Metasploit is primarily one framework for developing and testing exploits. It comes with a set of tools supports that help exploit exploits, including open ports of a system.
We can use scanners to detect open ports and the services running behind them. Using the following commands we can quickly capture SMB port 445 to identify it version of the operating system.
To start metasploit, type " msfconsole At your terminal.
We will then use the following command to scan open ports
Mandate: use auxiliary/scanner/portscan/syn
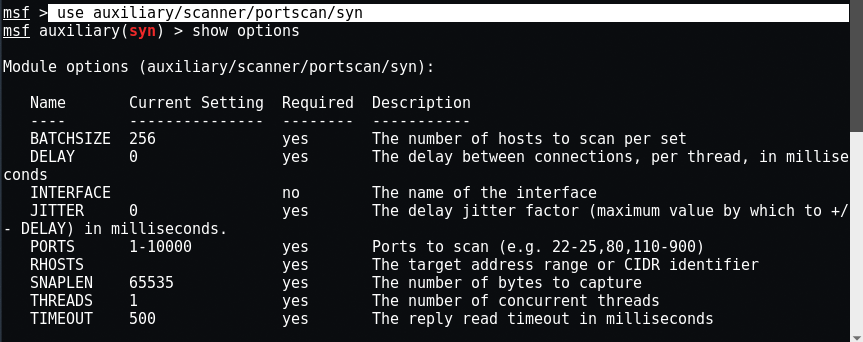
Scanners use the option RHOSTS instead of RHOST. RHOSTS can get IP (192.168.1.20-192.168.1.30), CIDR (192.168.1.0/24), but also (192.168.1.0/24, 192.168.3.0/24) as well as a list of servers (file: / tmp / hostlist.txt).
In this case, the IP (our target) is 192.168.179.142, so the command is " set RHOSTS 192.168.179.142 “. If you want to scan all ports ranging from 1-10000, then leave the PORTS command, otherwise you can choose " set PORTS 445 ".
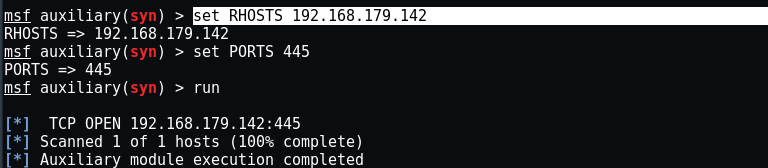
Here we will load the 'tcp' scanner by typing the command run and our results clearly show that the door 445 is open to address our destination. Then, based on our results, we will use the SMB scanner if port 445 is open.
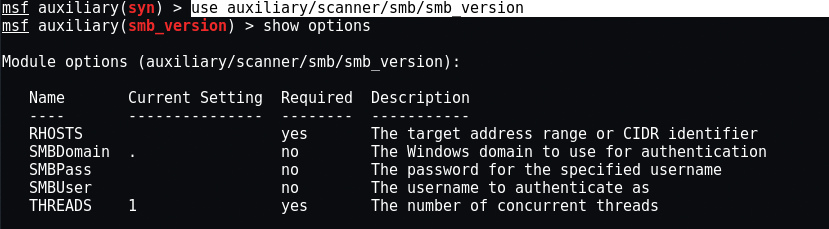
To scan an SMB, type " use auxiliary / scanner / smb / smb_versionAt the same terminal.
Specify typing the target again " set RHOSTS 192.168.179.142 ".
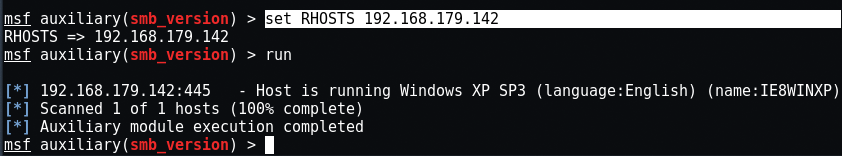
The smb_version scanner connects to each workstation on a given set of servers and determines the version of SMB service running.
As you can see, with a few simple commands in metasploit you can easily determine the operating system type of a remote machine.





