More and more we see tools and applications cyber securitys to use docker. For example, in our guide on infringement of IP camera credentials, we used docker to limit our application.
What is Docker?
Docker is an open source platform for developing, shipping and running applications. It uses virtualization at the operating system (OS) level to create containers, which are lightweight, self-contained packages that contain everything an application needs to run: code, libraries, and dependencies. The Containers they isolate applications from the underlying system, making them secure and portable.
Docker simplifies the software management process by ensuring that what you develop and test in one environment will work reliably in another.
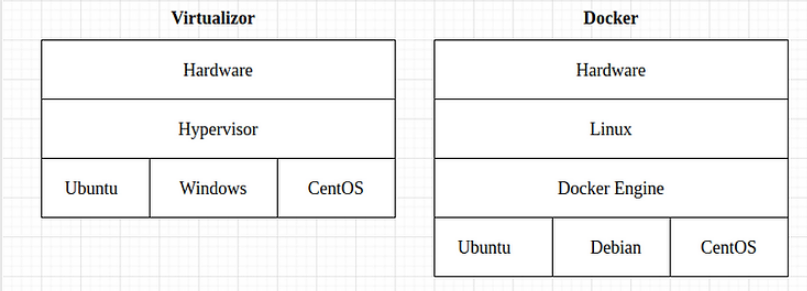
The Docker containers they replace virtual machines by virtualizing the operating system instead hardware. This means that the Docker containers they are lighter and more efficient than virtual machines and can be used to run multiple applications on a single one host machine.
Traditional virtual machines create a complete operating system environment for each virtual engine, including its own kernel, libraries, and applications. This means that each virtual machine requires its own share of the host's resources, such as CPU, memory and disk space.
On the other hand, Docker Containers they share the host's kernel and libraries. This means that the Containers they are much smaller and more efficient than virtual machines. Docker Containers they can also be started and stopped much faster than virtual machines.
They are tied to the underlying OS, so you can't run them Containers Windows on Linux systems or vice versa.
How to install docker on Linux
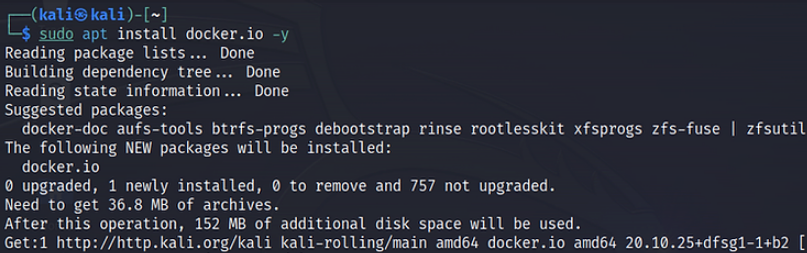
To install Docker on Debian-based Linux systems, run the following command:
sudo apt install docker.io -y
If Docker is not enabled or not active after installation, run the following commands:
sudo systemctl enable docker
sudo systemctl start docker
Install images
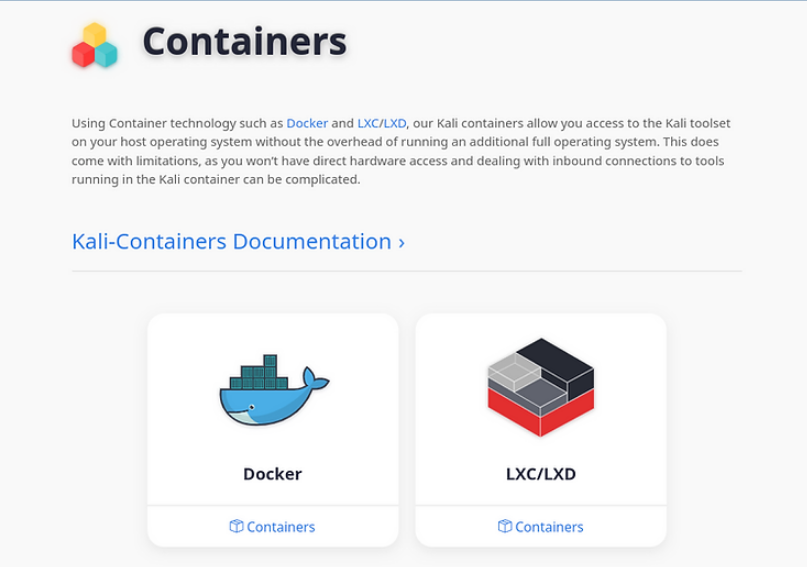
After installing Docker, you can start deploying images by pulling and running them as containers. To try the prebuilt Kali OS images from Offensive Security, download them from the official kali.org site. After selecting an application that contains Containers, you will be taken to the Docker Hub, where you can also search for other images.
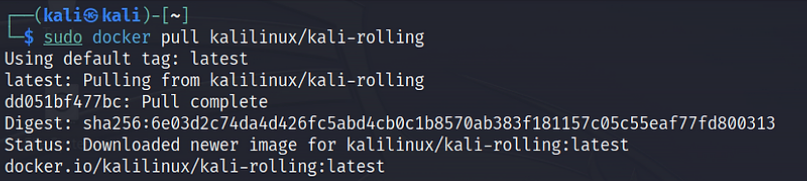
To draw one picture from Docker Hub, you can use the docker pull command with the image name.
sudo docker pull kalilinux/kali-rolling
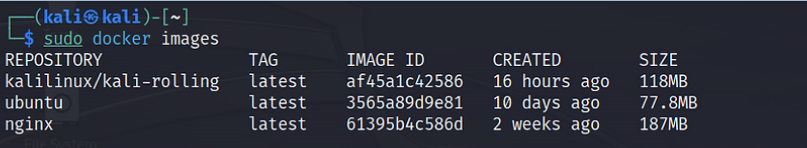
To display all your downloaded images, run the following command:
sudo docker images
It's time to deploy our docker using the command:
sudo docker run -d -t --name kali kalilinux/kali-rolling
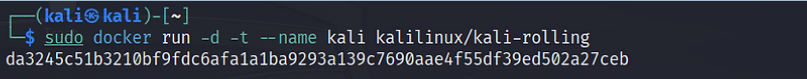
Where:
-d Run the container in detached mode. This means that the container will run in the background, even if you exit the terminal window.
-t Attach an interactive terminal to the container. This is useful for running commands inside docker.
--name Set a custom name for docker .
kalilinux/kali-rolling The name of the Docker image to run as container .
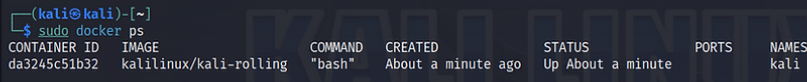
To display all running containers, run the following command:as administrator.
sudo docker ps
To connect to Docker us, we can use the “docker exec” command:
sudo docker exec -Item kali bash
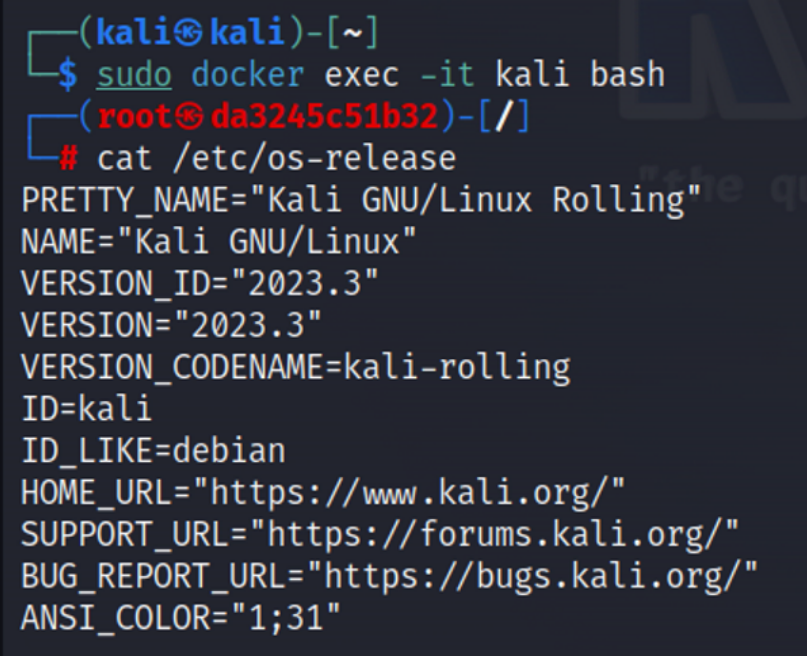
After logging in, you may realize that there are no hacking tools installed on the Docker Kali. This is because the Docker it is very lightweight and does not come with pre-installed tools. However, you can easily install any required tools or toolkits using the apt package manager.
Summary
Docker is becoming very popular in the hacker and cybersecurity industry due to the fact that it allows for lightweight virtualization and comes with all the code, libraries, and dependencies you need to run your application. This is one more tool in your toolbox to help you on your way to becoming a real hacker!





