Οι ερευνητές της ESET, κατά τις πρόσφατες αναλύσεις των banking Trojans που πλήττουν τη Λατινική Αμερική, προχώρησαν στην ανατομία του Guildma, the most powerful and advanced banking Trojan ever encountered by this team in this region.
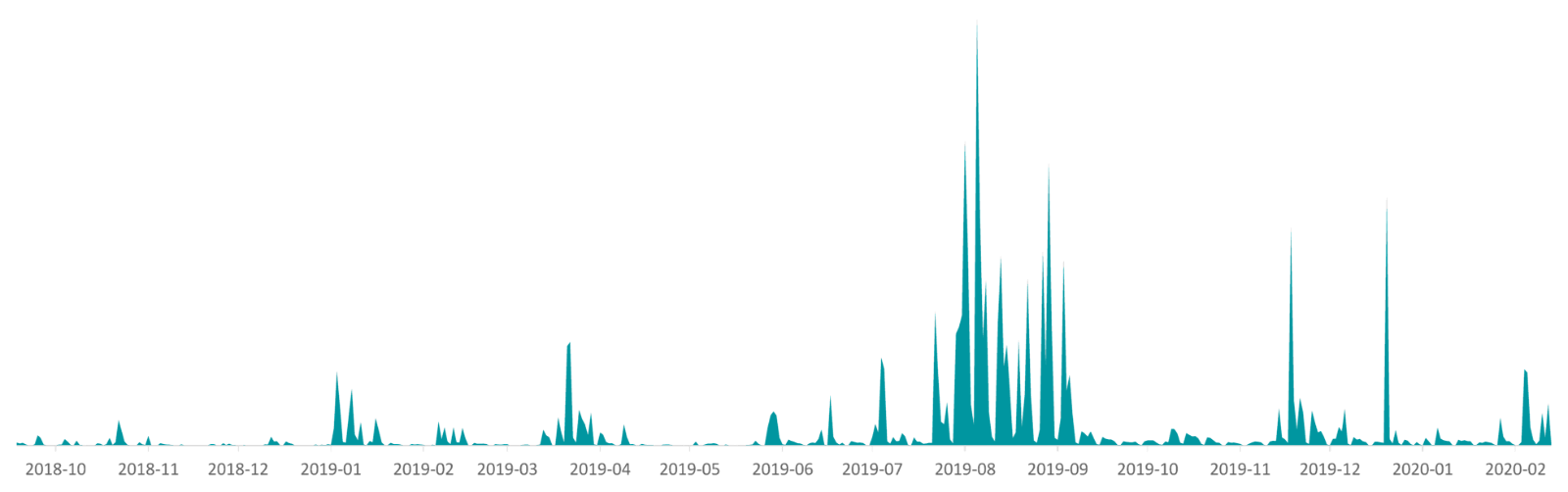
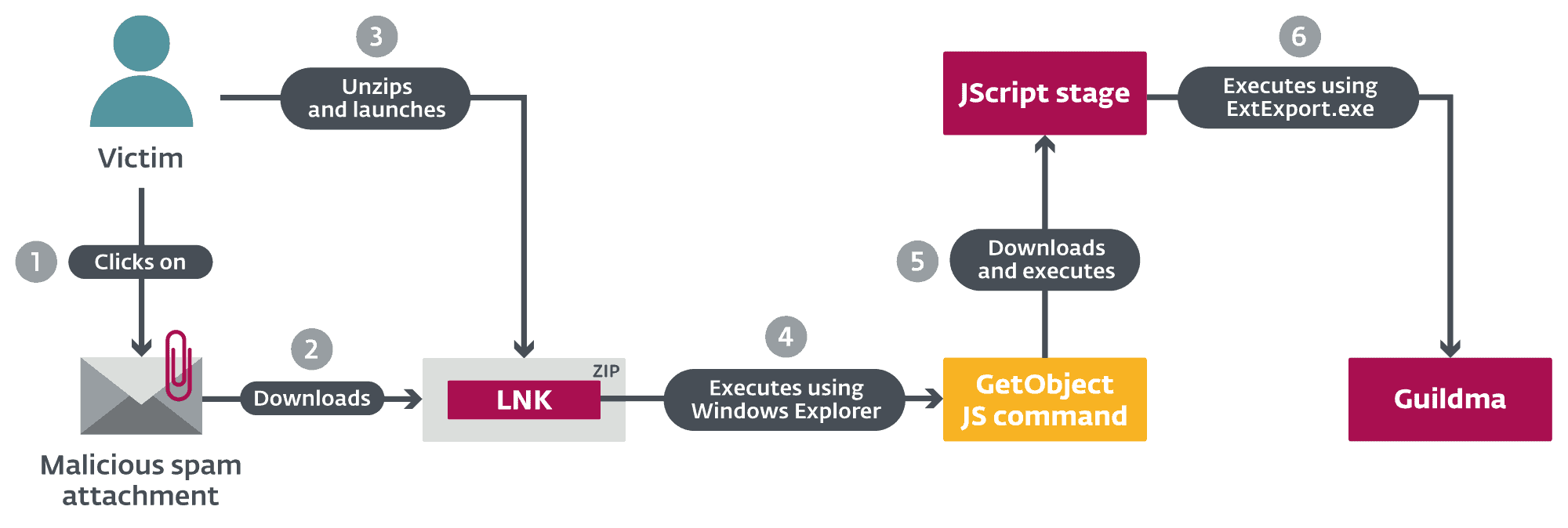
This malware specifically targets banking institutions, trying to steal credentials for email accounts, e-shops and streaming services in Brazil. It has infected at least 10 times more victims than other Latin American banking Trojans analyzed by ESET. During the peak period - a massive campaign in 2019 - ESET recorded up to 50.000 attacks per day. Guildma spreads exclusively through spam emails with malicious attachments.
In one of its latest releases, Guildma used a new way of distributing command and control servers, abusing profiles in YouTube and Facebook. However, its operators stopped using it Facebook almost immediately and, at least for the time being, they rely entirely on YouTube.
“Guildma uses very innovative execution methods and sophisticated techniques attacks. The actual attack is orchestrated by the C&C server. In this way, its operators can react more flexibly to the countermeasures that banks implement when they are attacked," explains Robert Šuman, the ESET researcher who leads the team analyzing Guildma.
Το Guildma διαθέτει πολλαπλές λειτουργίες backdoor, όπως να κάνει λήψεις screenshot, να καταγράφει πληκτρολογήσεις, να προσομοιώνει λειτουργίες του ποντικιού και του πληκτρολογίου, να μπλοκάρει συντομεύσεις (όπως απενεργοποίηση του Alt + F4, για να δυσκολεύει την εξαφάνιση των ψεύτικων παράθυρων που μπορεί να εμφανίζει), και/ή να κάνει reboot. Επιπλέον, το Guildma διαθέτει εξαιρετικά αρθρωτή αρχιτεκτονική, αποτελούμενο, σήμερα, από τουλάχιστον 10 modules. Το malware χρησιμοποιεί εργαλεία που υπάρχουν ήδη στο machine and reuses its own methods. "New techniques are added from time to time, but, for the most part, developers seem to just reuse techniques from older versions," Šuman says.
In one of the first editions of Guildma in 2019, the possibility of targeting institutions (mainly banks) outside Brazil was added. However, in the last 14 months, ESET has not detected any international campaigns outside the country. In fact, the attackers went so far as to block downloads from IP addresses outside Brazil.
Guildma's campaigns escalated slowly until the massive campaign in August 2019, when the ESET Research Team recorded up to 50.000 samples per day. This campaign continued for almost two months, reaching more than double the amount detected 10 months ago.
The trojan has changed many versions during its development, but there has usually been very little evolution between versions due to its "rigid" architecture.
Guildma has several of the key features of Latin American banking trojans. For more technical details, read the blog post «Guildma: The devil electric drives»On WeLiveSecurity.





