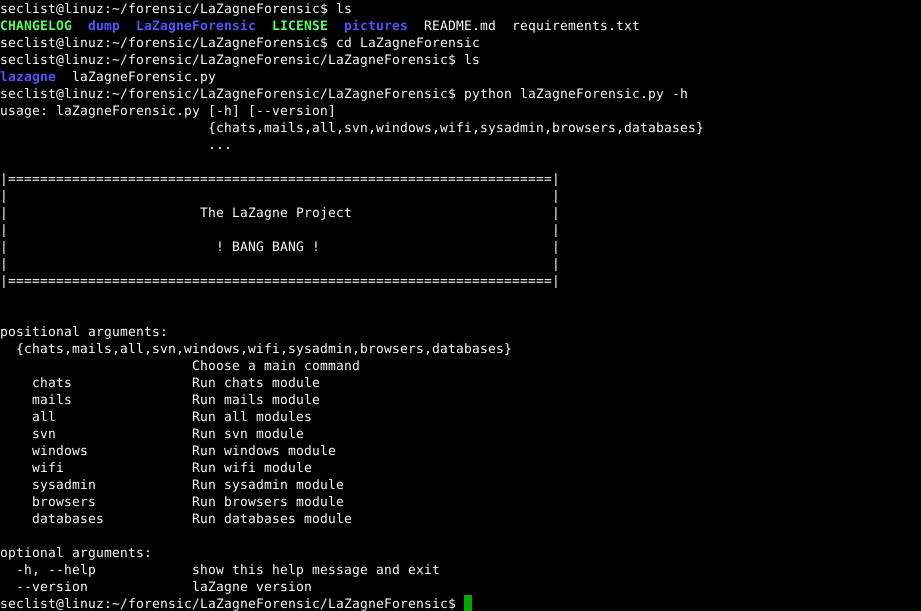
The LaZagneForensic (LZF) application allows any Windows user to recover almost any code access stored on the computer.
The LaZagneForensic program reportedly exploits the way Windows work to gain access to sensitive information stored by users each system. It is known that all passwords on Microsoft systems are stored encrypted by Windows. But as soon as the user connects to the system, they are automatically decoded, so that they can be used by the operating system.
The original LaZagne app uses an internal Windows API called CryptUnprotectData to decrypt user passwords. This API starts working with user login, otherwise it doesn't work. If the computer is not started (when the analysis is performed from a connected disk except connections) or if we do not place the application on a remote host, the passwords cannot be recovered.
LaZagneForensic was created to overcome this problem. The project is mainly inspired by Jean-Michel Picod's amazing work for them DPAPICK and Francesco Picasso for the Windows DPAPI laboratory.
That is why LaZagneForensic works after the user logs on to Windows. Then it can easily pick up passwords, and then store them in plain text.
The developer of the application even says that the only way to stay safe is to avoid storing passwords using the default Windows method.
This practically means that for your security you might want to use a third-party password manager.
We occasionally report the password manager KeePass. It is the password manager we recommend as it saves everything locally and with very strong encryption.
LaZagneForensic can recover passwords from the following programs: Outlook, Thunderbird, Chrome, Firefox, Internet Explorer, Opera, Pidgin, Filezilla, wifi, databases, Skype, etc.





