A group of academics from Switzerland discovered a bug that could be used to bypass PINs in Visa contactless payments.
This means that if fraudsters get their hands on a stolen Visa card, they can use it to pay dearly productthe, and above the transaction limit without having to enter the card's PIN code.
According to the research team, a successful attack needs four data: (1 + 2) two Android smartphones, (3) a dedicated Android application developed by the research team, and (4) a Visa contactless transaction card.
The Android application is installed on both smartphones, which will act as a card simulator and POS (Point-Of-Sale).
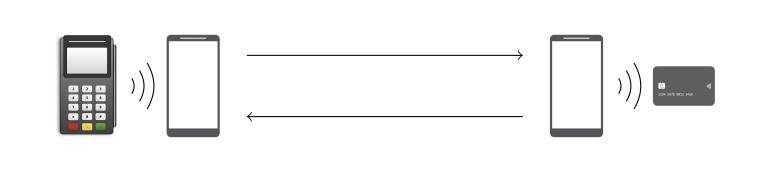
The phone that mimics a POS device is located near the stolen card, while the smartphone that acts as a card simulator is used to pay for goods.
The whole idea behind the attack is that the POS emulator asks the card to make a payment and then sends the modified data over WiFi to the second smartphone that makes the payment without having to provide a PIN (after the attacker has modified the data of cochanges to say no PIN required).
"Our application does not require root privileges or other hacks on Android and we have used it successfully on Pixel and Huawei devices," said the researchers.
https://www.youtube.com/watch?v=JyUsMLxCCt8
At the technical level, the researchers said the attack was possible due to a design flaw in the EMV standard and the Visa contactless payment protocol.
These issues allow an attacker to change the data involved in a contactless payment, along with the fields that controln the details of the transaction and whether the cardholder has been verified or not.
"The cardholder verification method used in a transaction is neither validated nor encrypted and is not protected from modification," the researchers said.
More: https://arxiv.org/pdf/2006.08249.pdf





