A malware loader that was described as a "project in progress" in June is now fully operational and infecting thousands of Windows home and office computers.
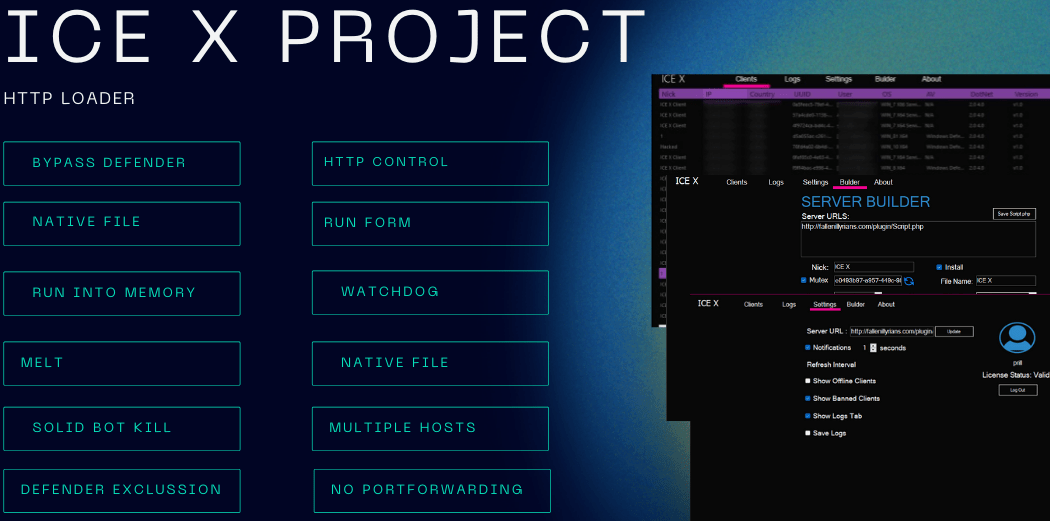
IceXLoader version 3 was discovered over the summer by FortiGuard Labs of Fortinet, which wrote that the malware's capabilities were lacking and appeared to have been ported to the Nim programming language.
However, researchers from Minerva Labs on Tuesday they said that they had found a newer version of IceXLoader – 3.3.3 – that works properly.
IceXLoader collects metadata from the system – such as the IP address, the name user and machine name, Windows version, and CPU, GPU and memory information – and sends it to a command and control (C2) server, according to the researchers.
There is one there base malware's SQLite database, and is constantly updated. According to the researchers, it "contains thousands of victim files, from private home and corporate computers."
The price of IceXLoader on the dark web was $118 (lifetime license) but at the moment we don't know how much the new version costs.
The malicious one software it initially enters systems through phishing. Emails contain a ZIP file that hosts a dropper, which drops a downloader written in .NET. This malware downloads another dropper that decrypts and injects IceXLoader.
IceXLoader directly communicates with the C2 server for further commands and additional malware. According to FortiGuard, IceXLoader version 1.0 was used to distribute the DCRat malware – or Dark Crystal RAT (a remote accesss), while version 3.0 distributed a Monero miner.
IceXLoader has a number of features designed to avoid being detected by Microsoft Defender.
Additionally, the malware is written in Nim – a newer programming language that compiles to C, C++ and JavaScript. Nim has been adopted in recent years by malicious developers trying to make their malicious code difficult to detect.
It's part of a larger trend in recent years where malware developers are turning to newer languages like Go, DLang, Nim and Rust to avoid easy detection.





