HosTaGe is a lightweight mobile honeypot aimed at detecting malicious, wireless networks.

As most malware spreads over the network and through specific protocols, a honeypot can scan wireless networks for active propagation malicioussoftware.
The company, as it says, envisions such a thing honeypots to work in all genres mobile συσκευών, π.χ. smartphone and tablet, to provide a quick security assessment of a network.
HosTaGe imitates the following protocols in its latest version: AMQP, COAP, ECHO, FTP, HTTP, HTTPS, MySQL, MQTT, MODBUS, S7COMM, SNMP, SIP, SMB, SSH, SMTP and TELNET
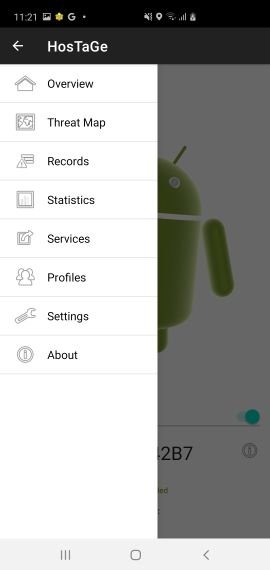
To start the honeypot service, the device must be connected to WiFi or LTE / 4G network. The honeypot service can be started from the home screen using the switch. By default, the "Paranoid" profile starts, which mimics all protocols in HosTaGe.
Specifications
The bot has three states:
- Safe (Cheerful Dancing)
- Under Attack! (Jumping in red with a bee)
- Infected Network (A vigil bot)
By default when the honeypot service starts on a new network, the android bot starts with a happy gesture indicating that the network is secure. The current state of the network can also be checked by double-clicking on the bot.
When it detects an attack, the android bot starts jumping in panic with a bee around it. This is done to notify the user that an attack has been detected.
The bot displays the panic function for a detected attack for a period of 15 minutes. After this period, the bot displays a warning gesture notifying the user that the network is infected.
HosTaGe also stores the infected networks in its database so that the user is notified whenever the application is connected to an infected network.
Application snapshots
You can download the application from here. No longer available from Play Store.





