Recently a more complex version of it appeared Svpeng Trojan for Android mobile devices and seems to have been equipped with ransomware capabilities.
The threat appeared on the scene security about a year ago, and at that time it was considered a typical Trojan-SMS that hijacked SMS to hit bank accounts. But soon it started to get more complicated.
In early June, Kaspersky Lab researchers discovered a new modification of Svreng that gave him ransomware features.
Unlike the first malware that encrypted the mobiles of its victims (Android/Simplocker-Trojan Ransom.AndroidOS.Pletor.a) and analyzed by ESET and Kaspersky, the new Svреng encrypts the entire device and not just specific files.
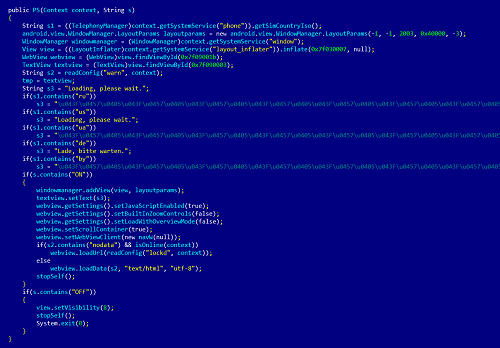
This is achieved by locking the smartphone until the ransom is paid. The device will not respond to any actions other than those that lead to a payment or disablement. However, as soon as the mobile starts again, Trojan takes control again.
Just like Trojan-Ransom.AndroidOS.Pletor.a does, the new Svring takes a photo of the victim and displays it in the ransom message, stating that the device was locked because it was "used to visit pornographic websites", which is "Violation of the federal laws of the United States of America."
The ransom reaches 200 dollars (148 euros) and alternative payment methods are provided, such as through the MoneyPak service.
In addition to encrypting the device, the malware checks the system for the presence of certain banking applications. The data which collects and sends them to the command and control server.