A new dangerous version of it ZeuS Banking Trojan identified by it has been recognized by Comodo AV labs. The new variant is signed by a stolen Digital Certificate owned by a Microsoft Developer, to avoid detection by Web browsers and anti-virus systems.
Every Windows PC recognizes and accepts software that is signed with Microsoft's authenticated digital certificates, an extremely sensitive encryption stamp.
Cyber criminals somehow managed to grab a valid Microsoft digital certificate, and they use it to trick users. Malicious software comes digitally signed by Microsoft, so no security tool can recognize it.
Digital signature malware is starting to circulate more and more frequently than last year. In accordance with THN, more than 200.000 unique malware was discovered over the last two years and found to have a valid digital signature.
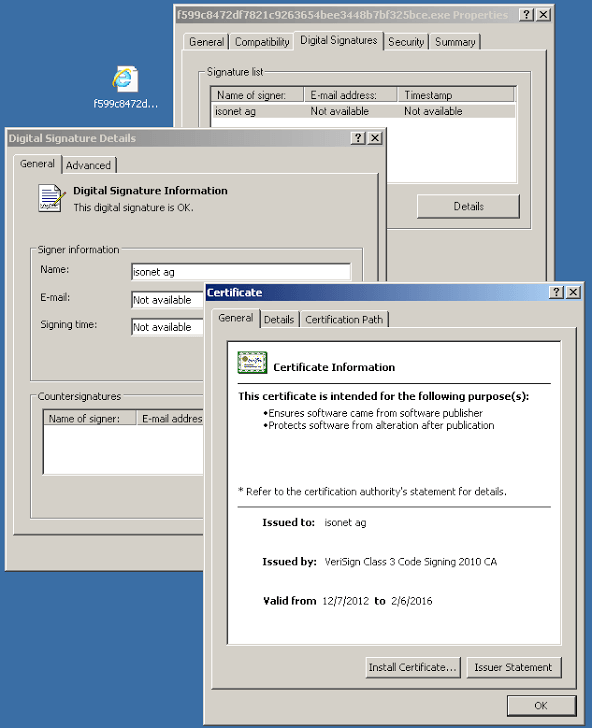
Comodo reports that one of the malware he was trying to trick is trying to cheat the user as an Internet Explorer file. The malicious file had a valid signature that was issued for "isonet ag."
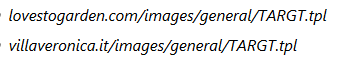
When the malicious file is installed (of course not detected by protection programs) it tries to download rootkit:
ZeuS Banking Trojan is one of the oldest malware, but this new advanced version of Zeus Trojan is protected by a Microsoft digital signature. This makes it much easier to fool users and anti-virus.
Τυπικά, το ZeuS malware εκτελεί μια επίθεση Man-In -Browser ( MitB ) που επιτρέπει στον hacker intercept the victim's credentials (usernames and passwords to bank accounts). .
“Αν το θύμα συνδεθεί σε ένα online banking site για να εκτελέσει κάποια συναλλαγή, όπως μεταφορά κεφαλαίων, δεν θα δει τίποτα περίεργο, όλα θα είναι όπως είναι συνήθως. Οι information όμως που θα πληκτρολογήσει θα είναι ορατές και στους hackers” εξήγησαν οι ερευνητές.
Three components of Zeus are needed to launch an attack:
Downloader: Once the malware is installed by someone online vulnerability or from an attachment that comes with an email, it will download the rootkit and malware.
Malware: It is the thief who will steal the valuables data του χρήστη, τα στοιχεία connections, credit card information, etc
Rootkit: It will hide the installed malware by protecting it from detection and removal. The rootkit is installed by decrypting the file in the "Boot Bus Extender", so it will load before each driver and this makes it difficult to remove it.