Fax machines may be a thing of the past, but they remain popular and are used by many businesses. According to a survey conducted the 2015, about 46,3 million fax machines are still in use, of which 17 million are believed to be operating in the United States.
The above figures show the seriousness of the issue to be mentioned below. Too many security researchers are concerned with repairing security gaps in modern technologies such as mobile devices, operating systems, and browsers.
Ορισμένοι ερευνητές ασφαλείας όμως ασχολήθηκαν και με την ξεπερασμένη τεχνολογία των συσκευών fax, πραγματοποιώντας attacks στα πρωτόκολλα επικοινωνίας που χρησιμοποιούν. 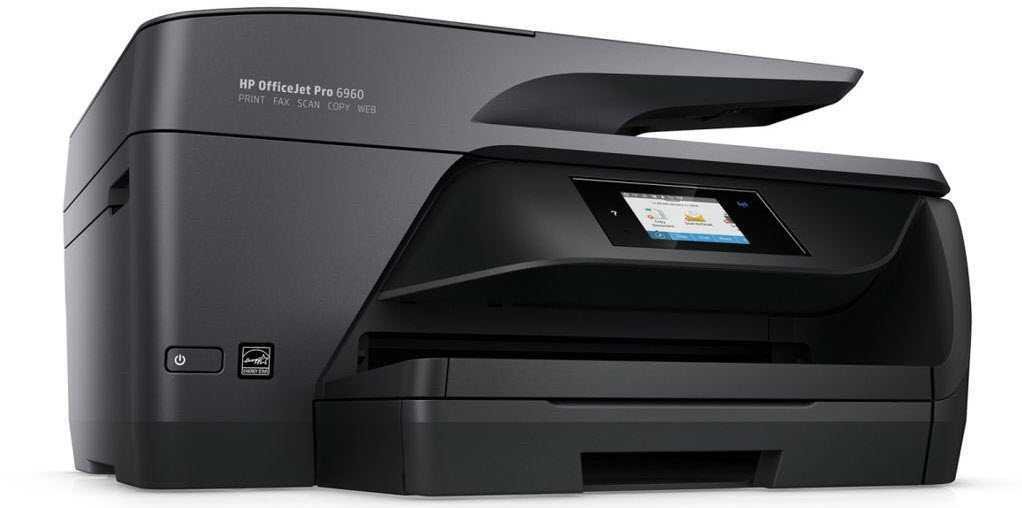
The Sunday we passed in Def With 26 held in Las Vegas, the Check Point Malware Research Team headed by Yaniv Balmas and security researcher Eyal Itkin presented their findings on fax security.
Researchers have announced the existence of security flaws in HP Officejet Pro fax machines All-in-One and specifically, on the HP Officejet Pro 6830 all-in-one printer and also on the OfficeJet Pro 8720.
Fax phone numbers are easy to find from websites των εταιρειών. Έτσι το μόνο που χρειάζεται είναι το κατάλληλο 0day. Η επίθεση είναι αρκετά απλή, αρκεί να έχετε τα εφόδια. Ο επιτιθέμενος μπορεί πολύ απλά αφού γνωρίζει τον τηλεφωνικό αριθμό του στόχου, να αποστείλει μέσω fαx ένα κακόβουλο αρχείο εικόνας.
The vulnerabilities identified included a buffer overflow security flaw based on “Devil's Ivy” (CVE 2017-976). Vulnerability allows remote code execution.
According to the researchers, an image file can be modified by adding malware ransomware, cryptominers, or spayware. Vulnerabilities in fax communication protocols can be exploited to decode and store malware in memory.
So if malware is loaded into memory the target fax is connected to some networks, malware will spread to other systems.
Check Point unveiled its findings in HP, which immediately developed fixes for device firmware. But according to the researchers:
The same protocols are used by too many fax machines and multifunction printers, or by fax machines such as fax2email. It is very likely that they are also vulnerable to attacks using the same method, which is a very serious threat to organizations that may not know how accessible their entire network is and how their most sensitive information can be exposed through of equipment sitting on the shelf and collecting dust.
________________________________________
- Julian Assange - Lennin Moreno: Clouds in relationship and limitations
- Athena get ready for Facebook's satellite
- CCleaner remove it directly from your computers





