The researchers Kaspersky malware discovered a new sophisticated system developed and used by the National Security Agency (NSA).
EquationDrug or the Equestre platform uses 116 modules to successfully track computers and steal for the secret information service.
"It is important to note that EquationDrug is not just a trojan, but a complete espionage platform, which includes a framework for conducting espionage activities by deploying special modules to get better results on the computers of selected victims," its researchers said. Kaspersky.
"Η αρχιτεκτονική του όλου πλαισίου μοιάζει με ένα μίνι-λειτουργικό σύστημα που έχει πυρήνα λειτουργίας συστήματος και χρήστη (kernel-mode και user-mode) και τα συστατικά του αυτά φαίνεται να αλληλεπιδρούν πολύ προσεκτικά μέσω μίας εξατομικευμένης διεπαφής ανταλλαγής messages."
The platform is part of its ongoing campaign NSA to infect the hard disk firmware. It replaces the older EquationLaser and is upgraded to the GrayFish platform.
Most of the unique identifiers and encoded names are tied to encrypted sections and so are unclear. Some modules can be identified with the unique identification number they use. Others again depend on other plugins to function.
Each plugin has a unique ID and a version number that defines all of the features it can offer.
Kaspersky researchers have been able to reveal 30 from the 116 modules that they believe are in NSA's super malware.
"The plugins we discovered probably represent only a small part of the attack's capabilities," the researchers report.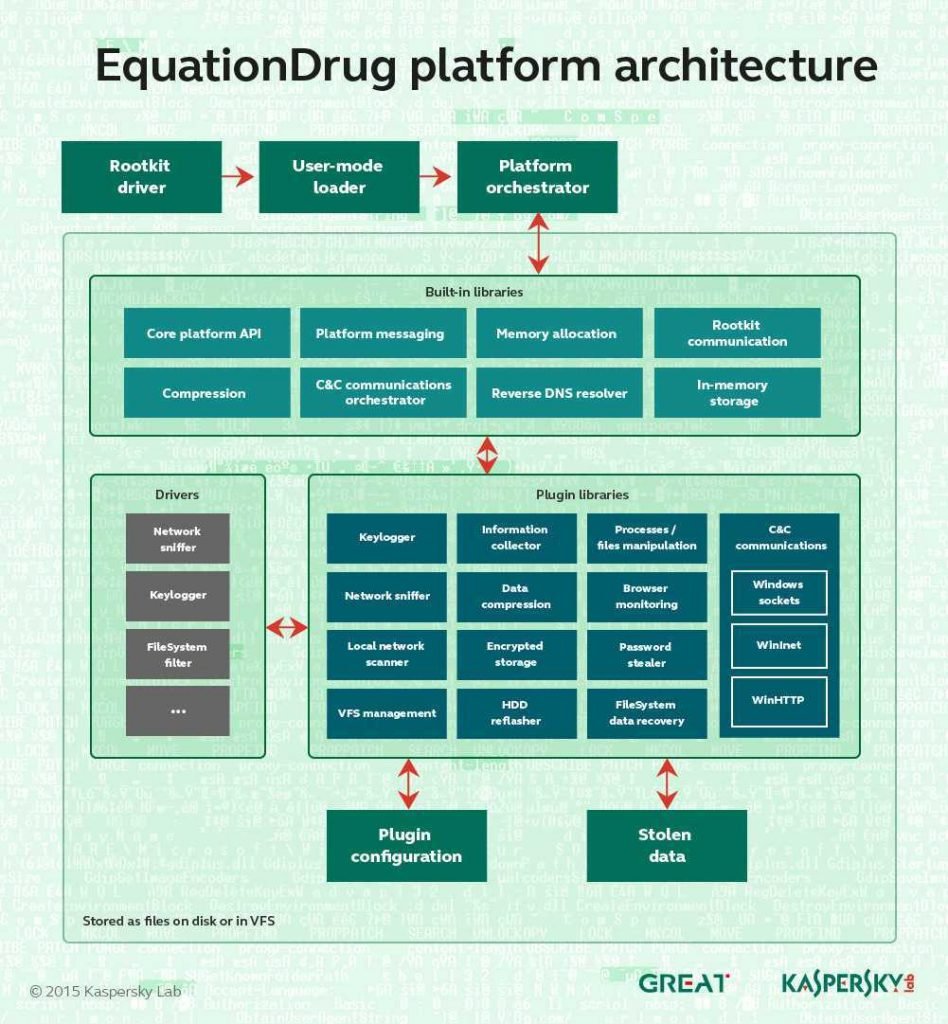
Units that have been detected so far in the NSA tool include malicious software for:
- Traffic Traffic Network for theft or re-routing
- Reversal resolution DNS (DNS PTR records)
- Computer Management
- Start procedures / stop
- Loading drivers and libraries
- Management files and catalogs
- Collection of system information
- Running version of the operating system
- Computer name detection
- Detect user name
- Location Detection
- Keyboard Layout Detection
- Time zone detection
- List of Procedures
- Browsing network resources, enumeration and access to public areas
- WMI Information Collection
- Collection of cached passwords
- Counting processes and other system functions
- Tracking user activity from web browsers in real time
- Low-level NTFS file system access based on the popular Sleuthkit framework
- Monitor removable storage units
- Passive backdoor network (running Equation shellcode from raw traffic)
- HDD and SSD firmware manipulation
- Keylogging and clipboard tracking
- Browsing history, cached passwords, and auto-fill form data collection.





