Microsoft he said this week that it enabled TLS 1.3, the latest version of the security protocol, in the latest versions of Windows 10 starting with build 20170.
The company states that TLS 1.3 is enabled by default in IIS / HTTP.SYS and that for old Microsoft Edge and Internet Explorer administrators should enable it from Internet Options in the Advanced section.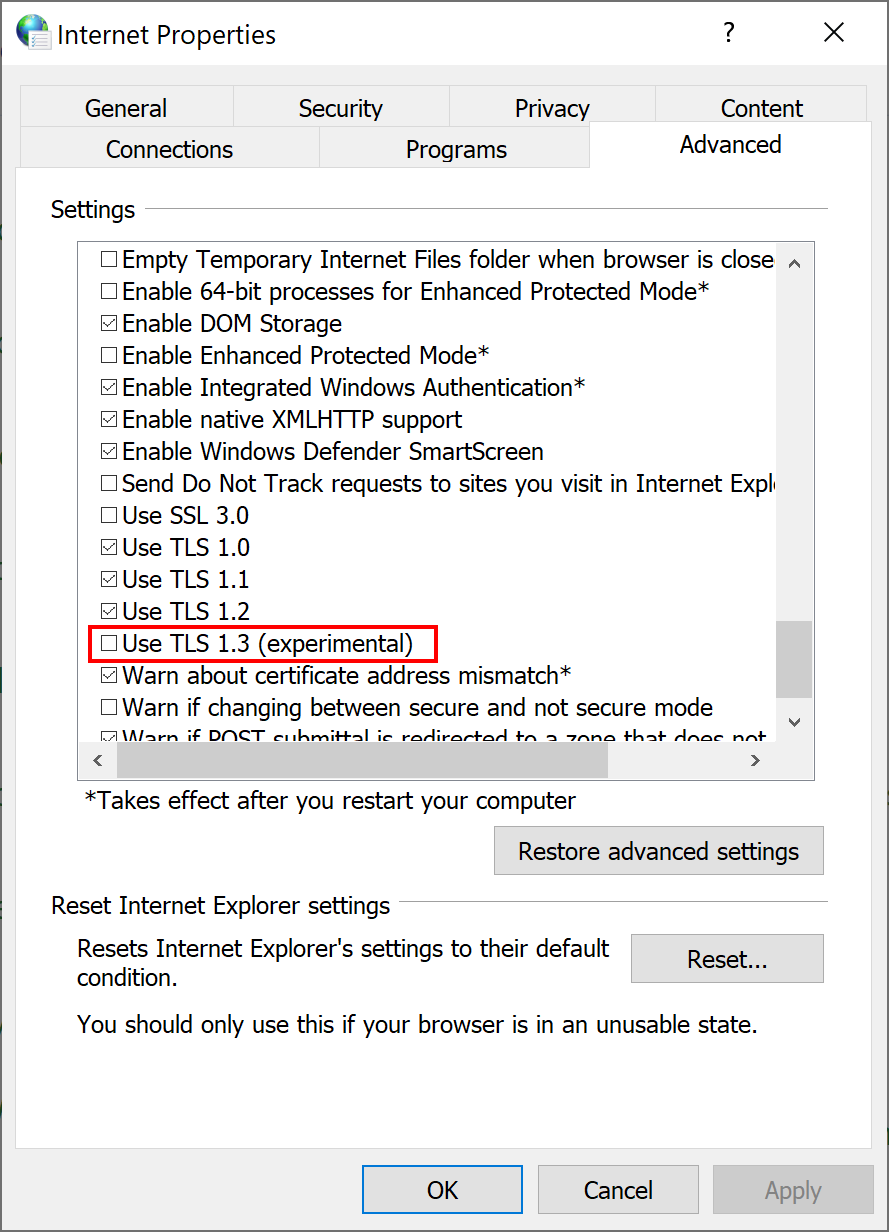
The new Microsoft Edge supports TLS 1.3 with no additional settings according to Microsoft.
Enabling TLS 1.3 in the latest versions of Windows 10 is the first step towards the wider adoption of the security protocol in Windows 10. The company has not revealed when it intends to enable it in the stable versions of Windows 10.
It's probably unlikely we'll see TLS 1.3 enabled in the next update capabilities Windows 10 version 20H2. The new protocol will probably roll out to everyone with Windows 21 version 1H10, next year's first feature update. This will coincide with the deactivation of TLS 1.0 and 1.1 that Microsoft has announced will not happen before Spring 2021.
TLS 1.0 and TLS 1.1 will not be disabled by default for either program browsing of the company until Spring 2021 at the earliest. Companies wishing to disable TLS 1.0 and TLS 1.1 before this date can do so using Group Policy.
The TLS 1.3 promises better security and performance than older protocols. Microsoft advises developers to start testing TLS 1.3 in their applications and services as soon as possible. Windows 10 will support three cipher suites to reduce complexity and guarantee "specific security properties".
Supported cipher suites are:
- TLS_AES_128_GCM_SHA256
- TLS_AES_256_GCM_SHA384
- TLS_CHACHA20_POLY1305_SHA256
The third cipher is not enabled by default.
The protocol allows for encryption earlier in the handshake, which provides greater security by preventing interference from malicioususers. TLS 1.3 encrypts the client certificate, so the ID card client identity remains private and no renegotiation is required for secure client authentication.





