Imagine opening a file with WinRAR, and install a malware on your system. The WinRAR application, a widely used one auxiliary program data compression and decompression. But according to the latest information from THN a flaw allows hackers to distribute malware. A security researcher from Israel, Danor Cohen (An7i) found that a feature allows spoofing in data that compresses the application. Let's see how.
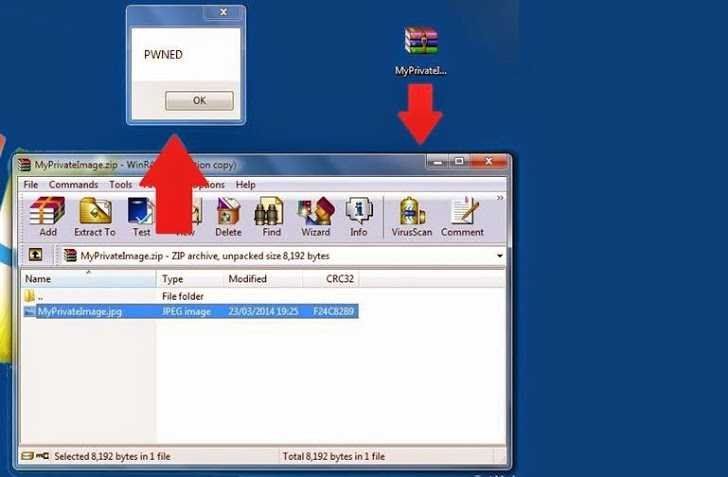
The hacker reports that by modifying a file name and expanding it within the traditional archive, it can hide binary malicious code within a file that represents .jpg, or .txt or any other form.
Using one tool Hex editor, parsed a ZIP file and noticed that the app adds some custom properties to a file, which usually has two name references to the properties. The first name is the original file name (FAX.png) and the second name is again the file name (FAX.png). The file properties are displayed in the WinRAR GUI window.
Danor renamed the file to FAX.EXE and extended the malicious FAX.EXE file to FAX.PNG. After everything is easy, prepare a separate ZIP file, which contained a malware file "FAX.exe", but displayed it as "FAX.png" to the end user.
Security firm IntelCrawler also published a report, which reveals that cybercriminals are using this zero-day vulnerability to target aerospace companies, Military subcontractors, embassies, as well as many other companies.
Using this technique, an attacker can install any malware in a very convincing way in the systems he chooses.
Danor managed to run it exploit successfully applied to the 4.20 version of the application, but IntelCrawler has confirmed that the vulnerability is compatible with all versions of the popular application including the latest V.5.1.