A ransomware group has started posting ads on Facebook to force victims to pay a ransom.

Their story attacks ransomware first started in 2012, when techies were surprised to see a new form of extortion, where hackers encrypt their victims' files and then demand a ransom to give them a decryption key.
In November 2019, it was adopted by ransomware groups a new strategy of double blackmail with which they copy the victims' files before encrypting them. The attackers then threatened to share the stolen files in public if the ransom for the decryption was not paid.
Since then, ransomware groups have contacted the media to report on their latest accomplishments in an effort to pressure victims to pay.
Yesterday, the ransomware groups behind Ragnar Locker they took it to the next level by hacking an account responsible for Facebook ads and created ads promoting their attack on the Campari Group.
Last week, the Italian company beverage company Campari Group suffered a Ragnar Locker ransomware attack, where attackers claim to have stolen 2 TB of unencrypted files before encrypting their network. To recover their files, the hackers demanded a ransom of 15 million dollars.
Such as first mentioned by Brian Krebs, ransomware Ragnar Locker hacked into a Facebook account to run ads warning Campari that their data would be published if they did not pay the ransom.
This Facebook ad was titled "Campari Group Network Security Breach" by the "Ragnar_Locker Group" and warned that further sensitive data would be released.
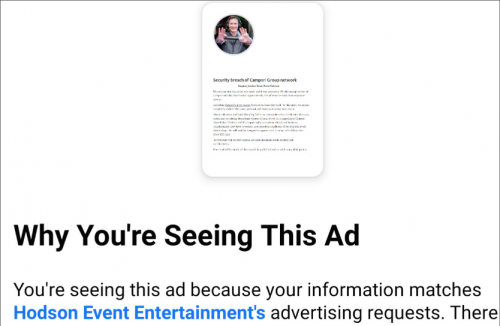
Chris Hodson, the owner of the Facebook account, told Brian Krebs that the ad was shown to more than 7.000 Facebook users before Facebook identified it as an attack.
Ransomware teams have long threatened to escalate their blackmail attempts by communicating with stock exchanges, major media outlets and other large clients.
This new attack tactic via Facebook shows the continued evolution of ransomware. With ransom demands and payments in the tens millions, we can expect to see further escalations in the future.





