Often, in order to hack a website, we need to connect and exploit an object. This can be an administrative panel or a subdirectory that is vulnerable to attacks. The key, of course, is to find these items, as they may be hidden.

DIRB, developed by The Dark Raver, is a tool designed to find these objects, hidden and not. Since it is already included in Kali, if you are working through it there is no need to download and install anything.
Step 1: Open a terminal
The first step, as usual, is to fire up Kali and open a terminal.
Step 2: Eqmovement of the DIRB
Once you open the terminal, type dirb to bring up the help screen.
kali > dirb
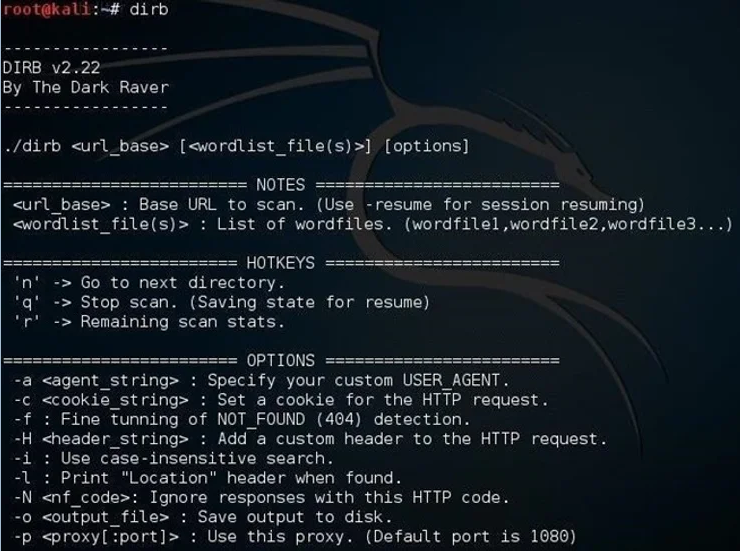
As you can see in the screenshot above, writing DIRB is very simple with many options. In its simplest form, we only need to type the command dirb followed by the URL of the website we are testing.
kali > dirb URL
Step 3: Using DIRB for a simple hidden object scan
In its simplest form, DIRB will scan the site looking for 4.612 object types. Let's test it on our favorite testing site, webscantest.com.
kali > dirb http://webscantest.com
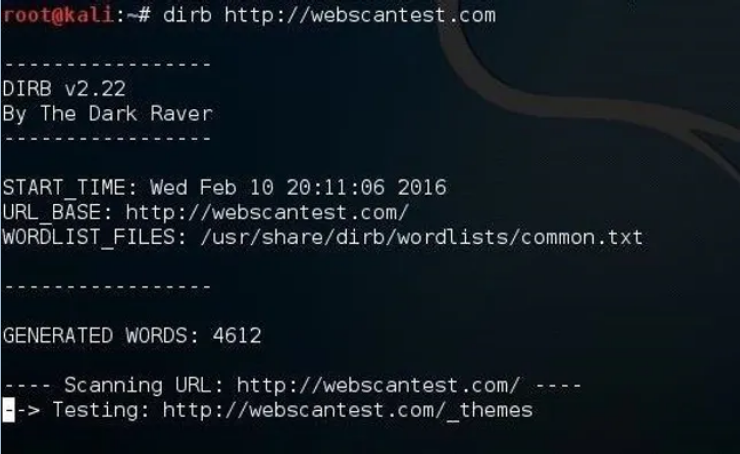
DIRB starts the scan by looking for the keywords among the website objects.
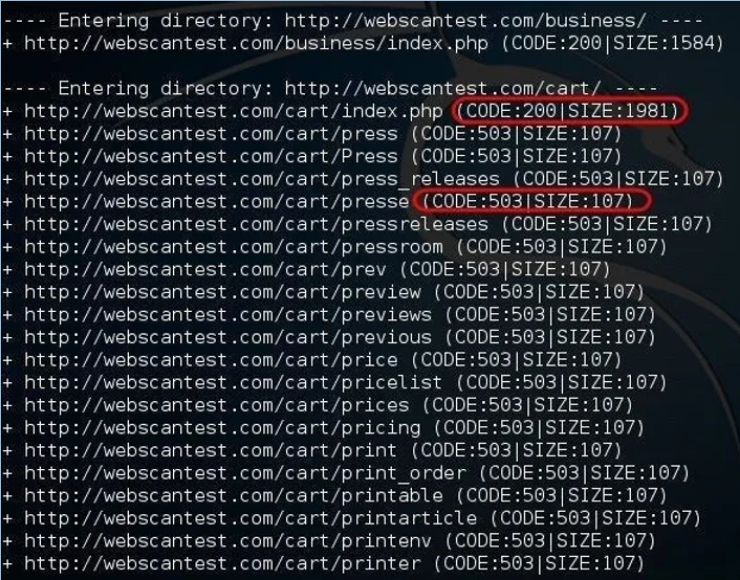
When DIRB finds an active directory (Code 200), it then begins searching within that directory for additional hidden objects. Code 503 indicates “temporarily not available".
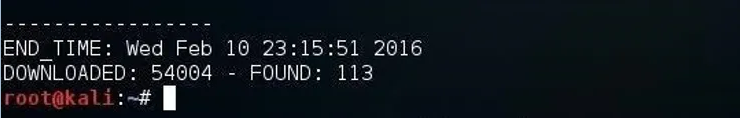
Finally, when DIRB finishes, it reports the number of objects found (113 in this case). Note that in the help screen above, we can use the -o switch to send the results to a archive output to save the results to a text file.
Step 4: Check for special vulnerable lists
We can use DIRB to check for specific vulnerabilities on specific types of websites. Each σελίδα has different vulnerabilities. They are NOT all the same. DIRB can help us look for specific page-specific vulnerabilities.
In Kali, DIRB has specific lists of words to search for these vulnerable, often hidden objects. You can find them at:
kali > cd /usr/share/dirb/wordlists/vuln
Then list the contents of this directory:
kali > ls -l
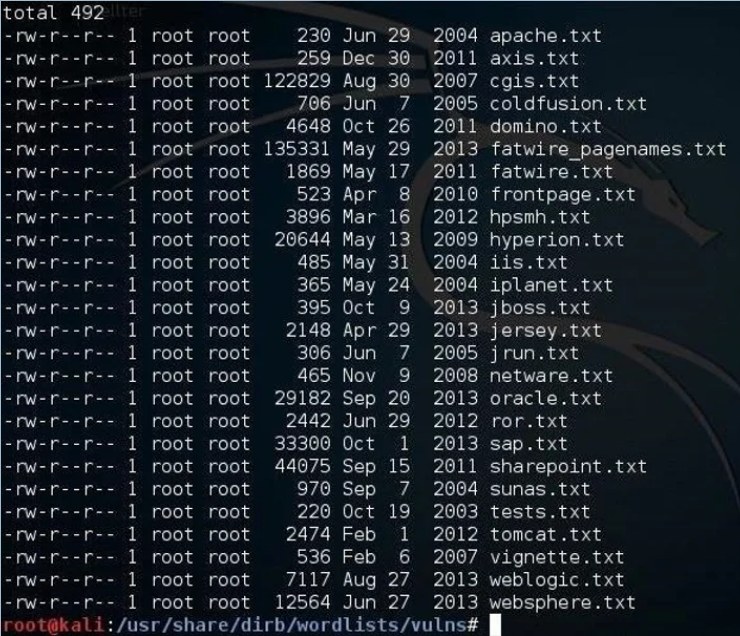
As you can see above, there are numerous wordlists in dirb containing keywords of vulnerable objects for various pages, such as Apache, ColdFusion, FatWire, ISS, JBoss, Oracle, SAP, Tomcat, WebLogic and many others. Since I suspect my site is running Apache as a server (I could do a banner grab or use httprint to make sure), it makes sense to test the apache.txt wordlist first.
We can now create the command dirb us to use Apache's list of vulnerable objects by typing:
kali > dirb http://webscantest.com /usr/share/dirb/wordlists/vulns/apache.txt
When we press enter, DIRB will scan the site for vulnerable objects from the apache.txt wordlist.
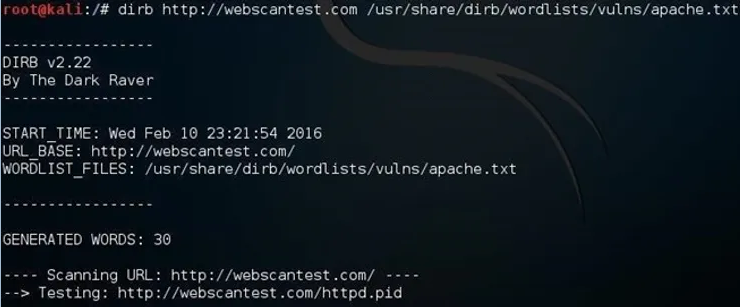
Now, DIRB will use the Apache list to search for known vulnerable objects. If it finds one, then you can take the next step and search for an exploit to exploit in Exploit-DB, Metasploit, SecurityFocus (www.securityfocus.com), or any of the many other exploit sources on the web.
Of course, you must use the vulns word list that is appropriate for the technology used on the site. For example, if it is a Windows IIS server, you should use the iis.txt wordlist.





