Everyone knows and has read about the OpenSSL bug heartbleed, a critical error in running OpenSSL that allows attackers to read portions of the affected server's memory by revealing user data.

Heartbleed's vulnerability has become a front page all over the world, but some readers do not know its nature, otherwise they would not be the victims of the spam that followed.
The Spammers χρησιμοποιούν κάθε ευκαιρία και έτσι αυτή τη φορά να εκμεταλλεύονται το περίφημο Ηeartbleed bug για να τρομάξουν τους users and lead them to install an Anti-Heartbleed software on their systems, which is of course malware.
Her researchers Symantec αποκάλυψαν μια εκστρατεία το spam που διαδίδεται με την αποστολή μηνυμάτων και προειδοποιούν τους ανυποψίαστους χρήστες ότι τους σύστημα μπορεί ακόμα να “μολυνθεί” από το Ηeartbleed bug (!). Έτσι ζητάει να εκτελέσουν το εργαλείο αφαίρεσης του bug Ηeartbleed (που έρχεται συνημμένο στο μήνυμα) προκειμένου να αφαιρέσουν τον ιό από το σύστημά τους.
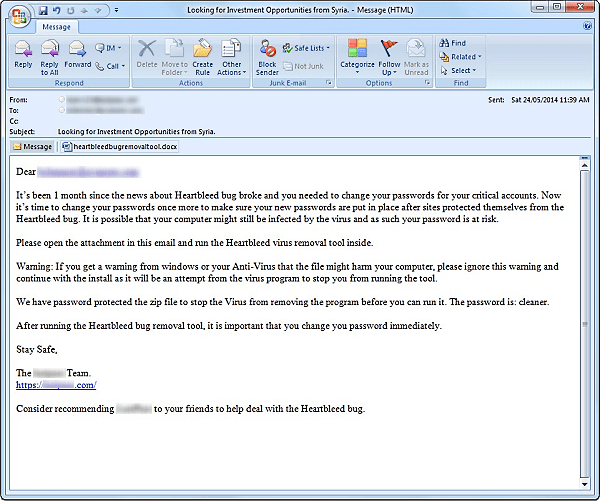
Those who do not know that Heartbleed is not a virus or Malware, but a vulnerability of OpenSSL is falling into the spammers' trap.
If someone opens the attachment which appears to be a docx file, an encrypted zip file will also come. When the victim extracts the content zip file, it will find an executable .Exe that it thinks is the Heartbleed bug removal tool.
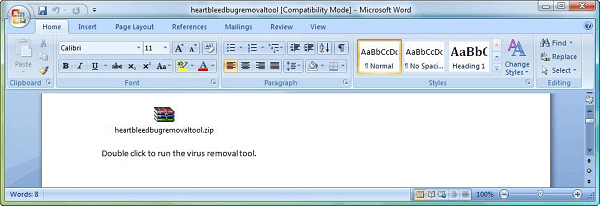
Once the .exe runs it downloads a keylogger to the background, without his knowledge, while a progress bar appears with a message stating that the Heartbleed bug was not found and the computer is clean.
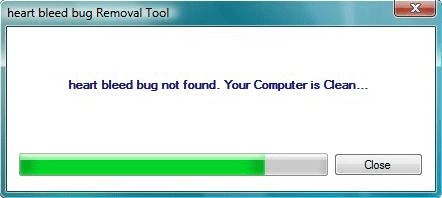
The victim feels relieved after knowing that he is not at risk from Heartbleed but at the same time ignoring that there is a keylogger that records that he typed on his computer. The keylogger installed in the background except that it records the keystrokes, gets screenshots and sends the information to the criminals.





