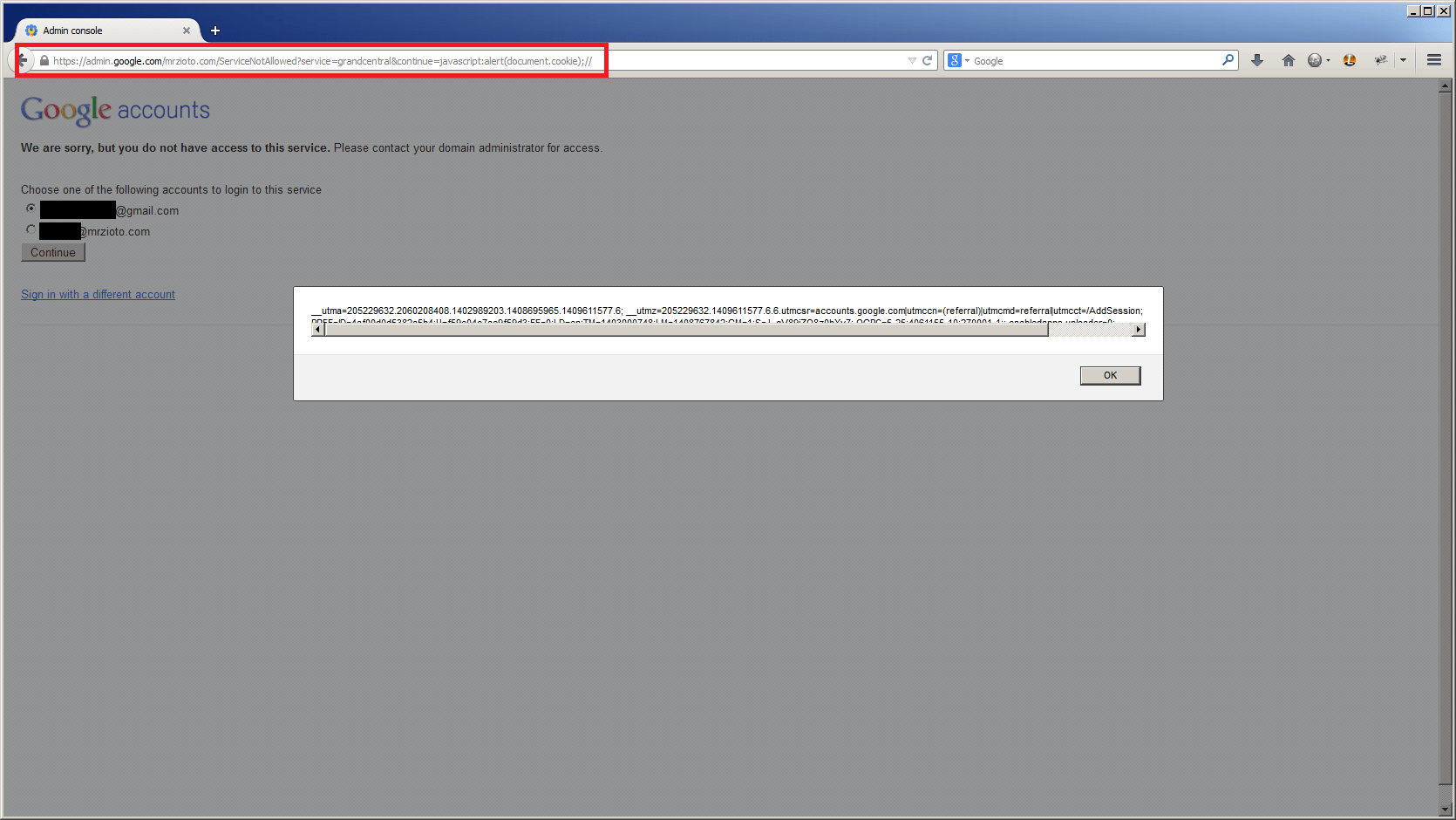
The researcher published a PoC to prove what he claims. Google has already corrected the vulnerability.





