From 09.01.2014 we published about an unprecedented hacking technique used in a attack on League of Legends.
We are republishing its analysis Cloudflare trying to explain the new technique.
The ability of servers that synchronize Internet time to return more data than what they received from computers that requested time, exploited the intruders, explains Cloudflare.
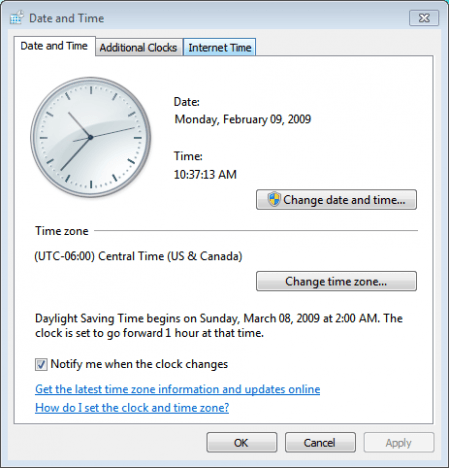
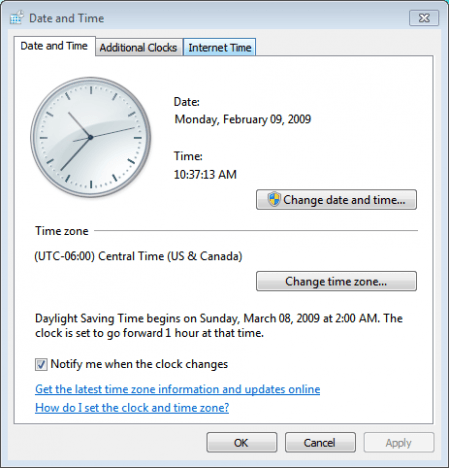 A technique that could make inaccessible popular online services was implemented on a large scale on Monday 10 February 2014, broadcasts the BBC. The company supply υπηρεσιών φιλοξενίας και ασφάλειας online, Cloudflare ανακοίνωσε ότι κατέγραψε την μεγαλύτερη επίθεση στο σύστημα συγχρονισμού computers on the Internet, with which the (unknown) target was flooded with data.
A technique that could make inaccessible popular online services was implemented on a large scale on Monday 10 February 2014, broadcasts the BBC. The company supply υπηρεσιών φιλοξενίας και ασφάλειας online, Cloudflare ανακοίνωσε ότι κατέγραψε την μεγαλύτερη επίθεση στο σύστημα συγχρονισμού computers on the Internet, with which the (unknown) target was flooded with data.
The technique concerns the so-called
network time Protocol, the protocol for synchronizing computer hours connected over the Internet, that is
tens of millions of computers. The target of "the largest NTP attack" remains unknown, according to Cloudflare, although it is located in Europe. It is a distributed denial of service (DDoS) attack that sent data with far greater force than what is currently believed to be the largest cyberattack of all time. Clouflare recorded 400 Gigabits per second, when the Spamhaus attack in 2013 was 100Gigabit weaker. NTP server response to a single target, uploading much more data on its back. As a result, the target received incredible volume
data and finally, to be catalyzed.
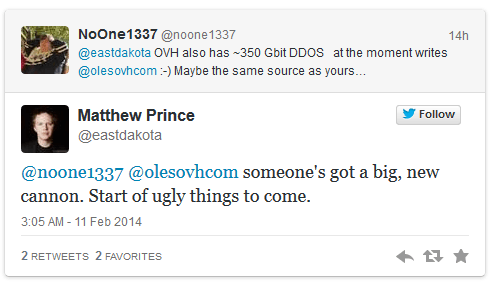
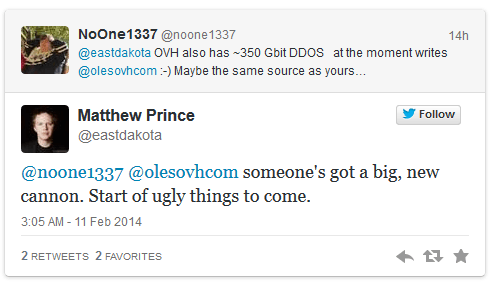
Cloudflare head Matthew Prins attributed the attack to the security holes of the NTP protocol that was developed when the outlook for cyber attacks was not visible (1985), and in a role of Cassandra, predicted by writing on Twitter that this blow would mean the beginning of many tribulations . It is noteworthy that the probability of exploiting the loopholes of the NTP protocol is being discussed for months.
BBC News, In.gr Technology
Join the 2.087 registrants.
 A technique that could make inaccessible popular online services was implemented on a large scale on Monday 10 February 2014, broadcasts the BBC. The company supply υπηρεσιών φιλοξενίας και ασφάλειας online, Cloudflare ανακοίνωσε ότι κατέγραψε την μεγαλύτερη επίθεση στο σύστημα συγχρονισμού computers on the Internet, with which the (unknown) target was flooded with data.
A technique that could make inaccessible popular online services was implemented on a large scale on Monday 10 February 2014, broadcasts the BBC. The company supply υπηρεσιών φιλοξενίας και ασφάλειας online, Cloudflare ανακοίνωσε ότι κατέγραψε την μεγαλύτερη επίθεση στο σύστημα συγχρονισμού computers on the Internet, with which the (unknown) target was flooded with data.