This RobbinHood does not give to anyone .. Many security products include infringement protection (tamper protection) which makes it very difficult to turn off the software, at least without leaving any traces.
The instant updates they also make it more difficult for malicious users to invade vulnerable systems because they close security vulnerabilities and cannot exploit them.

Similarly, system services often keep their critical files in permanent use, which means that they cannot be easily deleted or modified, which prevents malicious users from destroying them with an attack. ransomware.
But the best one wins… ..
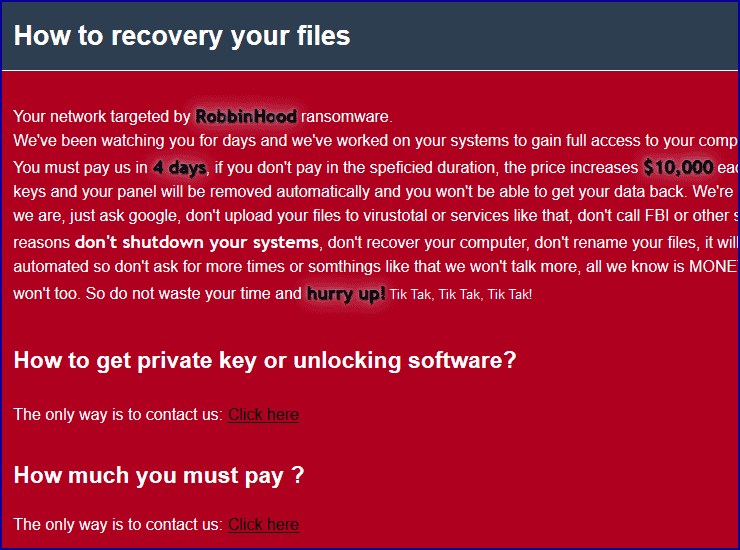
This could be the difference between a ransom claim that you can not avoid paying, because everything is coded and you can not ignore it because all your important data does not exist and your business can not work. .
This is where the maliciousness comes in software RobbinHood:
Malicious users have discovered a way that helps them bypass all of the above much more easily and gain access to any "secure" system. We wrote the safe with quotes because we consider it a very big tale for the security companies and the peb testers to get rich.
The masters of RobbinHood, instead of looking for weaknesses in functional and system software, they simply brought their own bug!
The way it works is a fascinating story, told in great detail in a SophosLabs survey. If you want more technical details about the attack that we will describe (in a few words) below, see here.
In short, the crooks along with the ransomware also added an old but buggy one Windows kernel driver.
The old driver is not malware, but an official software component from the motherboard Gigabyte, and that is why it is digitally signed by the company. Of course the signature is certified as genuine by Microsoft itself.
So Windows will load the wizard because of the signature…
After that, everything is easy, as as we mentioned the driver may be genuine but it contains an error, which fraudsters can exploit to trick Windows into letting them upload their own, unsigned and malicious files!
And the driver gives them low-level access to the kernel, processes and files of the system, which means that they can kill programs they want and delete files that are usually locked.
Distorting kernel behavior on its own can cause a number of problems, such as programs that stop working properly, or corrupted data, or even BSoD.
But fraudsters do not care.
By the time you notice minor problems, the damage is already done, and if the computer is on a network, all systems will be locked up. Meanwhile the key fromencryptiononly the cheater has it.





