The program Pidrila (from Python Interactive Deepweb-oriented Rapid Intelligent Link Analyzer) is really fast prototype web path scanner developed by BrightSearch team for all ethical netstalkers.
Installation & use
git clone https://github.com/enemy-submarine/pidrila.git
cd pidrilla
python3 pidrila.py -u
Options
Usage: pidrila.py [OPTIONS]
Options:
-U, –user-agent TEXT User-Agent
-t, –timeout INTEGER Request timeout [default: 30]-A, –auth TEXT Basic HTTP auth, ie login:Password
-M, –max-connections-per-host INTEGER
How many simultaneous connections should we
open (per each host) [default: 16]
-m, –max-connections INTEGER How many simultaneous connections should we
open [default: 128]
-p, –proxy TEXT Proxy address, like socks5h://127.0.0.1:9050
-p, –pathlist FILENAME Path list
-L, –url-list FILENAME Target URL list
-u, –url TEXT Target URL, option is mutually exclusive
with url_list [required]
-l, –logs DIRECTORY Destination directory for the logs
–Http-method [head | get] HTTP method: GET or HEAD [default: get] –help Show this message and exit.
Specifications
- Asynchronous
- Can simultaneously scan an unlimited number of sites
- keep-alive support
- HTTP and SOCKS proxy support
- User agent randomization
Examples of use
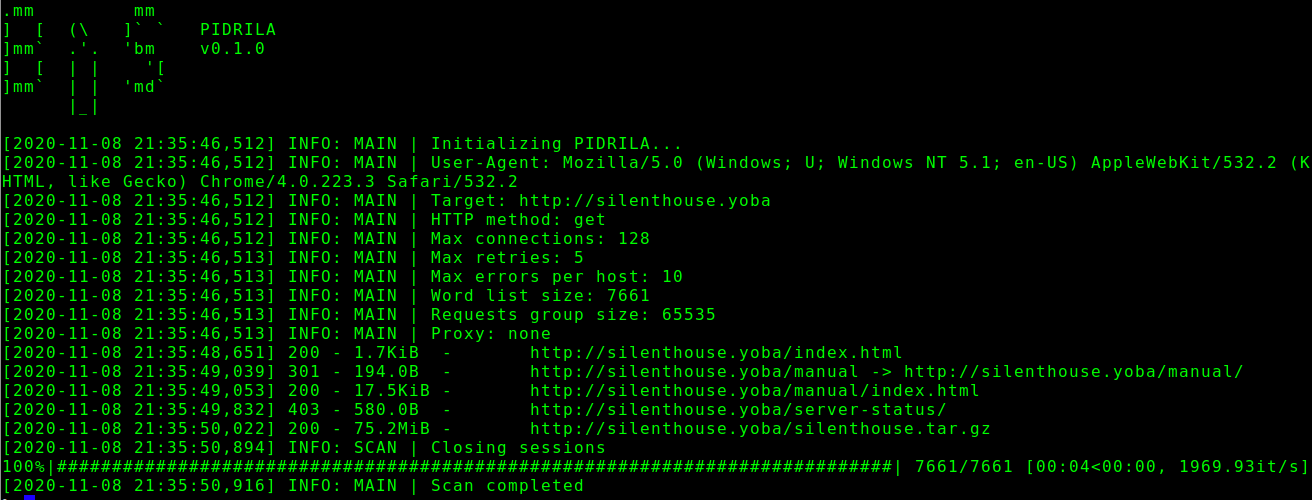
Scanning an individual Clearweb site
python3 ./pidrila.py -u http: //silenthouse.yoba -M 128
Scan site onion
python3 ./pidrila.py -u http://zqktlwi4fecvo6ro.onion -m 16 -M 16 –proxy = socks5h: //127.0.0.1: 9050
Fast bulk scan with custom User-Agent
python3 ./pidrila.py -m 2048 -L darkweb_sites_list.txt –user-agent “Pantusha / 2.0 (4.2BSD)”





