Lure10 Attack over Wi-Fi Sense: Karma has long been a key man-in-the-middle attack used for authorized wireless network security assessments. However, many modern operating systems and routers provide effective countermeasures, and thus need other approaches to cheating wireless clients.
We introduce you to Lure10: a new attack that takes advantage of the Windows Wi-Fi Sense feature.
What is Wi-Fi Sense?
Wi-Fi Sense, which is turned on by default in Windows 10 and Windows Phone 8.1, is a feature that automatically connects users to open wireless networks they know (are reconnected).
Based on information collected from various Windows Appliances that were connected to these open networks, Microsoft evaluates whether they provide a good quality connection, and if they do, adds them to the list of hotspots suggested by Wi-Fi Sense.
Wi-Fi Sense will select and show the user a network when in range, automatically accept their conditions of its use and will automatically connect it to this network.
The Lure10 technique
The success of the attack presented by the security technician George Hadjisofronius at this year's conference Hack in the Box in Amsterdam is based on the following:
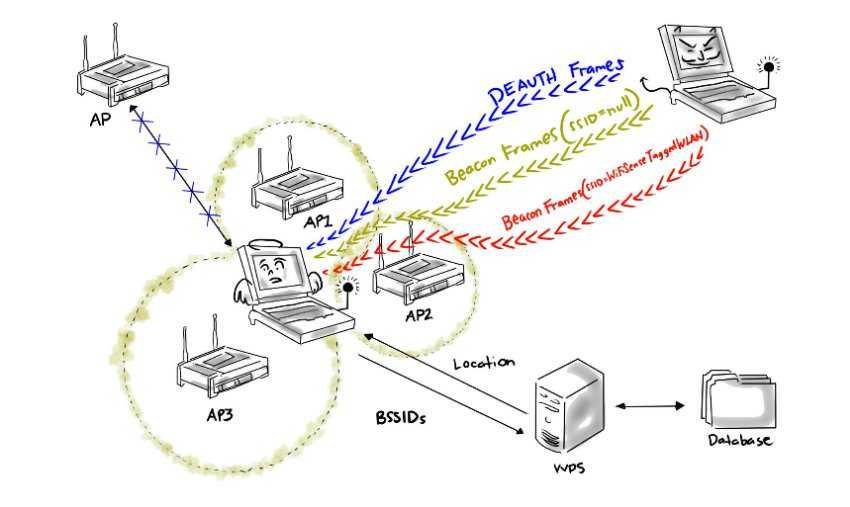
- The victim's device is tricked into believing it is within the geographic area of an open wirelessy network labeled Wi-Fi Sense
- The attacker successfully interrupts the existing Wi-Fi connection of the victim's device (by falsifying DEAUTH frames) and
- It successfully mimics this Wi-Fi Sense network (a network with the same ESSID - extended service set identifier).
This last condition can be achieved by finding a Wi-Fi Sense network located in an area relatively close to the victim (eg in his home country) and by collecting ESSID (eg “AIRPORT_FREE”).
At the same time, the attacker should also collect the BSSIDs of other wireless networks in the same area, as they are also used by the Windows discovery service to determine the location of a device.
With these BSSIDs, the attacker can fool Windows that think the device is in the area of the impersonation network (the first condition of the attack).
Once the attacker manages to perform these two steps, he begins to send beacon frames to the ESSID of the Wi-Fi Sense network he imitates. This is enough to automatically connect the victim's device if shared WLAN exists in the list of preferred networks and the list of available networks.
But even this last situation can be achieved. You can see the researcher presentations for more details.
How To Protect Yourself?
The Lure10 attack technique has been added to the latest version of the tool open code Wifiphisher Rogue Access Point, developed by George Hatzisoforion.
The researcher said that Microsoft has been informed about this issue, has recognized its seriousness but has not yet taken steps to correct it.
You can protect yourself from this attack by disabling Wi-Fi Sense on your device.



