As soon as 24 hours after the release of the 3.6.4 security update from the Joomla project that identified two critical security flaws, hackers had already begun to look for unpatched systems and then massive scans on the Internet began.
The two vulnerabilities are listed as CVE-2016-8870 and CVE-2.016-8.869. The first allows attackers to remotely creation accounts on Joomla websites, while the second allows the elevation of account privileges to administrator level.
Η team of Joomla, and Davide Tampellini, the Joomla engineer who discovered the last flaw, refused to release any technical details about the second flaw. But many malicious researchers reverse-engineered the 3.6.4 update, picked apart the modifications, and managed to discern the exploit's methodology. So they created numerous weaponized exploits that were released online.
Sucuri's security team, which carried out reverse engineering at 3.6.4, published a proof-of-concept PoC and added the exploit code to its web firewall.
So Sucuri gained the ability to detect hacking attempts for both of these security blanks. The company reported that about 24 hours after the release of 3.6.4 from Joomla saw three IP addresses from Romania hit some of Joomla's biggest sites around the world.
The attackers tried to exploit the two errors and create a user named "db_cfg" and password "fsugmze3 ″.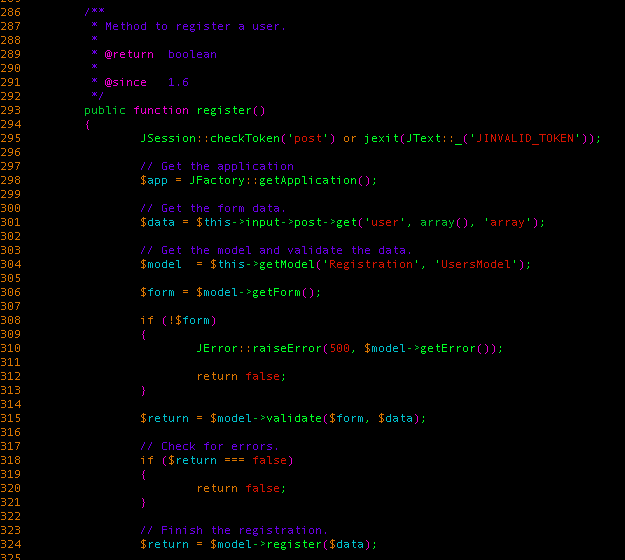
Twelve hours after that, the three IPs began mass scans on the internet, searching for every Joomla website.
Shortly afterwards, a second perpetrator using an IP from Latvia began his own mass scans, using random user account names with "ringcoslio1981@gmail.com" as the email address.
Watch these IPs
82.76.195.141
82.77.15.204
81.196.107.174
185.129.148.216
Sucuri advises webmasters to search Joomla! archives logging their website for the above IP addresses.
Attackers will generally try to access the following URL:
/index.php/component/users/?task=user.register
“We believe that any Joomla website! that has not been updated is already in jeopardy, "said Daniel Cid, Founder and CTO of Sucuri.
"Every Joomla site on our network has been hit (and blocked by Sucuri Firewall) and I guess it has happened on every site."
The exact same thing happened last year, when the Joomla project fixed the zero-day CVE-2015-8562 in version 3.4.6, which was released in mid-December. By the end of the year, attackers were performing an average of about 16.600 scans per day trying to exploit the flaw.





