Oί hackers behind TrickBot cybercrime have released the XNUMXth version of the malware, with additional features to evade detection.
TrickBot is usually installed via phishing emails or other malware. Once installed, TrickBot will run silently on the victim's computer while simultaneously downloading other modules for implementation different tasks.
These modules perform a wide range of malicious activity, including base stealing data Active Directory Services ενός τομέα , της εξάπλωσης τους σε ένα δίκτυο, του κλειδώματος οθόνης, της κλοπής των cookie και των κωδικών πρόσβασης του προletterbrowsing and stealing OpenSSH keys.
TrickBot is known to complete an attack by giving access to the hackers behind ransomware Ryuk and Conti to make matters worse.
New features added to TrickBot v100
Since the Microsoft and its partners launched a coordinated attack against TrickBot's infrastructure last month, hoping the hackers would take some time to recover.
Unfortunately, the TrickBot gang is still active, as evidenced by the release of the XNUMXth version of its malware.
This latest version was discovered by Vitali Kremez of Advanced Intel, who found that they added new features to make it more difficult to detect.
With this version, TrickBot now inserts its own dll into the legally executable Windows wermgr.exe file (Windows Troubleshooting), directly from memory using code from the "MemoryModule" project.
"MemoryModule is a library that can be used to fully load a DLL from memory - without first saving it to disk," she explains. σελίδα of the MemoryModule project on GitHub.
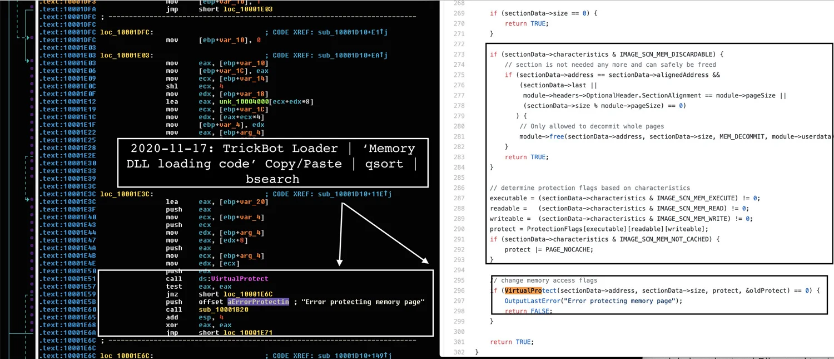
Initially start as an executable file, TrickBot will be inserted into wermgr.exe and then terminate the original TrickBot executable.
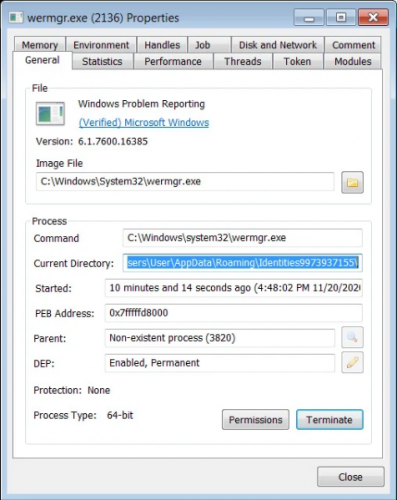
According to Kremez, during the "injection" of DLL, he will do it using Doppel Hollowing or he will edit doppelganging , to avoid detection by security software.
Unfortunately, this means that TrickBot is here to stay in the near future and consumers and businesses need to stay alert and be smart with the email attachments that open.





