Check Point security researchers have spotted a new type of social engineering attack to deceive those who work from home. The goal is personal information, money and the introduction of malware into a corporate network.
During the pandemic, many people work from home. This offers cyber criminals the opportunity to attack their employees as well as their employers.

What is Vishing?
Vishing is a variant of electronic "phishing", where the voice - V for the English term "voice" - plays a very important role. Fraudsters call employees and impersonate a specific employee to gain access to certain parts of the network, information or skills, such as functions for transport company money.
The attacks discovered by Check Point are highly sophisticated:
Hackers use it LinkedIn to find out which employee has access to it through information that is stored and represents some large company. In addition, security researchers have discovered that criminals in English-speaking countries recruit scammers who speak very good English to read a text when they make their phone call.
In addition, fraudsters are constantly changing phone numbers to call their targets, to prevent them from being located and blacklisted. Vishing attacks claim that a company executive is calling. The calls often claim that the executive comes from the financial, legal or human resources department.
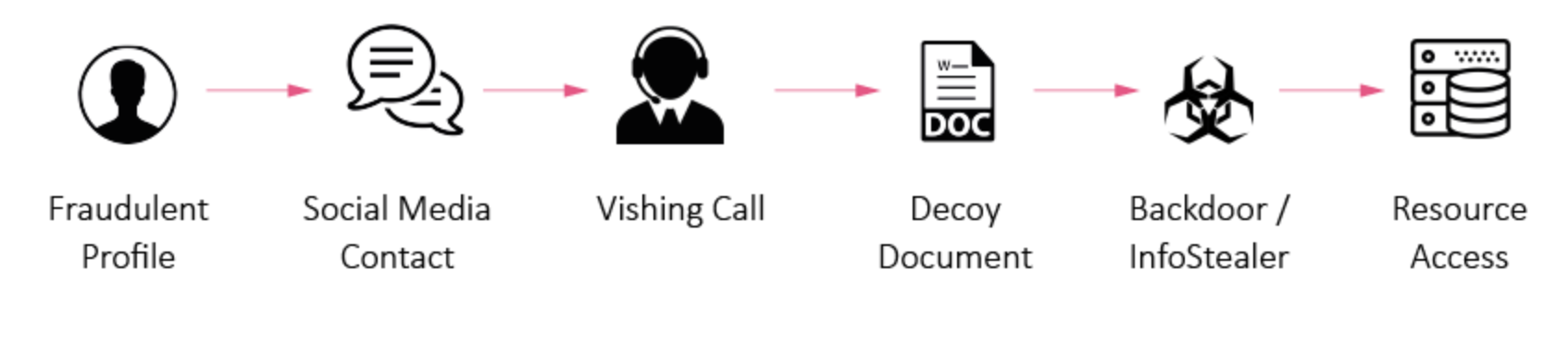
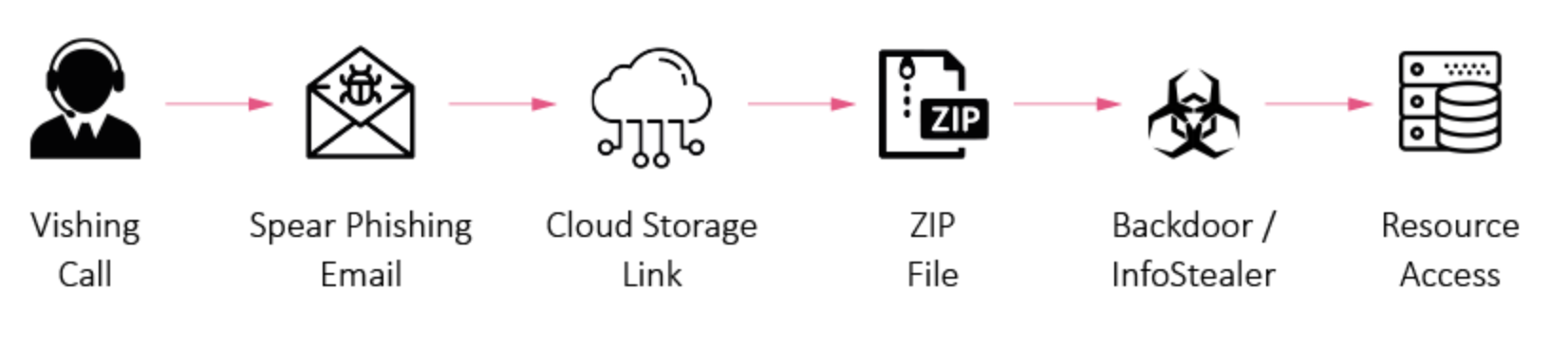
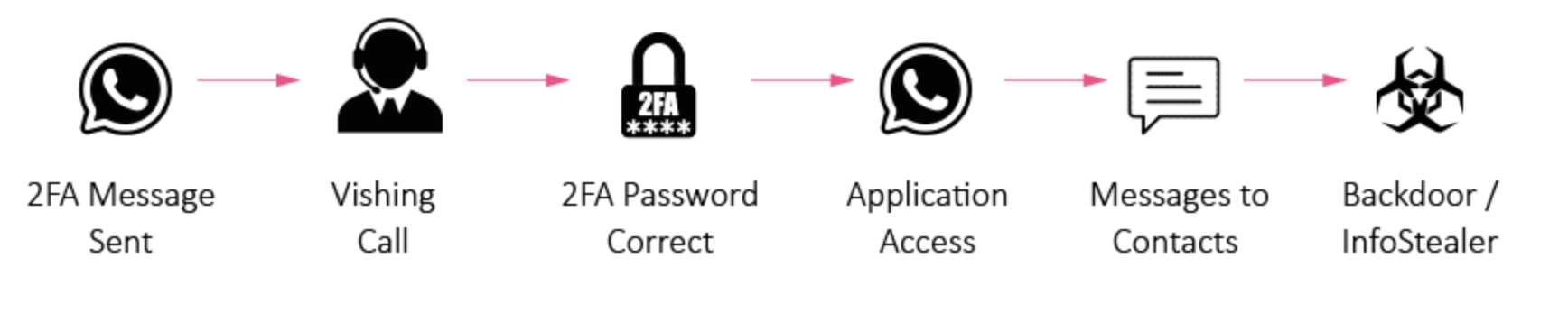
Different methods of attacking with graphics:
1.
2.
3.
Employees at home are very popular targets, because teleworkers are alone at home and of course can not easily check if the person talking to them on the phone is the one who claims.
CISA also warned in August 2020
Check Point observations on the new attack confirm the "fishing" warnings that issued in August (PDF) by the Cyber Security and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI). Both drew attention to targeted attacks against US companies and also stressed that teleworkers would be the main target of the calls.
Vishing: A new danger for teleworkers
Commenting on the new attacks, Lotem Finkelsteen, Director of the Threat Division market of Check Point Software Technologies, said:
"Fishing is one of the most dangerous threats facing teleworkers today and fraud is rarely detected. We have seen a growing number of multi-layered cyber attacks using vishing. First, vishing helps hackers learn more about their targets before the main attack. On the other hand, it deepens the most famous phishing. Vishing is also becoming the nucleus of major attacks, where victims are tricked into revealing 2FA codes via SMS or accessing specific systems - as happened in the big Twitter hack earlier this year.
Although they all refer to the US and people using LinkedIn to reveal too much personal information about themselves, their workplace and their employer, the attacks are likely to take place in other countries as well. world.





