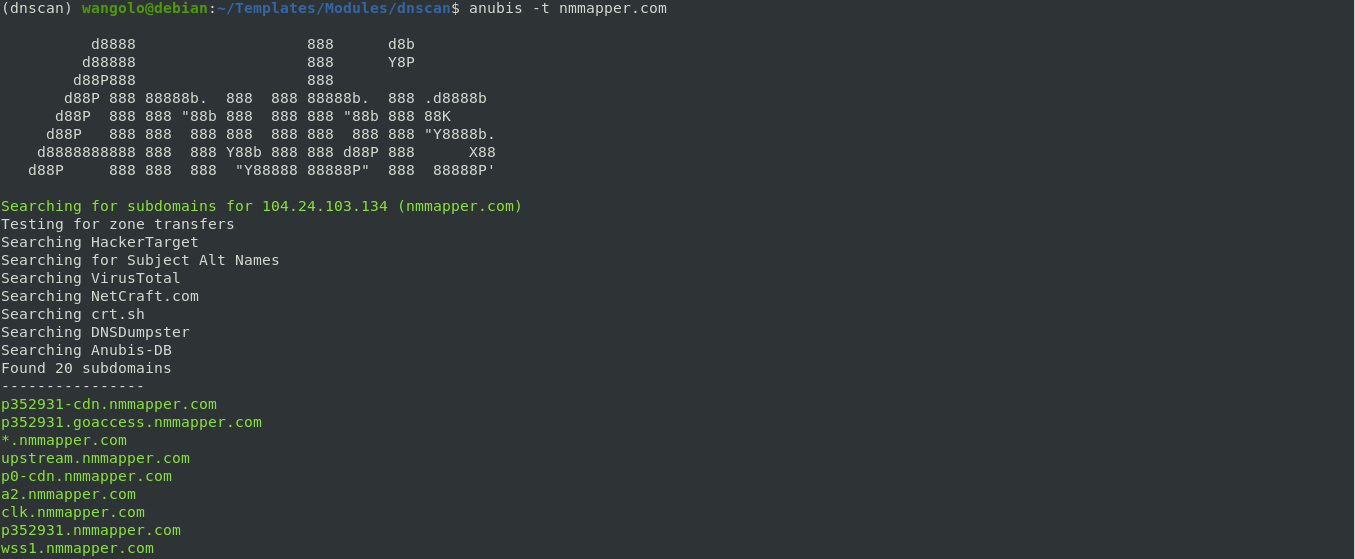
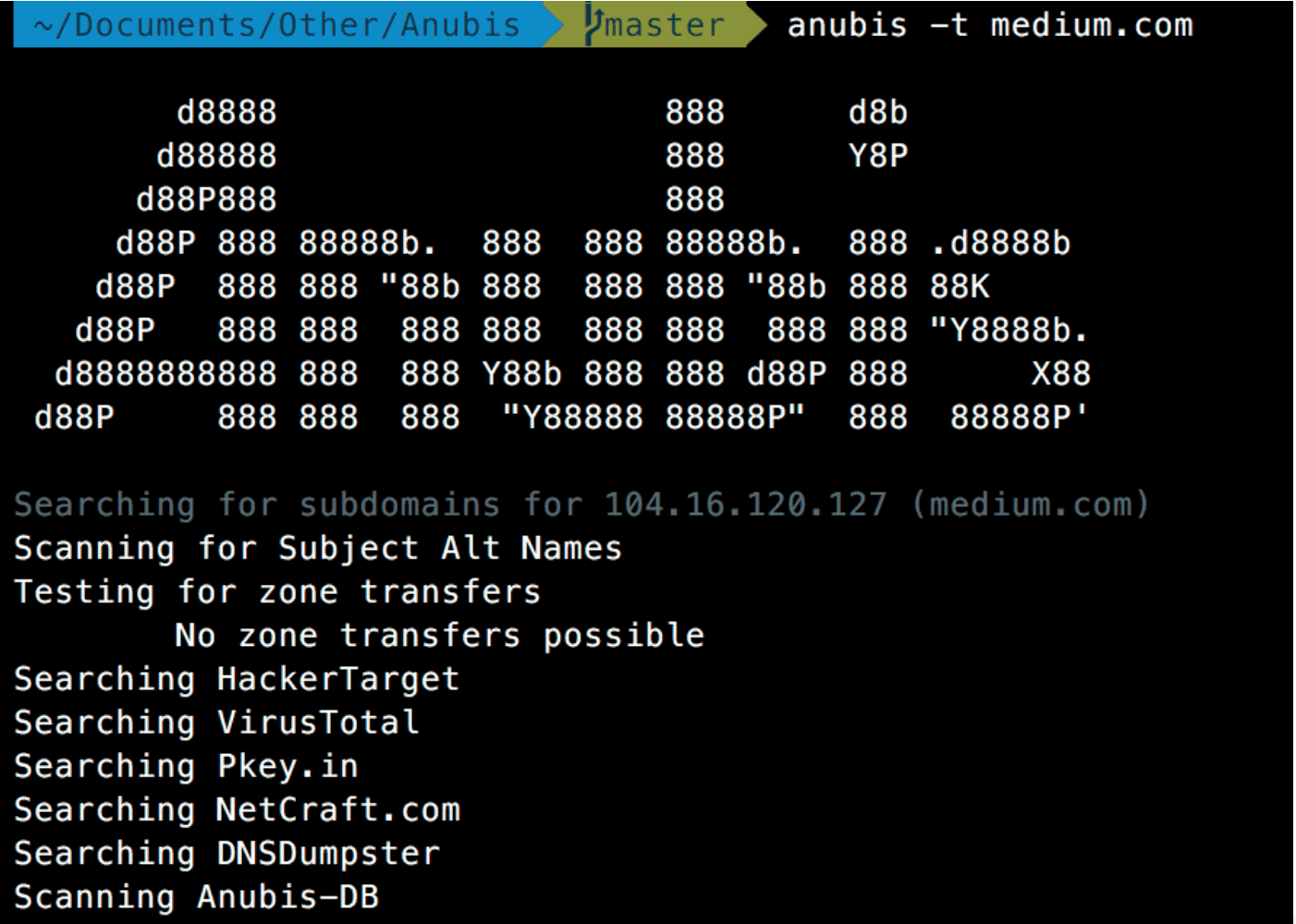
Anubis is one tool collection subdomains. It collects data from various sources, including HackerTarget, DNSDumpster, VirusTotal, Google, Pkey, and NetCraft.
Anubis has one more program which helps it discover the subdomains, the AnubisDB.
Specifications
- Gathers data from a variety of sources to provide one of the most comprehensive tools for finding subdomains.
- It is able to identify all the key servers behind the domains and export any IP addresses.
- It is also able to extract information from less used but potentially efficient "routes", including DNSSEC subdomain lists and zone transport.
Installation
sudo apt-get install python3-pip python-dev libssl-dev libffi-dev
pip3 install anubis-netsec
ή
git clone https://github.com/jonluca/Anubis.git cd Anubis pip3 install -r requirements.txt pip3 install
Use
Usage: anubis -t TARGET [-o FILENAME] [-noispbarv] [-w SCAN] [-q NUM] anubis -h anubis --version Options: -h --help show this help message and exit -t --target set target (comma separated, no spaces, if multiple) -n --with-nmap perform an nmap service / script scan -o --output save to filename -i --additional-info show additional information about the host from Shodan ( requires API key) -p --ip outputs the resolved IPs for each subdomain, and a full list of unique ips -a --send-to-anubis-db send results to Anubis-DB -r --recursive recursively search over all subdomains -s --ssl run an ssl scan and output cipher + chain info -w --overwrite-nmap-scan SCAN overwrite default nmap scan (default -nPn -sV -sC) -v --verbose print debug info and full request output -q --queue-workers NUM override number of queue workers (default: 10, max: 100) --version show version and exit Help: For help using this tool, please open an issue on the Github repository: https: / /github.com/jonluca/anubis
Application snapshots
You will find a user guide for the program here.





