A security researcher has discovered a new 0day vulnerability in most versions of Windows 10 that allows creating files in operating system folders.
Exploiting the flaw is important and intruders can use it to launch their attack after the initial infection of the target server, although it only works on machines with Hyper-V enabled.

Researcher Jonas Lykkegaard published a tweet last week showing how a non-privileged user can create an arbitrary archive in the “system32” folder, which contains important files for the operating system Windows and the installed software.
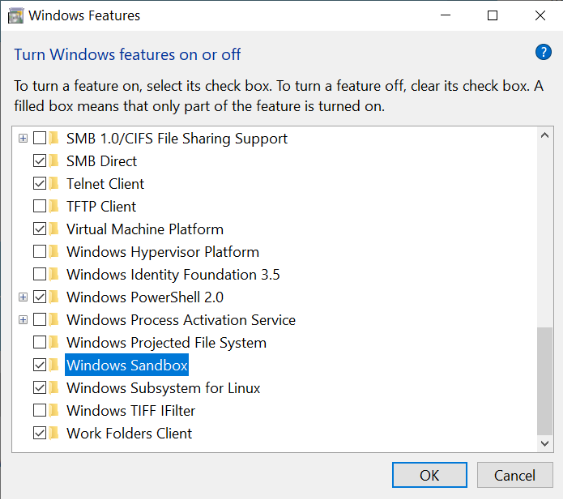
However, this only works if Hyper-V is already enabled, which limits the range of targets, as the option is disabled by default and is available in Windows 10 Pro, Enterprise and Education.
Hyper-V is Microsoft's solution for building virtual machines (VMs) in Windows 10. Depending on the physical resources available on the host, at least three virtual machines may run.
An average user may never get this feature to work, but they can run Windows Sandbox, an isolated environment for running programs or loading untrusted websites, without the risk of infecting the normal operating system. system of Windows.
Microsoft introduced it Windows Sandbox with the May 2019 Update, in Windows 10 of version 1903. This feature automatically activates Hyper-V.
To show the vulnerability, Lykkegaard created a blank file in system32 called phoneinfo.dll. Making changes to this folder requires increased permissions, but these restrictions "go for a walk" when Hyper-V is enabled.

So since the creator of the file is also the owner of the computer, an attacker can use it to place malicious code that will run with elevated privileges when needed.
CERT CC vulnerability analyst Will Dormann confirmed that the vulnerability exists and that exploiting it literally requires no effort from perpetrator to victim.
While this vulnerability is easy to exploit, there are more dangerous issues in Windows 10 that Microsoft should address. This is one reason why he decided to publicize the vulnerability on Twitter and not report it through Microsoft's bug bounty program.