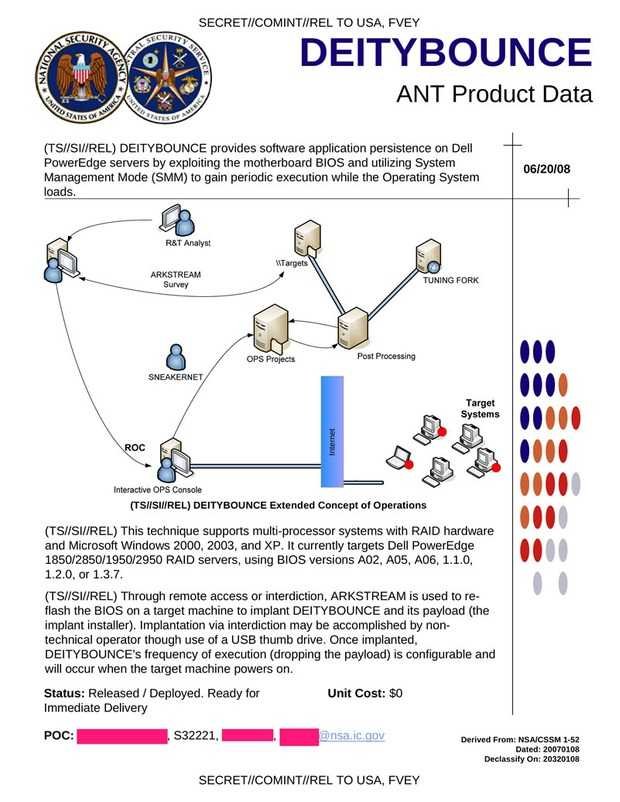
A new document that leaked by Edward Snowden describes the program DEITYBOUNCE of NSAThe document describes how the NSA can access its systems Dell and more specifically on PowerEdge servers by utilizing the motherboard's BIOS and using it System Management Mode (SMM). With this particular technique the malicious US Secret Service program, is loaded during operating system startup.
The attack, as described, requires physical access to the system with a USB, apparently using the Autorun bugs known by Stuxnet. Once embedded in the system BIOS the tool starts working as soon as it starts loading operating system.
In accordance with ZDNet the document has date Ιανουαρίου 2007 (ίδια ημερομηνία με το έγγραφο που περιγράφει το hack του iPhone), and the attacks described in it were certainly much more difficult to accomplish then, than they are today. The specific attacks do not work on all systems and models. They are aimed at “Microsoft Windows 2000, 2003 and XP. Affected models are Dell PowerEdge servers 1850/2850/1950/2950 RAID, using BIOS versions A02, A05, A06, 1.1.0, 1.2.0, or 1.3.7.”
Of course, the NSA should have updated the attack technique from 2007 to date as operating systems and firmware in today's existing technologies have the potential to overturn this form of attack. Unified Extensible Firmware Interface (UEFI) technology along with Secure Boot implement a PKI-based authentication that runs on the computer. If, of course, the NSA has access to the keys, it does not need to flash the malicious code in the BIOS. Dell and Microsoft have been using UEFI with Secure Boot in recent years. Certification of a Windows 8-based system requires UEFI and Secure Boot and is enabled by default using a Microsoft private key.
So if major technology companies do not cooperate with the NSA (by providing certification keys), it is quite difficult for secret services to breach such systems. But with the revelations that are constantly coming from Edward Snowden, it is becoming clear that we should not use closed-source operating systems.