Zerodium, a company that pays up to $ 2 million for exploits on Apple's iOS, says it is lowering its price because the number of exploits targeting the platform has risen sharply recently.
In other words, the company is no longer willing to spend so much money on iOS hacks because the system just isn't what it used to be and there are a lot of security gaps.
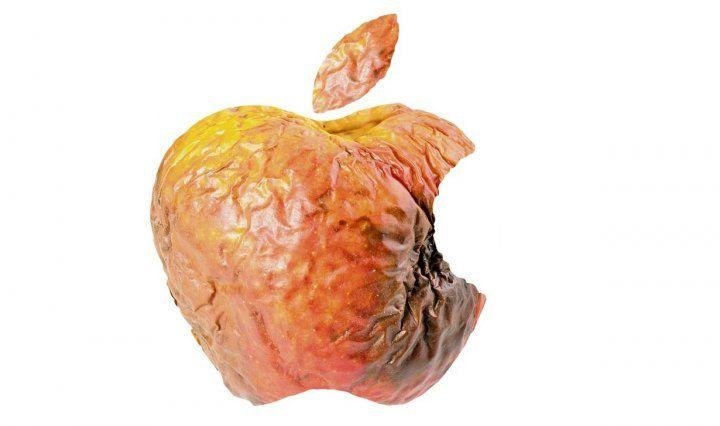
"IOS security is fucked", said Chaouki Bekrar, CEO and founder of Zerodium.
Zerodium reports that one possible reason for the increase in the number of exploits targeting iOS could be the greater number of researchers looking for errors security in Apple's operating system, as well as the jailbreaks make it possible to carefully inspect the code with reverse engineering.
As a result, the company states that it is no longer interested in specific types of iOS exploit.
“We do NOT want new Apple iOS LPE, Safari RCE, or sandbox escapes for the next 2 to 3 months due to the large number of submissions related to these vulnerabilities. Prices for for iOS one-click chains (e.g. via Safari) will likely be reduced in the near future,” Zerodium announced on Twitter.
"Only PAC and non-persistence still hold… but we see a lot of exploits bypassing the PAC and there are some persistence exploits (0days) that work with all iPhone / iPad. "Let's hope iOS 14 gets better."
Apple is expected to introduce the new iOS 14 in the fall, probably together with the new iPhone models. However, a preview of this updated versions of the operating system is expected to be announced and released at the WWDC conference, with an early beta version.





