Στο ετήσιο συνέδριο της παγκόσμιας εταιρείας κυβερνοασφάλειας ESET, οι ερευνητές της ESET παρουσίασαν μια νέα έρευνα σχετικά με την περιβόητη ομάδα APT (Advanced Persistent Threat) Lazarus.

Jean-Ian Boutin, ESET's Director of Threat Research, analyzed several new campaigns carried out by the Lazarus team against defense companies around the world from late 2021 to March 2022.
In the relevant attacks of the period 2021-2022 and according to ESET telemetry, the Lazarus team targeted companies in Europe (France, Italy, Germany, the Netherlands, Poland and Ukraine) and Latin America (Brazil).
Although the main purpose of this Lazarus operation is cyber espionage, the team has also tried to extract money (unsuccessfully).
"The Lazarus team showed ingenuity by developing an interesting set of tools, including, for example, a user mode component that is able to exploit a vulnerable Dell driver to write to the kernel memory. Αυτό το προηγμένο τέχνασμα χρησιμοποιήθηκε σε μια προσπάθεια παράκαμψης της παρακολούθησης λύσεων security” says Jean-Ian Boutin.
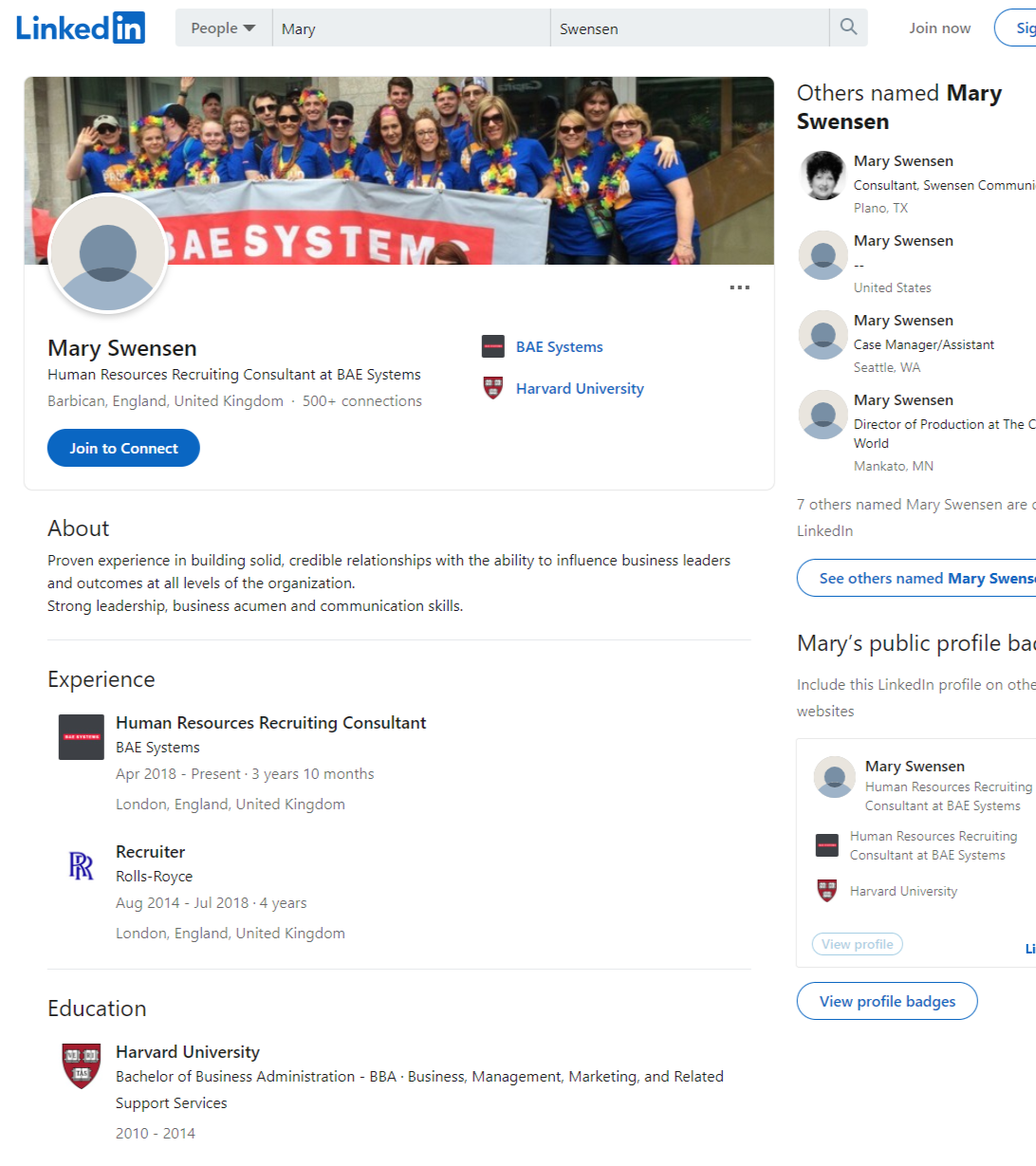
As early as 2020, ESET researchers had recorded a campaign called In (ter) caption, in which a Lazarus subgroup targeted European aerospace and defense companies. This campaign was notable, as the group used social media, particularly LinkedIn, to build trust between the attacker and an unsuspecting employee before sending malicious disguise information in the form of job descriptions or applications. Companies in Brazil, the Czech Republic, Qatar, Turkey and Ukraine were already in the spotlight at the time.
ESET researchers believed that the activity was mostly targeting European companies, but after tracking a number of Lazarus sub-groups running similar campaigns against defense companies, they soon realized that the campaign was expanding in scope. Although the malware used in the campaigns was different, the initial modus operandi (modus operandi) always remained the same: an alleged recruiter communicated via LinkedIn with an employee and eventually sent the malicious information.
In this respect, they have continued to act in the same way as in the past. However, ESET researchers have also found that evidence from a genuine recruitment campaign was used to legitimize the group's fake recruitment campaigns.
In addition, attackers have used services such as WhatsApp or Slack in their malicious campaigns.
Misleading recruitment campaign by the Lazarus team
In 2021, the US Department of Justice indicted three computer programmers for cyber-attacks while working for the North Korean military. According to the US government, they belonged to the North Korean military hacker unit, known to the infosec community as the Lazarus Group.
Alongside the new Lazarus research, ESET presented during its annual conference the topic “Past and Present Cyberwar in Ukraine” (Cyber War in Ukraine, Past and Present).
ESET researcher Robert Lipovský studied cyber warfare in depth during Russia's invasion of Ukraine - including the recent attempt to cut off the country's electricity grid using Industroyer2 and various wiper attacks.
Finally, at the ESET World conference, former International Space Station commander Canadian astronaut Chris Hadfield and ESET Progress Protected campaign executive and ESET CEO Richard Marko discussed the specifics of technology, science and life.





