You may have heard the term Zero Trust from your IT. Maybe not and you just felt it, when you suddenly realized that you can do almost nothing on the Internet or the Intranet. What exactly is the Zero Trust?

The Zero Trust or in Greek Zero Trust Architecture, has last become the word-key of cyber securitys. This is a strategy that helps prevent successful data breaches by removing the concept of trust from an organization's network architecture.
Based on the principle «never trust, always verifyZero Trust is designed to protect modern digital environments by leveraging network segmentation, preventing lateral breach, providing Layer 7 threat prevention, and simplifying user access control.
For the record, the logic of the Zero Trust was created in 2010 by John Kaidevag, during his tenure as Vice President and Chief Analyst at Forrester Research. He then realized that traditional security models work with the outdated assumption that they must trust everything within an organization's internal network.
According to this old model of trust, it is considered that one user's identity is not compromised and that all users act responsibly and IT can trust them.

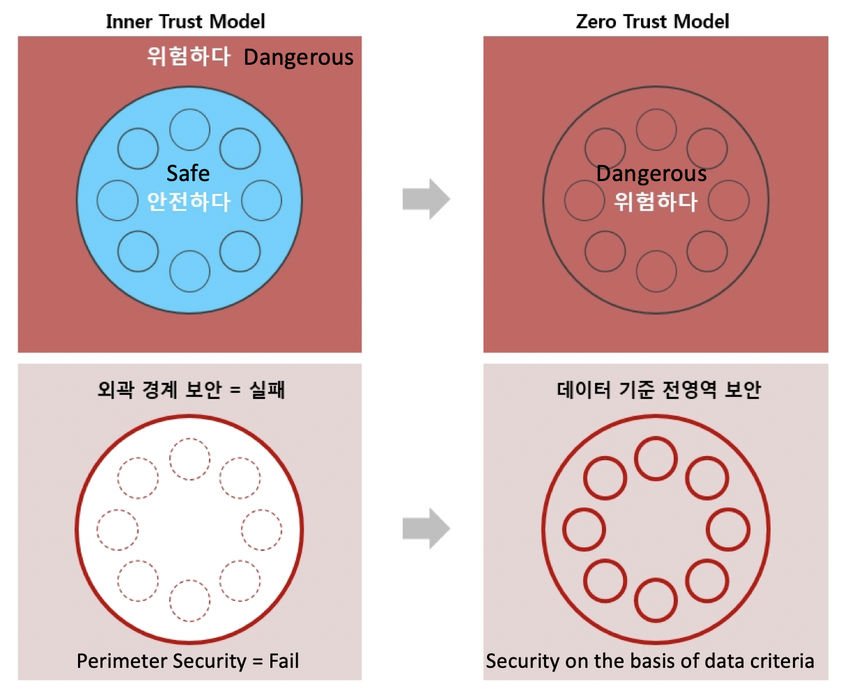
The traditional security of the computer network is based on the idea of the Castle-and-the-Trench. Castle and moat security is difficult to access when you are offline, but everyone on the net is trusted by default. The problem with this approach is that when an attacker finally gains access to the network, he has a free kingdom over everything inside.

The Zero Trust model recognizes that trust is vulnerability. He believes that once connected to the network, users, including malware and any threats that may be present on their PC, are free to access, move and view any data. In short, there is no limit to what they see.
Η philosophy behind a Zero Trust network assumes that there are intruders both inside and outside the network, so no user or machine should be trusted automatically.

So in the Zero Trust model there is always a "protect surface". It contains the most critical and valuable data, assets, applications and network services for the operations of an organization. This surface is very small in relation to the total attack surface.
And then there are Microsegmentation. This technique creates security perimeters (small zones within the protective surface) to maintain separate access for separate parts of the network. The model is not to recognize the whole system as one, but to divide each factor as a micro-segmentation and to apply to each one a perimeter application, as a way of security.
For example, a network of files in a single data center that uses security perimeters may contain dozens of separate, secure zones. A person or program with access to one of these zones will not be able to access any of the other zones without a separate authorization.
That is, if you have a company that manufactures and sells clothespins, with Zero Trust your accountant will not have access to the warehouse files or even to the materials archiving program. Accordingly, the storekeeper will not view the accounting records or the accounting program. The sellers will only see the warehouse but they will not be able to change it and from the accounting they will only see the invoices that are cut to the customers. And so on…..
So if the protective surface "falls" or even if one or two micro-parts "fall" the damage will not be universal and above all it will be easily detectable.
A key safety net of zero confidence is Multi-Factor Authentication (MFA). Anyone who has access to something will not be enough Password to enter the system. MFA simply means requiring more than one credential to authenticate a user. Entering a password is not enough to gain access.
In addition to user access controls, zero trust also requires strict controls on device access. Zero Trust systems must monitor how many different devices are trying to access their network and ensure that each device is authorized. This further minimizes the attack surface of the network.
In general, we would say that the principles of the Zero Trust are:
- Explicit verification of each user and material
- Implement the minimum possible access rights
- You assume that there is already an infringement
Once you have established a zero-confidence policy around your protective surface, you continue to monitor and maintain traffic in real time, looking for things, interdependencies, etc. that have not yet been considered, as well as ways to improve the policy.





