Kaspersky Lab's Worldwide Research and Analysis Team unveils the action of the Desert Falcons, a digital espionage organization targeting many organizations and individual high-profile figures from Middle East countries. 
Kaspersky Lab experts see this organization as the first known Arab group of "digital mercenaries" to develop and carry out complete digital espionage operations.
- The campaign has been active for at least two years. The team Desert Falcons has begun to develop and consolidate its operation within 2011. However, the beginning of the group's core action and infections through it malwareis placed in 2013. The peak of their activity is recorded at the beginning of 2015.
- The overwhelming majority of targets are in Egypt, Palestine, Israel and Jordan.
- In addition to the Middle East countries, which were the original targets, the group Desert Falconsis also active outside of this area. Overall, its members have managed to attack more than 3.000 victims in more than 50 countries worldwide, having overrun 1 million records.
- Attackers use malicious tools that they have developed themselves to launch attacks on computers Windows and devices Android.
- Her experts Kaspersky Lab have many reasons to believe that the mother tongue of the group members Desert Falconsis Arabic.
The targeted list of victims includes military and governmental organizations - and in particular, officials in charge of dealing with money laundering. The campaign also turned against executives from the health and economy sectors, top media, research and education institutions, energy providers and utilities, activists and political leaders, personal security companies, and other targets in their possession geopolitical information.
Overall, Kaspersky Lab experts have been able to detect signs of attacks over 3.000essions, to more than 50 countries, finding it intercepting more than one million files. Although the organization of the attack appears to be operating in countries such as Egypt, Palestine, Israel and Jordan, many victims have also been found in Qatar, Saudi Arabia, the United Arab Emirates, Algeria, Lebanon, Norway, Turkey, Sweden, France, the United States, Russia and other countries.
Transport, "Infection", Espionage
The primary method used by the Desert Falcons team to deliver malware loadυ ήταν το spearphishing μέσω email, μηνυμάτων σε μέσα κοινωνικής δικτύωσης και μηνυμάτων σε chat. Τα μηνύματα phishingπεριείχαν κακόβουλα αρχεία (ή linkπου οδηγούσαν σε κακόβουλα αρχεία), τα οποία μιμούνταν νόμιμα έγγραφα ή εφαρμογές. Η ομάδα Desert Falconsχρησιμοποιεί διάφορες τεχνικές για να δελεάσει τα θύματα της και να τα αναγκάσει να εκτελέσουν τα κακόβουλα αρχεία. Μία από τις πιο χαρακτηριστικές τεχνικές που uses the group is the so-called “Right-to-LeftOverride”.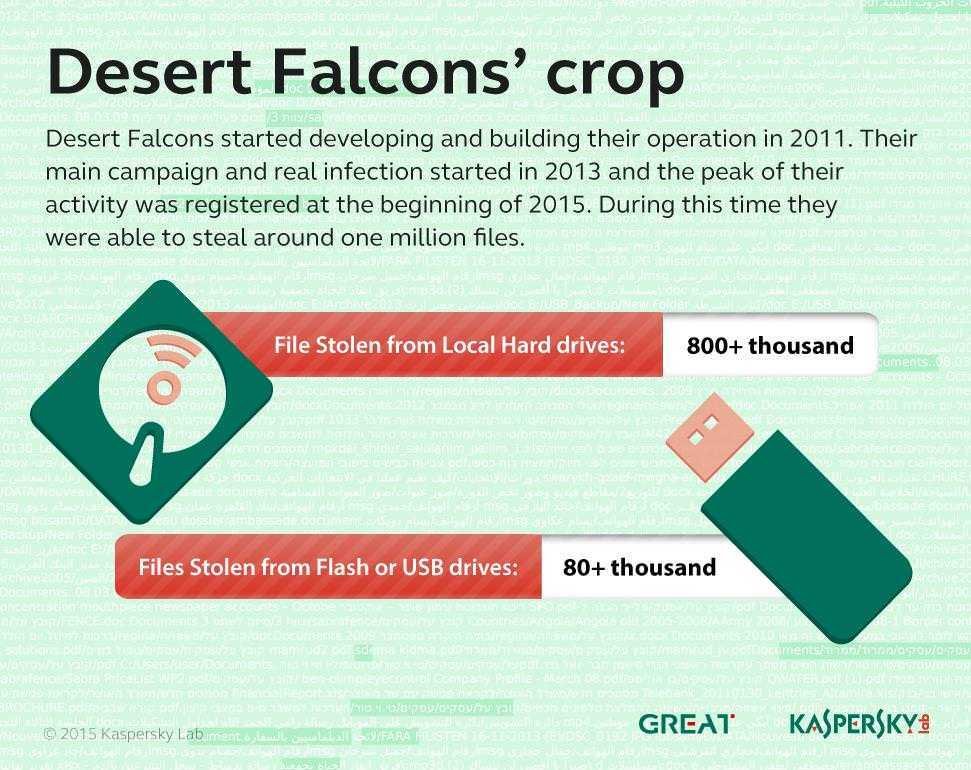
This technique takes advantage of a special character in Unicode to reverse the string of characters in the name of a file by hiding a dangerous extension in the middle of the name and placing a false file extension that looks harmless close to the end of the file name. Using this technique, malicious (.exe, .scr) files resemble a harmless PDF document or file, and even cautious users with good technical knowledge can drag and drop these files. For example, a file with a suffix ".Fdp.scr"would be presented as".Rcs.pdf".
After the victim's successful infection, Desert Falcons members use one of two different BackDocs, either their basic Trojan or DHSBackdoor, which seem to have been developed from scratch and are in constant growth. Kaspersky Lab specialists were able to identify more than 100 malware samples used by this group for attacks.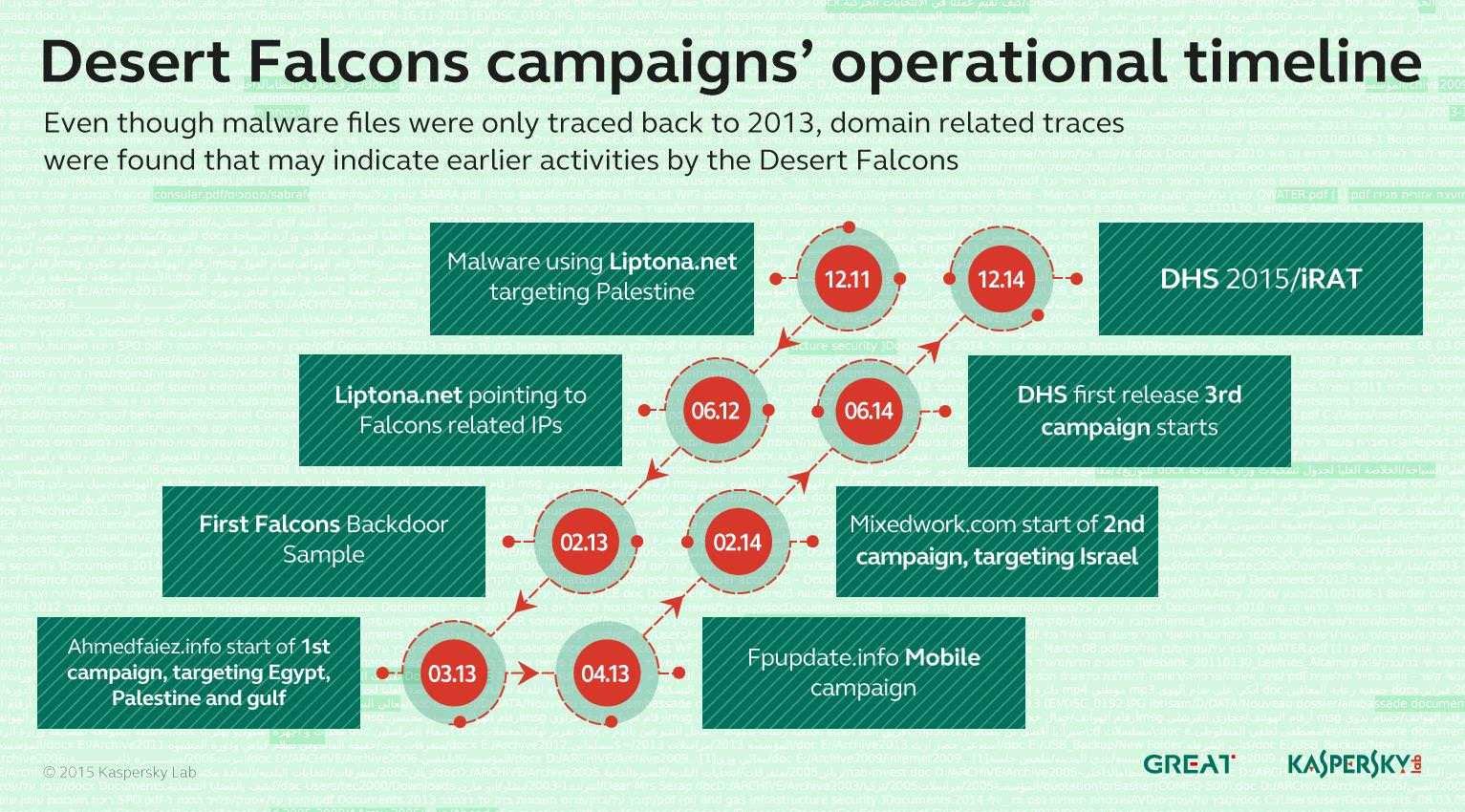
The malicious tools used have full backdoor functionality. So they can pull screenshots, να υποκλέπτουν πληκτρολογήσεις, να κάνουν uploadή downloadαρχεία, να συλλέγουν πληροφορίες σχετικά με όλα τα αρχεία Word και Excel στο σκληρό δίσκο ή τις συνδεδεμένες συσκευές USB ενός θύματος, να υποκλέπτουν κωδικούς πρόσβασης που αποθηκεύονται στο μητρώο του συστήματος (Internet Explore and Live Messenger) and make recordings. Kaspersky Lab experts also managed to detect traces of the activity of a malware, which appears to be a backdoor for Android, with the ability to intercept calls and SMS logs.
Using these tools, members of the Desert Falcons team created and managed at least three different malicious campaigns targeting different victims in different countries.
A "flock" in the secret hunt
Kaspersky Lab researchers estimate that at least 30 individuals, in three groups, shared in different countries, are running the Desert Falcons malware campaigns.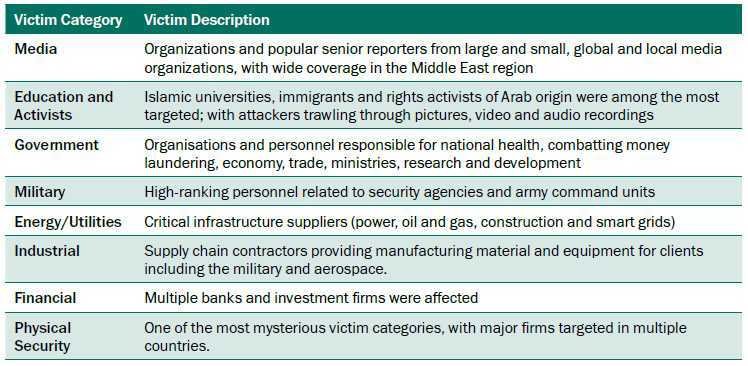
"The people behind this organization are extremely determined, active, with good technical knowledge and good information on political and cultural issues. Using only phishing email, social engineering techniques, tools and backdoors developed by themselves, the members of the team Desert Falcons have been able to "pollute" hundreds of major victims in the Middle East through their computers or their handheld devices, as well as decode sensitive data. We expect this campaign to continue to develop more Trojans and to use even more sophisticated techniques. With sufficient funding, they could acquire or develop exploits, which could increase the effectiveness of their attacks,said Dmitry Bestuzhev, a security expert and member of Kaspersky Lab's Worldwide Research and Analysis Group.
Kaspersky Lab products detect and successfully block the malware used by the Desert Falcons team.
More information about the campaign is available at Securelist.com.





