US health agencies account for the bulk of their target victims Trojan Stegoloader, a malicious malware that incorporates its code into archives PNG images, in an attempt to avoid detection mechanisms at the network and host level.
According to security experts, the largest number of infections is found in North America, affecting entities in various sectors, including financial, construction and technology businesses as well as oil and gas companies.
The Trojan Stegoloader, recently reported by Dell SecureWorks, is also known as Gatak. Its architecture is modular, which means its functionality can be extended to be used on a case-by-case basis according to the objectives of cyber criminals.
The technique used by the creators of Trojan is called segregation, and is commonly used in malware to update configuration files, or even to deliver malware. Although this method is not new, it is not widespread as an attack technique.
Another tactic used by trojan authors to avoid its detection is to run the malicious modules in its memory computer. The PNG image, or the code extracted from it and decrypted, is not stored on the hard disk, leaves no trace of contamination on the storage drive, and escapes detection by analysisof the disk signature (disk signature).
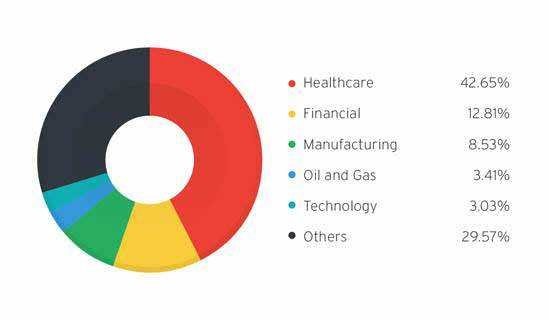
According telemetry data of Trend Micro, 42,65% of Trojan Stegoloader victims come from the healthcare sector, followed by financial sector organizations with 12,81%.
Homer Pacag, a security engineer at Trend Micro, believes that steganography can be used creatively in the future by cybercriminals exploring new ways to attacks against healthcare providers for the purpose of intercepting medical data.