Google has fixed an error in WebGL (Web Graphics Library) of the Google Chrome browser, which could lead to arbitrary execution code.
WebGL is one JavaScript API που χρησιμοποιείται από συμβατά προγράμματα περιήγησης για την καλύτερη απόδοση graphics 2D and 3D without the use of addons.
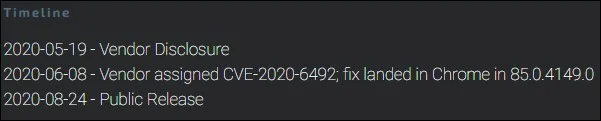
The fix for this vulnerability is already included in the beta version of the Google application and we will soon see it in the fixed version 85.0.4149.0 that will be released today according to Google.

The security loophole was discovered by Cisco Talos researcher Marcin Towalski and has been documented in CVE-2020-6492. It is very high quality and has been rated with 8.3 CVSSv3 Score.
Vulnerability triggers a vacation operation when the WebGL component fails to handle properly objects in the memory.
The CVE-2020-6492 vulnerability affects Google Chrome 81.0.4044.138 (Fixed), 84.0.4136.5 (Dev) and 84.0.4143.7 (Canary), and reported to Google on May 19.