A fake Paypal website that was basically fishing for victims (Phishing), asked users to confirm their account by sending a selfie photo of themselves in which they would hold their identity.
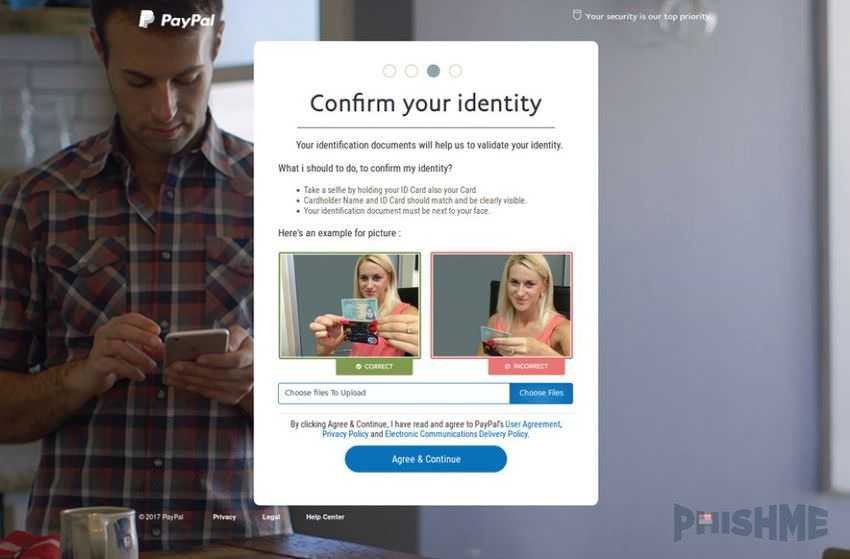
Her fake website PayPal deceived its victims by presenting a copy of the Paypal login page urging users to login by giving their password, and in addition their credit card details, and self a selfie of the user in which he would explicitly keep his identity.
The issue was brought to the attention of PhishMe security investigators, and according to their report, the scammer was trying to direct users via emails to a phishing PayPal web page, written in Wordpress, located in New Zealand.
At this time, this phishing website has been removed. Its URL did not resemble that of Paypal, so users who had some phishing experience would have to immediately notice that they were on a page with the wrong address.
In the first authentication of users, the website asked users to write their name and password. But the scammer was not satisfied. Once someone entered their password on this page, the scammer was sure they were dealing with a careless or uneducated user, and so proceeded to request more information. During a four-step process, the website asked for the user's address, the data of his credit card, and a selfie photo of him holding his ID in his hand.
It is not clear why the scammer wanted this information. Her expert PhishMe Mr Chris Sims believes he wanted them to "create cryptocurrency accounts, to launder money stolen from other victims."
Of course this technique with the selfie, where the victim holds his ID in his hand, it is not done for the first time. In October 2016, McAfee had discovered a variant of the Acecard Android banking trojan, which also asked users to take a selfie while logging in to their bank account.
The tactics were quite innovative at the time, and several articles were written about it. So he probably gave the idea to the current scammer and decided to adapt it to his phishing.
The process of “selfie Missions" on the current website is strange. Instead of relying on WebRTC or Flash to access the user's camera for the user to take a photo and save it automatically, the scammer asked users to upload a photo from their computer. This means more hassle, as the user has to take a selfie, transfer it to the computer, and then upload it to the scammer's page. Extending the attack in this way gives the user more time to notice something wrong with the fake Paypal website and stop the process.
In addition, there is a second issue. Phishing websites usually do not have rules in the form of the validation format, and they take whatever users upload. This phisher had special rules for the format of the photos and requested only JPEG, JPG or PNG format.
The fraudster also made mistakes. The user's photo was not stored on a server under the scammer's control, but sent the data to an e-mail address in "oxigene [.] 007 @ Yandex [.] Com."
Sims says he searched for this address in the Skype user list and found a person called "Najat Zou," from "Mansac, France." Of course this information is not credible to determine his or her nationality or location user, simply provide a first step from which police officers may start investigating if they decide to investigate the matter further.





