The SQLi-Hunter is a simple HTTP server, with a sqlmap api that makes SQLi discovery a very easy task.
Requirements
Ruby:> 2.0.0
sqlmap
Installation
git clone https://github.com/sqlmapproject/sqlmap.git
git clone https://github.com/zt2/sqli-hunter.git
cd sqli-hunter
gem install bundle
bundle install
Use
SQLMAP API wrapper by ztz (github.com/zt2)
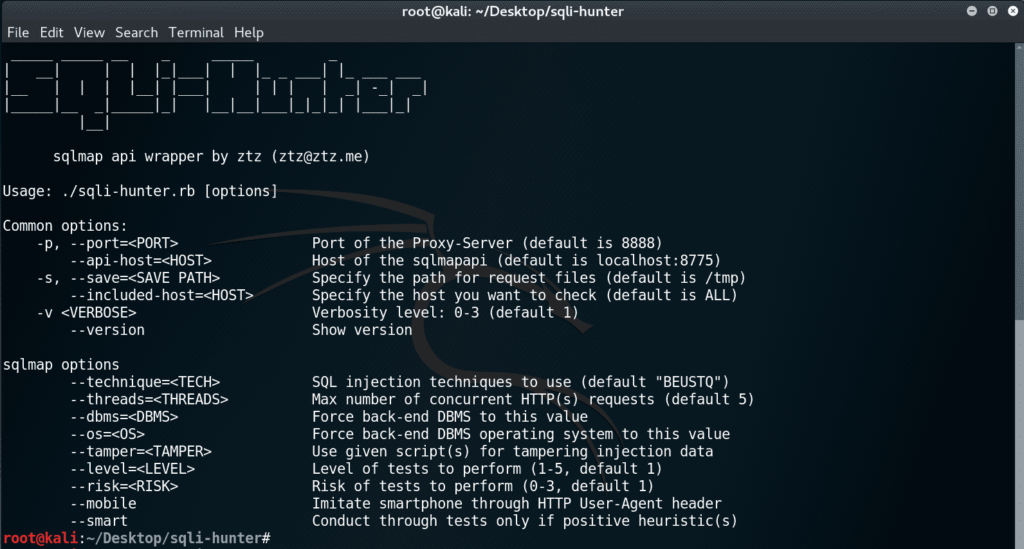
Usage: bin / sqli-hunter.rb [options]
Common options:
-h, –host = [HOST] Bind host for proxy server (default is localhost)
-p, –port = Bind port for proxy server (default is 8080)
–Sqlmap-host = [HOST] Host for sqlmap api (default is localhost)
–Sqlmap-port = [PORT] Port for sqlmap api (default is 8775)
–Targeted-hosts = [HOSTS] Targeted hosts split by comma (default is all)
-version Display version
SQLMAP options
–Technique = [TECH] SQL injection techniques to use (default “BEUSTQ”)
–Threads = [THREADS] Max number of competing HTTP (s) requests (default 5)
–Dbms = [DBMS] Force back-end DBMS to this value
–os=[OS] Force back-end DBMS operating system to this value
–Tamper = [TAMPER] Use given script (s) for tampering injection data
–Level = [LEVEL] Level of tests to perform (1-5, default 1)
–Risk = [RISK] Risk of tests to perform (0-3, default 1)
–Mobile Imitate smartphone via HTTP User-Agent header
–Smart Conduct through tests only if positive heuristic (s)
–Random-agent Use randomly selected HTTP User-Agent header value
Results:
➜ sqli-hunter git: (master) ruby bin / sqli-hunter.rb –targeted-hosts = demo.aisec.cn –threads = 15 –random-agent –smart
[01:50:17] [INFO] [bdf9f3495bb70fbc] task created
[01:50:17] [INFO] [bdf9f3495bb70fbc] task started
[01:50:20] [INFO] [bdf9f3495bb70fbc] task finished
[01:50:20][SUCCESS] [bdf9f3495bb70fbc] task vulnerable, use ‘sqlmap -r /var/folders/kb/rwf8j7051x71q4flc_s39wzm0000gn/T/d20191021-40013-17a62ve/5f8a3ad452a15777219b8a5c8c7ec3b6' to exploit
You can download the program from here.





