Shrug: A new form of ransomware is distributed through drive-by attacks, but malware contains bugs in its encoding. Below we will see how you can retrieve your locked files for free.
Shrug ransomware first appeared on July 6 and is embedded in fake software and game applications. Those who download such an application also acquire the malicious file that locks their files.
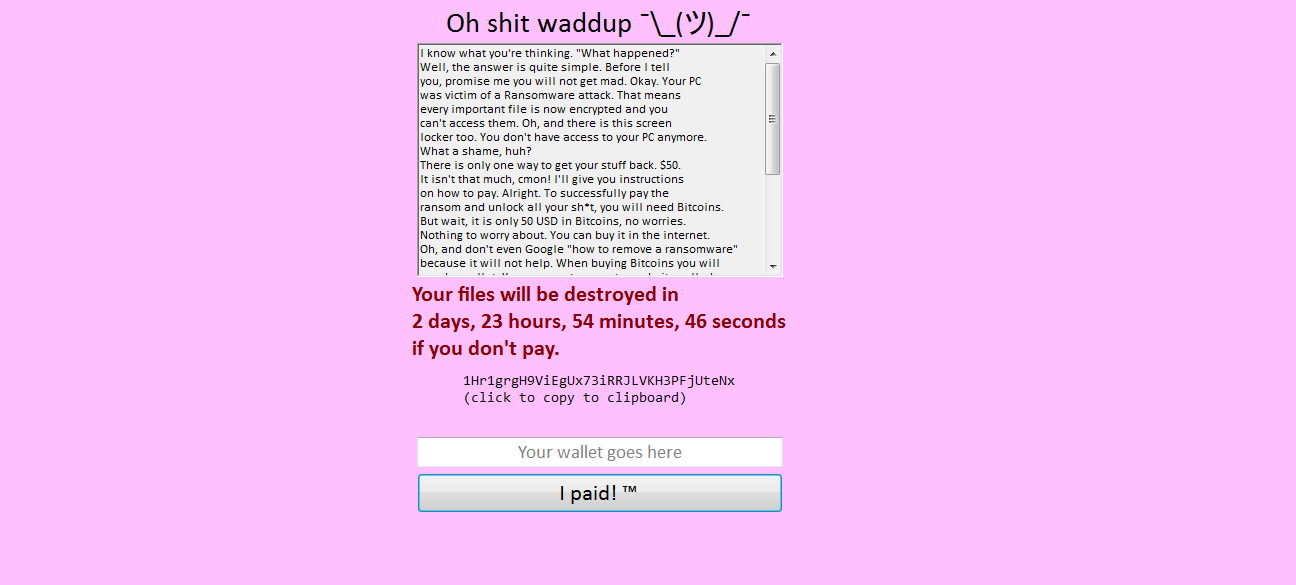
The ransom note reads:
I know what you think, What happened? The answer is very simple. Before I tell you, promise you that you will not go crazy.
Like other ransomware, the note also includes instructions on how to buy and transfer Bitcoin, as well as a threat that all files will be destroyed altogether in three days unless the ransom is paid. Encrypted files are locked with an .SHRUG extension.
Shrug uses a random sequence of keys for each user, but the researchers of security company LMNTRIX, found that the creators of the ransomware left the keys they needed to unlock the files in a folder, allowing their victims to retrieve their files without paying the ransom. Keys found embedded in the registry, encrypted.
To decrypt your files infected by Shrug ransomware, you should reboot the infected machine to terminate the process that the ransomware uses to lock the mouse and keyboard.
After that, you will need to open File Explorer to go to the installation path of Shrug ransomware:
C: \ Users \ USERNAME \ AppData \ Local \ Temp \ shrug.exe
Delete the file shrug.exe file by pressing Shift and Delete together.
Then open the RUN application by typing "RUN" in the Windows search. Then type "Regedit" to open the registry.
Follow the route:
HKEY_CURRENT_USER \ Software \Microsoft\Windows\CurrentVersion\Run
Find it key titled "Shrug", and delete it. Then clean the recycle bin, and restart your machine and the ransomware will disappear.
Shrug indicates that it is possible to build ransomware from criminals who do not have the necessary skills to do it effectively.
The low value of the ransom may also suggest that the attackers were not so sure about their product, which may still be under development.
Malware reminds us once again that we need to download software only from trusted sources.
___________________
- Windows 10 April: Have you lost your desktop?
- Kaspersky Lab: Yes we have collected NSA files
- Dark Patterns: How they mislead the wrong privacy options
- Task Manager which applications consume more power?
- 600 mining servers made wings: cost 2 million dollars





