In 2014, a data breach exposed details of three billion Yahoo users. In 2016, its employees Sony Pictures saw their sensitive personal information leaked along with thousands of company documents. What do these two attacks have in common? Both started with a phishing email.
"Email threats are still one of the most common ways for cybercriminals to gain access to sensitive information or install malware," warns Roman Cuprik from the global digital security firm's team ESET. Most known phishing cases target anonymous users, but it's not uncommon for attacks to target very specific people who handle sensitive information. And, as ESET researchers point out, in 2022, this type of threats saw an annual increase of almost 30%.
As AI language models make it easier to write emails, chances are these numbers will increase!
Phishing attacks are a form of social engineering that prompts us to react with a sense of urgency and curiosity. While we can all fall victim to this type of attack, we can also learn to avoid it. Let's take a look at some examples of the most common phishing attacks used to trick us.
- "Your session has ended. Click here to log in again.”
In one of the most common phishing tactics, scammers simply tell you that you've logged out of a account and prompt you to fill in your credentials. Clicking on the link will take you to a website that looks very much like the real thing. The difference, however, is that once you put in your credentials these will be immediately sent to cybercriminals, who will then use them to gain access to your information. In some cases, they may even log into your account and change your password.
This technique is based on the habit of users to automatically respond to such messages without thinking about the content or without checking for typical signs of a phishing message.
For example, last year GitHub Security warned about emails pretending to come from the popular CI/CD software development platform CircleCI. Scammers would send a “session timed out” notification and ask you to log in again using your GitHub credentials. “We noticed some unusual activity on your account. Please verify”.
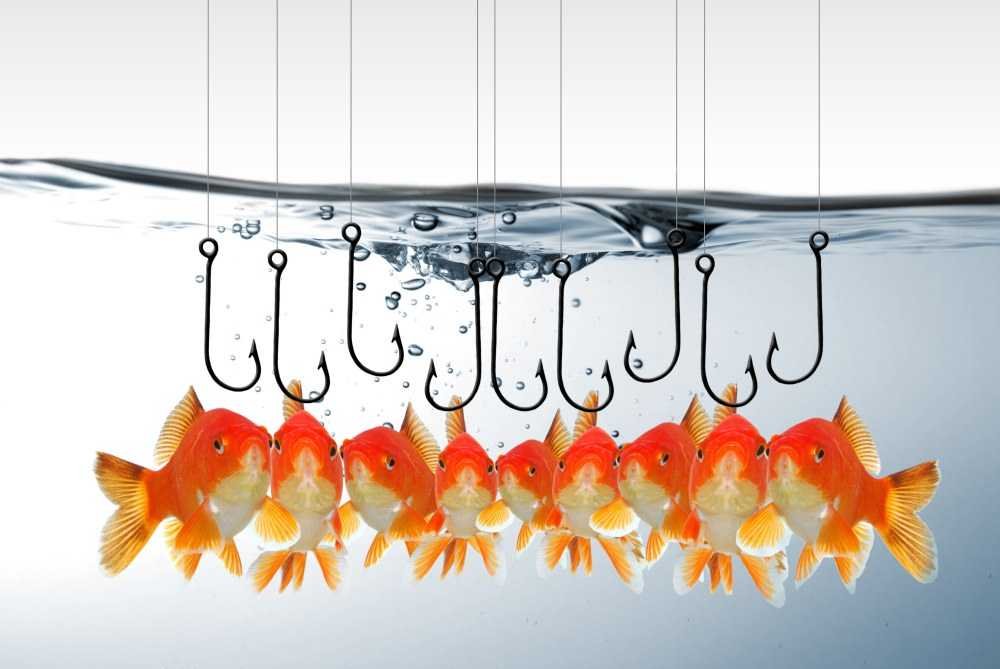
With this ploy, cybercriminals try to create a sense of urgency. Who wouldn't want to avoid suddenly losing an account? Usually, these emails copy messages from legitimate services such as Amazon, PayPal, etc.
For example, in late 2018, the United States Federal Trade Commission (FTC) issued a warning regarding phishing emails that appeared to be sent by Netflix. These emails claimed that an account was put on hold due to some error with payment information, asking users to update their billing information using an embedded link, which was of course malicious and used to obtain login credentials.
Similarly, the Apple customers were targeted in 2016, when scammers tried to steal their personal information with phishing emails that claimed users needed to reconfirm their account information because "a virus" had allegedly been found in Apple's iTunes database.
-
“You must make payment immediately”
Impersonating corporate email accounts has long been the champion among spearphishing campaigns that target a specific individual or group of employees at a selected company.
Before sending these fake emails, scammers learn as much as possible about company structures, details, jargon, etc. of a business so that the phishing email is indistinguishable from a genuine one.
Some of these emails are specifically addressed to employees who are responsible for managing cash and financial matters. Cybercriminals pretend to be the CEO or someone higher up who is authorized to instruct the transfer of money and ask the victim to send money to a specific account, supposedly belonging to the CEO or the company.
In 2018, CEO impersonation was used to theft over C$100.000 from the City of Ottawa. The city treasurer received a fake email from someone pretending to be the city manager, requesting to transfer the amount of money that ended up in the scammers' pockets.
The greedy scammers even tried to trick the cashier a second time, but when they sent a second email the scam was exposed and they were caught in the act.
-
"Dear candidate..."
These phishing emails are based on fake job offers. They can trick potential victims into clicking on a link or opening malicious files sent along with an email, asking the victim to, for example, create an account and pass their personal information to apply for a job.
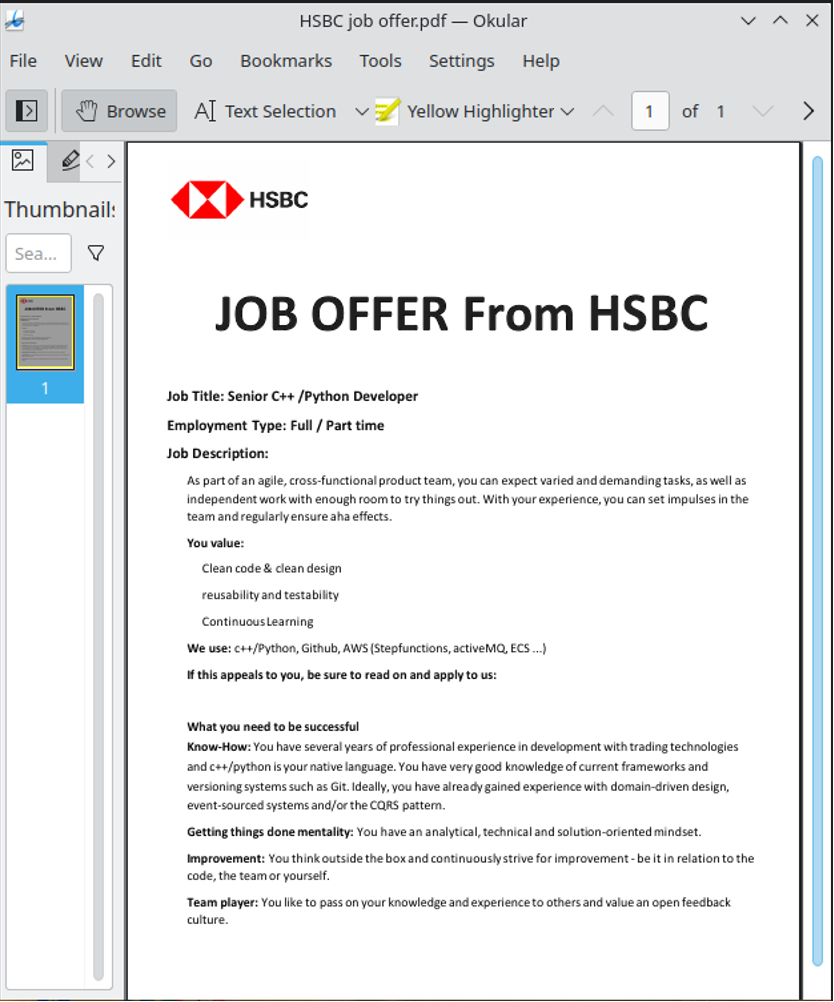
For example, the Lazarus threat group has conducted several such campaigns, such as Operation DreamJob, which was discovered by ESET researchers just recently, which lured its victims with fake job offers.
Such scams also exist on popular job boards, so always try to verify that the boss who contacted you or the job offer you see is legitimate.
The campaign targeted Linux users with a ZIP file delivering a fake HSBC job offer as bait
-
“Due to the current situation…”
Phishing also increases during major events – be it sporting events or a humanitarian crisis. For example, in early 2023, the Fancy Bear threat group organized an email campaign related to the war in Ukraine. The emails carried a malicious RTF file titled “Nuclear Terrorism A Very Real Threat”. Once someone opened the file it would compromise the computer.
-
"Merry Christmas!"
Holiday scams often take advantage of the shopping season. Emails contain offers that are "too good to be true" or create a false sense of urgency to grab a last minute opportunity!
Another approach for scammers is to send emails with malicious files related to the holidays, such as Christmas cards, gift certificates, etc.
-
"We can't process your tax return"
Only a few things in this world are certain – death, taxes and phishing emails during tax filing season. Because people file their tax returns, it's no surprise that they will receive an email from the IRS.
Fraudsters abuse this situation by sending fake IRS emails. Usually, they claim that some information is missing and ask for additional personal or financial information.
Other emails offer refunds, while asking for credit card information.
-
No response required
Some phishing emails have little to no content, tricking you into opening an attachment to learn more about the subject.
For example, the ESET Research uncovered a malicious campaign in 2021 that targeted corporate networks in Spanish-speaking countries using short emails with PDF attachments.
The subject of the email can be as simple as in this case: “Dublin Services Statement” - there was no message other than a signature and a cell phone contact in Venezuela.
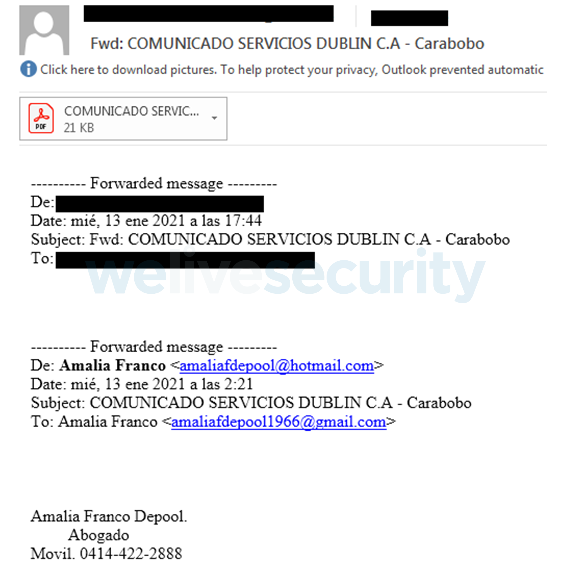
Example of malicious Email
Meanwhile, the attached file is a simple PDF file with no important content, but it contained a link that redirects victims to cloud storage services, from which the malware can be downloaded.
How to protect yourself from phishing emails
According to Cuprik from ESET these are the 8 key steps you can take to keep phishing attacks at bay:
- Please read the email carefully. Don't click on automatic.
- Check if the email address matches the real domain.
- Be wary of unexpected e-mails from a bank, supplier or any other organization.
- Check for "red flags," such as urgent or threatening emails that require an immediate response or requests for credentials, personal and financial information. Grammatical errors, spelling errors, and typographical errors are also clues.
- Compare the attached URL with the corresponding domain of a legitimate company or organization. If you see something suspicious, don't click on it.
- Watch out for deals that are too good to be true and unexpected gifts.
- Don't send money in a hurry. If your superior suddenly asks for such a transfer, contact him immediately.
- Install a cybersecurity product with built-in anti-phishing tools.
Phishing emails are a widespread threat and even IT professionals can fall victim to this scam. Fortunately, most of these emails are fairly easy to spot if you control the urge to click on links or open attachments before confirming who the sender is.