A recent update fixes a 0day vulnerability of the proletterof the Windows AppX installation (CVE-2021-43890), who used the Emotet.
An add-on to the patch Tuesday, December 2021 for the AppX installer used on Windows, Microsoft has closed the Windows AppX Installer forgery vulnerability.
The gang behind Emotet took advantage of this vulnerability to infect systems. The following is a brief overview.
The AppX-Installer used in Windows 10 and Windows 11 to install applications has a serious design flaw.
An infected payload from Emotet appears as a trusted application in the installer dialog. The Trusted App statement is displayed to users without any digital signature being evaluated. Only when the user clicks on the Trusted App link does he receive the audit notification identity from the publisher you see in the tweet below from the actual publisher of the app.
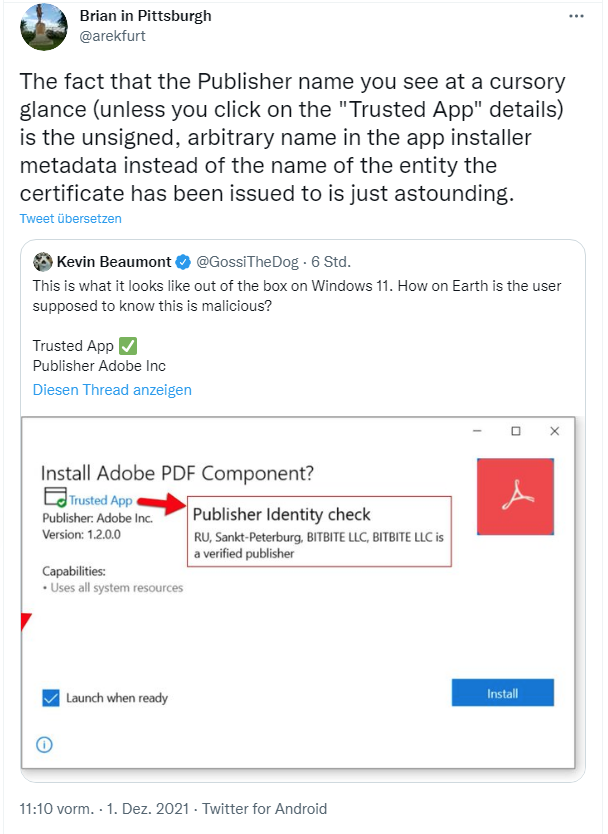
The Emotet team is taking advantage of this security loophole to distribute its dropper that will install ransomware as a trusted Windows application.
As early as December 14, 2021, security researcher Will Dormann tweeted that ms-appinstaller's URI had been blocked by Microsoft with an update.
Note that as of today's updates (CVE-2021-43890), the ms-appinstaller: URI has been disabled. pic.twitter.com/tk9KpmHCy8
- Will Dormann (@wdormann) December 14, 2021
Dormann posted the issue in a series of tweets from December 1, 2021. If Windows users were logged in as administrators, it could be abused because ms-appinstaller: is a URL protocol through which the install AppX from almost anywhere. Even opening a Microsoft document Office it was enough.
Dormann then recommended activating the "Prevent non-administrators from installing packaged Windows applications" policy group or disabling the ms-appinstaller via the reg file for all users.
Do your users log in as administrators? No? Good!
Set the "Prevent non-admin users from installing packaged Windows apps" group policy to avoid foot-shooting.
Do they log in as admins? Interesting choice...
Maybe unregister ms-appinstaller for EACH user.https://t.co/kttJZfRgEX pic.twitter.com/QiYg8XhlPM- Will Dormann (@wdormann) December 2, 2021
But as of December 14, 2021, Microsoft published it σελίδα security Windows AppX Installer Spoofing Vulnerability CVE-2021-43890, which confirms all of the above and discloses the CVE.
Microsoft is aware of attacks that attempt to exploit this vulnerability with specially designed packages containing the Emotet / Trickbot / Bazaloader malware.
In addition, Microsoft has updated the AppX Installer (Desktop Installer):
- Microsoft Desktop Installer 1.16 for Windows 10 version 1809 or later
- Microsoft Desktop Installer 1.11 for Windows 10 version 1709 or Windows 10 version 1803





