Dll Hijack Detect: DLL hijacking is a type of computer hack that forces programs to load malicious Dynamic Link Libraries, instead of the intended (ie clean and official) libraries on a Windows system.
Programs that do not specify legitimate paths to libraries are vulnerable to pirated DLLs as Windows in this case uses a priority based on search order to load libraries.
If attackers manage to place malicious libraries in a location with high priority, then that library has a high chance of being loaded by the application.
Since you may be confused for a moment, let's put it again in simple terms: Windows has some specific paths to folders that it looks there to find various archives, ρουτίνες και βιβλιοθήκες. Η σειρά που ψάχνουν τους φακέλους έχει προτεραιότητες, δηλαδή πρώτα θα ψάξουν στο c:\windows\system32\ , αν δεν βρουν τίποτα σχετικό θα πάνε στο c:\windows\system\ κλπ κλπ. Βέβαια η αναζήτηση αυτή θα γίνει μόνο αν οι προγραμματιστές που έφτιαξαν κάποιο program δεν αναφέρουν ακριβώς στο πρόγραμμα που να ψάξει να βρει μία βιβλιοθήκη (που αν είναι εξειδικευμένη τότε συνήθως είναι εντός του φακέλου που έχει εγκατασταθεί το πρόγραμμα) , αλλά απλά του λένε βρες το τάδε dll αρχείο. Οι hakers γνωρίζοντας αυτή την λεπτομέρεια προσπαθούν να τοποθετήσουν στο υπολογιστή σας χακαρισμένα dll αρχεία με κακόβουλο λογισμικό σε θέσεις με υψηλή προτεραιότητα αναζήτησης για τα Windows.
Unfortunately users can not do anything about it as it is not always clear whether the paths to the folders are set correctly or not, in applications running on the system. It is up to the developers to make sure that the paths in the programs are set correctly before giving them to the public for download.
Of course, as an end user, you can use various control programs, such as Dll Hijack Detect, to scan your computer for possible jamming.
The program Dll Hijack Detect detects all DLLs loaded by the processes currently running on the system. It also inspects all locations that contain libraries and that could be malicious files, check if a loaded library is displayed multiple times in different folders, determines which library is being loaded at the moment, and finally warns you if it is possible to get rid of it.
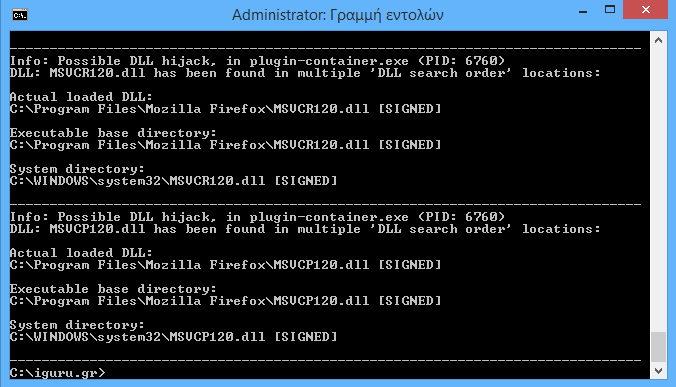
It is not necessary for every finding to be wrong. The above findings, for example, are clear, even if the libraries have been found in multiple locations in the system.
The program supports the / unsigned parameter which ignores the signed DLLs and thus greatly reduces the flow of results.
Keep in mind that the program Dll Hijack Detect is open source, free, and works under the command line (command prompt). See below for its instructions for use:
- Download its 86-bit or 64-bit version Dll Hijack Detect depending on your computer. Prefer the corresponding exe file.
- Place the executable exe file in a folder on your computer.
- Press the Windows key, and type cmd.exe in Search programs and files, right-click on the result, and select "Run as administrator" to open a command prompt with increased privileges.
- Go to the location where you have the program installed.
- Run dll_hijack_detect_x64.exe or dll_hijack_detect_x86.exe without parameters to scan the system.
- If you want, you can add / unsigned at the end of the command to show you vulnerable DLL files if of course there is even one of those that is unsigned.
All you have to do is look at the results and then check them one by one to see if your DLL files on your system are bad.
Tip: You can add "> C: \ apotelesmata.txt" (without the "") at the end of the command prompt to save the results to the APOTELESMATA.TXT file at the beginning of C:.
Note: You may need to install it Visual C ++ Redistributable Packages for Visual Studio 2013 to run the program.
Download the Dll Hijack Detect from here.





