A new variant of crypto-ransomware seems to be not as crypto as it allows its victims to take back their data without paying the ransom they require. The ransomware Scraper seems to have a flaw, which in practice means that about 70% of its victims can decipher their files, according to Kaspersky Labs, the Russian security firm that published a decryption mode.
Of course, it's a lot better να μην μολυνθείτε, αλλά εκείνοι που δεν πρόσεχαν, μπορούν να χρησιμοποιήσουν το utility offered by the company to avoid paying the $300 the scammers are asking for.
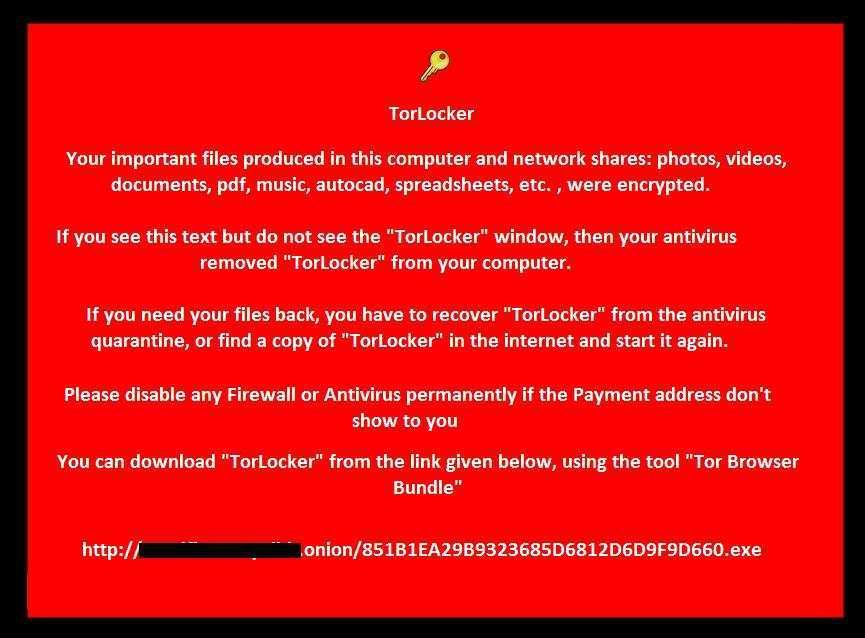
Malware Scraper (or TorLocker) first appeared in attacks in Japan last October. The Scraper later appeared in an English version, and encrypts the victim's files demanding a ransom ($300 or more, depending on how greedy the crooks are, to be paid to BitCoin or the Ukash service) to decrypt them.
More specifically, the malware encrypts almost all of the user's files, documents, video and audio files, images, databases, backups, virtual machine encryption keys, certificates and other files on all hard drives and on the network. It also deletes all her points resetof the system. Scraper only infects Windows computers.
User files are encrypted using multiple AES-256 one-time keys, an encryption key for each file. Kaspersky Labs says that somewhere this process went wrong, although other experts have their own theories. In any case, mistakes have clearly been made, otherwise decryption would be impractical.
"Although Trojan-Ransom.Win32.Scraper encrypts all files with AES-256 + RSA-2048, 70 percent of cases can be decrypted due to errors in the application of encryption algorithms," Kaspersky researchers Victor Alyushin and Fedor Sinitsyn.
If you are infected with malicious software, use the Kaspersky tool directly ScraperDecryptor.zip to decrypt your files. The company offers instructions on how to do it do from here.
One thing is for sure: Scammers will find some way to fix their code and release the new update. So Kaspersky's tool probably has an expiration date.





