Two Greek researchers managed to identify a loophole security on a NASA website (subdomain), which allowed them to perform a SQL injection and gain access to the agency's database.
According to Greek researchers, the US space agency was promptly alerted to the security gap, but to date it has not made any correction.
Researchers Dimitris Chatzidimitris and Anastasis Vasileiadhs report at Secnews.gr via email:
"On August 29 we spotted one vulnerability while navigating to a Nasa page (https://www.jpl.nasα.gov/which relates to various promotion systems….
Vulnerability is a type SQL injection and the link to this weakness is:
Note Secnews.gr: We do not list the link for obvious reasons but we list some of the items we received by email:
Parameter: catId (GET)
Type: boolean-based blind
Database version: 5.1.61-community-lo
"This particular vulnerability gave us access to the databases of that site"
Researchers report:
"After that we did not proceed to any possible access to the server beyond the bases as we had already confirmed that the page was not secure.
Immediately on August 27 we contacted the contact form on their page and we briefed them in detail to correct their security.
Until today 8 September we did not get any answer on this.
Security researchers:
Dimitris Chatzidimitris
Anastasis Vasileiadhs ”
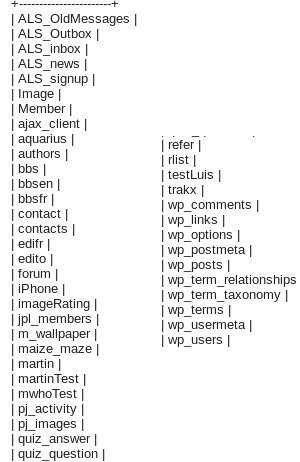
We quote a screenshoot from the database tables. We notice that the tables also contain the user data of the web page (usernames and passwords).
See the image below (wp-users, contacts, Member, authors)
_____________________________________
The information remains available to interested parties, both by the researchers themselves and by Secnews.gr.
Η information for vulnerabilities discovered in organizations, it is considered highly necessary (especially when they exist on high-traffic websites), and for us at Secnews.gr they are an immediate priority.
We hope that in this way, i.e. the immediate report of each vulnerability and not with its "hood", we contribute to a safer internet.
Of course, we have met many companies and organizations, both locally and globally, that instead of working together to resolve a vulnerability, they are moving legal means to persecute the researchers by covering the security gap very carefully with the mat, trying to avoid negative impressions .





